Since the arrival of cloud computing, the security needs of digital businesses have increased significantly. Older access control methods have become obsolete, leaving systems at risk. The complexity and cost of managing legacy, on-premise Identity and Access Management (IAM) drive the shift towards modern cloud-based IAM architecture. But how should you do it? Let's outline IAM best practices to make it easy and avoid data breaches.
Identity and Access Management overview
Identity and Access Management refers to the tools we use to police access to network resources at the perimeter and inside the network edge.
Modern IAM systems manage two key aspects: identity, which includes authentication and managing entry points into the network, and access, which involves setting specific user privileges and determining how freely users can move within network resources
IAM aims to enable users to access the resources they require while preventing unauthorized access to the rest of the network. It often functions alongside Zero Trust Network Access policies, ensuring compliance with industry-specific security regulations.
Modern IAM solutions can adapt as network perimeters change, scale to meet new demands, and reduce the threat surface available to cyber attackers when implemented well. However, mistakes can lead to inefficiency, extra costs, and more worryingly, gaping security vulnerabilities.
Fortunately, there are plenty of ways to implement cloud and hybrid-based IAM best practices that blend convenience and security.
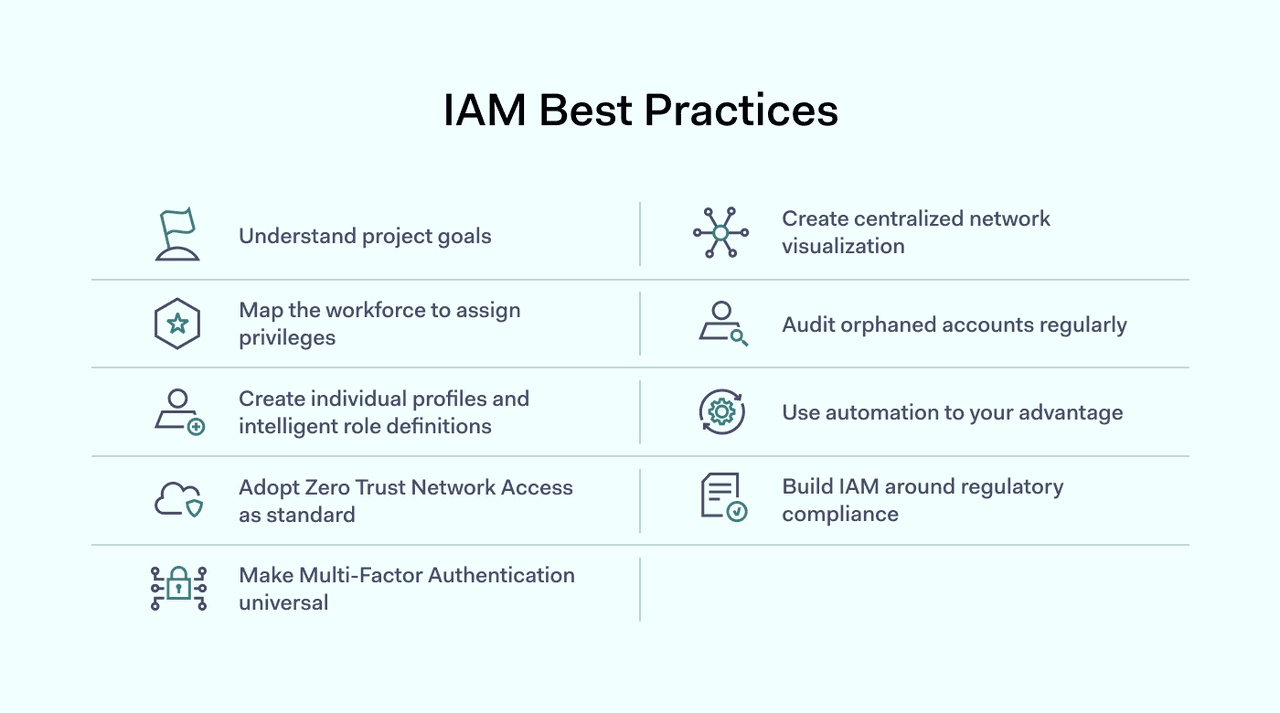
9 Identity and Access Management best practices
Efficient IAM depends on clear goals, smart privilege mapping, and adopting a Zero-Trust approach. Automation, regular audits, and compliance are key to a robust system.
We have gathered nine essential steps to help you implement secure, streamlined access across your organization.
