PCI-DSS is the most important regulatory framework for companies processing online credit data.
PCI security rules seek to protect cardholder data from data breaches. They apply to any company that handles or stores credit card data. The rules enforce strict penalties for any regulatory violations and guard against damaging data loss. That's why a strong PCI compliance strategy is critically important.
This article will PCI compliance checklist to meet the 12 key PCI requirements. This list will explain each requirement in more depth and help you build security systems that meet regulatory standards. With PCI 4.0 on the horizon, we will also explore the future of PCI compliance and help you create durable solutions to critical data security problems.
12 PCI DSS requirements
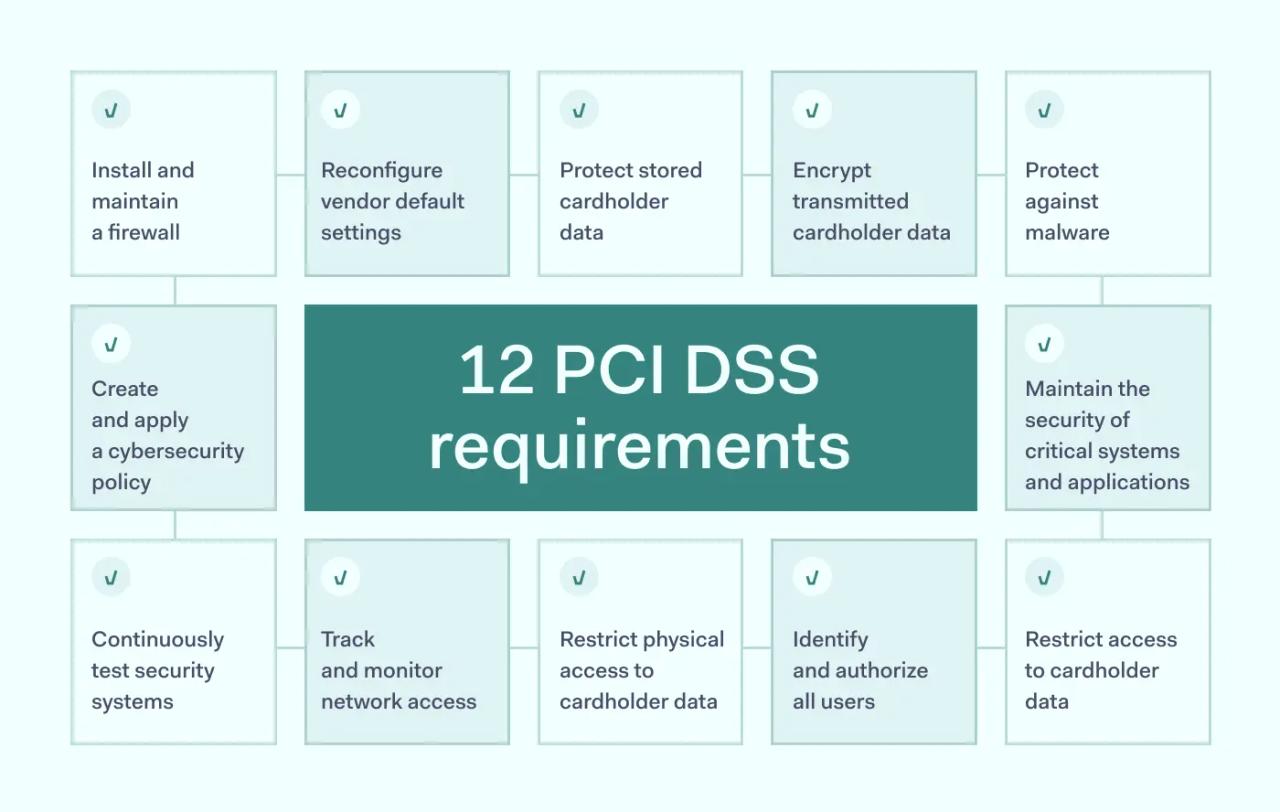
- Install and maintain a firewall
- Reconfigure vendor default settings
- Protect stored cardholder data
- Encrypt transmitted cardholder data
- Protect against malware
- Maintain the security of critical systems and applications
- Restrict access to cardholder data
- Identify and authorize all users
- Restrict physical access to cardholder data
- Track and monitor network access
- Continuously test security systems
- Create and apply a cybersecurity policy
There's more to complying with PCI-DSS than these simple requirements. Check out this introduction to PCI-DSS requirements to learn exactly what the regulatory standards demand.
Why is the PCI compliance checklist important?
This PCI compliance checklist is important because customers expect companies to protect cardholder data. Data breaches are punished by lost business and regulatory penalties. And companies that don't take security seriously will surely lose to organizations that meet PCI requirements.
PCI compliance also requires attention to detail. By following every recommendation in our checklist, organizations can protect both technical and operational systems. And they will also be protected from fines resulting from non-compliance.
PCI DSS compliance checklist
1. Install and maintain a firewall
Firewalls are the first line of defense against external threats. PCI-compliant organizations must apply firewall protection at the network edge.
The network firewall configuration should block unapproved traffic and restrict public access to the cardholder data environment (CDE). All devices connected to the network must fall under firewall protection, with no exceptions.
2. Change default vendor settings
Devices and applications sourced from third-party vendors usually come with default settings. Hackers will often try default passwords, which are publicly accessible and widely known. If hackers compromise a single asset via default passwords, they may gain access to the wider network.
Compliant companies must change all default passwords before deploying assets. System components should have custom configurations that meet network security standards. Access to assets should be protected by encryption and strong passwords.
This also applies to any shared infrastructure or applications. Partners should change default passwords on the server management side. Compliant organizations should double-check that this has been carried out.
3. Protect cardholder data
Protecting the CDE is the most important PCI-DSS compliance task. Organizations must know where cardholder data is flowing. They must record and secure all containers that store cardholder data. And all credit card information must be protected with strong encryption.
Databases containing cardholder data should be separate from the other network resources. Administrators can use their firewall configuration and access control to apply network segmentation. Each segment should be thoroughly tested to ensure data security.
Data retention is another core compliance requirement. Companies should retain cardholder data for the minimum possible duration. Data must be deleted securely. And no data should be collected following credit card authorization. Organizations must mask Payment Account Numbers (PANs) that cannot be encrypted.
Encryption keys also require protection. PCI rules require that keys are encrypted and stored securely.
4. Encrypt cardholder data in transit
Protecting static data is not enough. To meet PCI-DSS compliance requirements, organizations must also transmit cardholder data securely.
Companies should apply strong encryption to all data transfers. They must use approved protocols, such as later versions of TLS. It is important to check that your protocols comply with the most recent PCI-DSS regulations. And PANs should never be transmitted in plain text format.
5. Apply malware protection with antivirus software
Malware is a major attack vector for data breaches. PCI-DSS-compliant organizations must put in place measures to detect, neutralize, and destroy malware before it can cause damage or steal data.
Companies should require the installation of antivirus software on all connected devices. This includes remote devices used by employees working from home, network servers, and office workstations.
Installation of antivirus software is not enough to meet compliance rules. Organizations must update all antivirus software to the latest version. And threat detection tools must generate logs for use in PCI-DSS audits.
Organizations should protect the CDE with threat detection tools. And they must train network users to reduce phishing risks. This includes raising awareness of malicious attachments and the use of external devices.
6. Maintain system and application security
This requirement is focused on risk assessment. Companies must assess the systems they use and highlight any relevant security risks. This involves:
- Identifying potential attack vectors,
- Categorizing the risk level of each asset
- Documenting security controls to mitigate these risks
Risk assessment demands a holistic approach to secure network assets. Security teams must ensure that all assets are updated to reflect emerging threats. Network-wide threat detection systems should guard the entire cardholder data environment. Secure DevOps systems are also essential. This ensures that internally developed assets conform to PCI-DSS standards.
The core aim of this section is to show that an organization has identified core threats and put in place measures to handle them. This requires continuous security assessment and auditing.
7. Restrict access to cardholder data
Access control systems should protect the CDE against unauthorized intruders. Companies should implement Zero Trust principles that limit access on a need-to-know basis. Access should be allowed if users have a business need. If not, access systems should block access and report the issue to security managers.
Companies should put strong authentication systems in place to restrict access to legitimate users. PCI recommends the use of multi-factor authentication (MFA) or two-factor authentication (2FA) systems. Both systems require more than one authentication factor. This makes it much harder for outsiders to gain access.
8. Assign each user with a unique access identity
PCI regulations demand a unique ID for each network user. User activity should be logged and easy to track. Systems must log every access request and session metadata. And this information should be available during audit exercises.
PCI-DSS regulations also require tight control over shared accounts. Organizations should minimize the number of group accounts and document why such accounts are required. Users should be educated about the risks of sharing credentials with co-workers. And security teams should routinely audit access policies to prohibit unsafe access.
9. Restrict physical access to cardholder data
This requirement extends recommendations about digital access controls to physical devices.