- Understand project goals
- Map the workforce to assign privileges
- Create individual profiles and intelligent role definitions
- Adopt Zero Trust Network Access as standard
- Make multi-factor authentication universal
- Create a centralized network visualization
- Audit orphaned accounts regularly
- Use automation to your advantage
- Build IAM around regulatory compliance
- Implement adaptive access control
- Train your team on security protocols
Now, let's take a closer look at these IAM best practices to understand how they can be implemented.
1. Understand project goals
First, it's essential to visualize the endpoint of your IAM project. There are myriad reasons to implement Identity and Access Management.
Customer service teams could be overwhelmed by requests to reset passwords. There could be concerns about potential and existing threats from phishing or internal sabotage, while security audits may have exposed security risks like excessive user permissions.
Consider which resources your identity solution will cover. Do you rely on cloud-based applications or a blend of bare metal, remote devices, and the cloud?
Understand what problems IAM seeks to solve and make those solutions the central focus of your project strategy.
2. Map the workforce to assign privileges
When embarking on an identity security project, defining who needs access to what resources is vital. Consult HR to build a picture of every role and individual inside the organization, and contractors or freelancers who require secure access.
At the same time, establish ongoing relationships between security and HR teams to enable constant revisions to privileges as employees arrive, leave the company, or change their roles.
Creating an inventory of connected apps, databases, and devices may also be necessary to act as a basis for granting privileges. This inventory creation exercise can double up as an audit to catch any legacy equipment or software upgrades before changing any access processes.
3. Create individual profiles and intelligent role definitions
Everyone accessing your network should have a profile stating their specific access privileges. Avoid granting broad rights to entire departments or contractor groups because this creates vulnerabilities—if one account gets compromised, it can open access to sensitive data for unauthorized users.
Instead, adopt a detailed, user-specific approach to privileged access management. Each user's profile should clearly describe their responsibilities and the exact resources they can access. Detailed role definitions also simplify regular security audits, allowing IT to spot suspicious activity or overly permissive access quickly.
However, manually updating access privileges for every employee change can quickly overwhelm your IT team. To streamline the process, use role-based access control (RBAC). With RBAC, roles are predefined with specific permissions and assigned to individuals based on their job function.
4. Adopt Zero Trust Network Access as standard
The Zero Trust model is widely considered the best practice standard for managing user privileges and protecting your network. Unlike traditional security, which assumes internal users are automatically trustworthy, ZTNA treats every user, whether a new hire, a contractor, or even the CEO, as potentially risky until proven otherwise. Access is granted strictly on a verified, need-to-know basis, greatly reducing the risk of breaches.
At the core of ZTNA is the principle of least privilege. Users receive only the minimum level of access necessary for their tasks. For example, a developer doesn't need broad access to financial data, just as HR shouldn't automatically access engineering codebases.
Regularly reviewing permissions ensures access stays aligned with each user's current role. If someone changes departments or responsibilities, permissions should be adjusted accordingly.
5. Make multi-factor authentication universal
Authentication is a core aspect of identity and access management best practices. Never rely on passwords alone for data security; instead, integrate a form of multi-factor authentication into user access portals.
MFA involves requesting one or more additional credentials before granting access. These credentials could include biometrics, codes sent via SMS or email, or even authentication via social media accounts. Third-party multi or two-factor authentication providers can integrate seamlessly into access management systems, adding an extra layer of protection.
It may also be worthwhile to consider abandoning passwords altogether, as password-free access is increasingly common. If this isn't a viable option, include strong password security practices in your IAM system at every stage.
6. Create a centralized network visualization
Robust IAM implementations provide complete visibility for network managers. They need to be able to monitor every endpoint and every user who connects to the network, alongside activity within the perimeter, including cloud and bare-metal devices.
Visibility is critical in complex organizations with multiple cloud databases or core apps. For instance, a company may need to integrate eCommerce APIs, customer identity, and access management (CIAM) systems with corporate accounts and HR. Cloud access management solutions, including customer identity and access management solutions, will generally be the right fit in these situations.
Ensure that the centralized IAM system connects every user's device, location, and department. Centralization makes real-time user access monitoring more effective and enables smooth onboarding and management of orphaned accounts.
Additionally, be sure to employ single sign-on (SSO) practices wherever possible. Users should have a single data access point using a single set of credentials.
7. Audit orphaned accounts regularly
When employees leave your company, their access credentials often remain active unless proactively managed. These “orphaned” accounts pose significant risks—they’re prime targets for cybercriminals using social engineering, credential stuffing, or insider threat tactics.