Access controls should apply to all devices involved in the CDE. If a device receives, transfers, or stores cardholder information, it should only be accessible to authorized users. This applies to devices that are capable of connecting to the CDE, even if they do not handle credit card data. And it also covers paper assets that store cardholder data.
Companies should put in place physical access controls such as card readers or locks. And they should also monitor physical environments via security cameras. Cameras should record all access points and critical assets.
PCI-DSS rules require the storage of access records for at least 90 days. Records should show who has entered sensitive areas, and there should be individual records for outside visitors.
Physical access controls also apply to mobile devices and storage accessories containing cardholder data. These devices should be secured at all times. And they must be destroyed after use to eliminate the risk of data theft.
10. Track and monitor network access
Organizations must monitor access to the CDE. Systems should record every access request and provide real-time visibility for network administrators.
Access monitoring should feed into comprehensive activity auditing. Compliant organizations must generate audit trails for access requests and any user activities involving cardholder data. There should be separate audit trails for administrative account activity. And security alerts, such as failed access attempts should also be logged.
Security systems must automatically record any changes made to the CDE and associated assets. This includes changes to app configurations and product updates. Systems should record privilege elevations and object creations. And it is important to record any changes to auditing procedures.
Audit data should be stored in secure containers with minimal access for users outside the security team. Data should be stored for at least 3 months in an immediately available format. Information for the past year should be archived in a format that's suitable for annual PCI audits.
11. Regularly test security systems
PCI compliance requires regular network testing at all levels. External and internal network tests should be carried out by an Approved Scanning Vendor (ASV).
Network tests should scan for vulnerabilities such as insecure endpoints. Tests should document any weaknesses. Security teams should record subsequent actions taken to secure network assets.
Annual penetration testing is required at higher PCI levels and is advisable for all compliant organizations. Penetration tests should always follow major system-level changes. They should simulate the main data breach risks.
This requirement can also include the implementation of continuous testing processes. For instance, companies may put in place change detection systems to generate alerts when apps or access controls change. Intrusion detection systems may execute continuous scanning to detect vulnerable system components.
12. Create and implement cybersecurity policies
Documentation is a critical aspect of PCI compliance. Companies must create and implement a network-wide Information Security Policy. This policy includes all of the security controls present on the network and documents how each control relates to PCI compliance.
The information security policy explains how users can safely access sensitive data. It includes details about the organization's incident response plan -- including threat mitigation and system recovery. And it also explains third-party requirements.
Policies should be subject to annual review. Security teams should review whether current systems are capable of countering critical risks. And annual updates should bring policies into line with PCI best practices.
What is the future of PCI compliance?
PCI-DSS regulations constantly change. While the recommendations in our PCI-DSS compliance checklist remain valid, it's important to stay informed as the framework develops.
The Payment Card Industry Security Standards Council regularly updates security frameworks to reflect changes in technology and cybersecurity threats. Small changes can leave companies at risk of regulatory fines. And complying will boost your security posture to avoid the latest threats.
As of July 2023, the most recent PCI-DSS update was PCI-DSS 4.0. PCI-DSS 4.0 was introduced in March 2022. Companies have a two-year interim period when previous security controls remain sufficient. But all regulated entities are expected to conform to PCI-DSS 4.0 standards by March 31, 2024.
Companies may well need to take action to bring their security systems up to date. Important features of the 4.0 PCI-DSS standard include:
- Stricter requirements for the use of multi-factor authentication.
- More flexibility about how organizations can configure payment systems. This includes guidance for contactless payment systems, mobile devices, and tablets.
- Customization options for cloud-hosted business platforms.
- Specific controls to prevent code injection attacks.
- Increased use of Designated Entities Supplemental Validation (DESV) testing for larger organizations.
- Deprecation of SSL and earlier versions of TLS transfer protocols.
- General requirements to view security as a continuous challenge, with evidence of ongoing compliance action.
This will not lead to revolutionary change in the way organizations secure their cardholder data environments. And you should still use our checklist to guide security strategies. But it's always advisable to assess current compliance rules and compare your systems to PCI recommendations.
Conclusion: ensure PCI-DSS compliance with our checklist tool
PCI compliance reduces the risk of data breaches, protects cardholder data, and limits exposure to regulatory fines. All companies handling credit card information must meet PCI-DSS standards. And our checklist provides a simple roadmap to achieve compliance. Follow each step and implement the required controls. But always remember that PCI requirements change. So stay alert and adapt your strategy when necessary.