Regular auditing of orphaned accounts is essential to identifying and eliminating these potential vulnerabilities quickly. Set up routine checks to identify accounts associated with former employees, temporary contractors, or partners no longer affiliated with your company. Automation tools can greatly simplify this process, ensuring no accounts slip through unnoticed.
In addition to routine checks, it's good practice to integrate orphaned account management into your standard offboarding processes. When someone leaves or changes roles, immediately revoke unnecessary permissions or disable accounts entirely.
8. Use automation to your advantage
Implementing employee or customer onboarding functions can radically reduce the cost and labor associated with IAM best practices.
Pre-assigned roles can smoothly integrate new employees into network security protocols, and security staff usually do not need to tailor individual access privileges during onboarding.
Automate ongoing password management, too. For instance, self-service password portals can reduce the workload on security teams while prompting employees to improve their password security.
The same applies to offboarding, where automation can help handle problems regarding orphaned accounts. However, regularly assess automated processes, as roles will need updating to reflect changing circumstances.
9. Build IAM around regulatory compliance
Managing access is a core component of modern cybersecurity standards, and a robust IAM implementation will contribute toward effective compliance.
Access control applies whether you are seeking to satisfy compliance regulations like the EU's General Data Protection Regulation (GDPR), the Health Insurance Portability and Accountability Act (HIPAA), or the Payment Card Industry Data Security Standard (PCI-DSS).
Factor compliance into your plans from the beginning, and ensure that sector-specific rules fully cover you. Compliance isn't just a legal issue. It's also an excellent focal point for project managers to concentrate and a way to build trust with partners or customers.
10. Implement adaptive access control
Static rules for access control aren't always enough to handle modern threats. That's where adaptive access control comes in. Think of it as a smart security system that adjusts access permissions in real-time based on context. Instead of granting access based only on a user's role, this approach considers factors like their location, the device they're using, and even the time of day. If an employee who normally works from the office suddenly tries to log in from a different country at 3 AM, the system can automatically require extra verification or limit their access.
This dynamic method significantly strengthens your security by applying the principle of least privilege with greater precision. It ensures users get the access they need, but only under conditions that are considered safe.
By continuously evaluating risk factors for each access request, you can prevent potential breaches before they happen, making your security more responsive and resilient to unusual or suspicious activity.
11. Train your team on security protocols
Your technology and policies are only as strong as the people who use them. That's why regular employee training is a critical piece of any effective access control strategy. Even the most advanced system can be undermined by simple human error. By educating your team, you turn your employees from a potential weak link into your first line of defense. Training should cover the fundamentals of your company's security policies, with a special focus on the "why" behind the rules.
Explain concepts like the principle of least privilege in simple terms, so employees understand why their access permissions are limited to only what they need for their specific job. This helps them recognize and report when they might have excessive access.
Furthermore, a solid access control education program should teach them how to spot phishing attempts, use strong passwords, and understand their role in protecting company data. When your team understands the importance of these practices, they become active participants in keeping the organization secure.
Identity and Access Management risks in business
IAM projects can fail in many ways, and it's crucial to assess core risks before commencing any access management overhaul.
- Management buy-in. Executives need to be on board at every stage. Ideally, the process should have an executive champion who can secure funding and staff resources or force through required structural or cultural changes to business processes.
- Stakeholder engagement. IAM should never be seen narrowly as a security challenge. Visualizing the process as enterprise-wide, considering the needs of different users and departments is essential. Communication is also important. Ensure the project's goals are communicated to all key stakeholders and made clear across the organization.
- Procurement. Incorrect technology sourcing can hinder the implementation of IAM best practices at the beginning. While it is necessary to rely on the technical expertise of security teams, procurement decisions should take a broader perspective. Integrate expert advice as required, but assess the business's needs and compare different products before making any decisions.
- Scale and strategy. IAM systems can fail over time, especially when unexpected changes happen. Access management systems must grow with the company and work well with third-party contractors. Also, they should be flexible to work with new technology and not be too rigid.
- Policies and people. Access management is an ongoing human challenge as much as a technical exercise. It is essential to listen to different departments and individuals regarding their access needs. Are their privileges sufficient? Does IAM compromise its working practices? And it's also vital to create teams to audit access systems to ensure efficiency and security.
- Project drift. As with all IT projects, poor management can delay delivery. Generally speaking, it makes sense to divide the project into smaller segments with short timelines and milestones to map progress.
Conclusion
Implementing IAM best practices isn't optional-it's essential for keeping your network secure. Clear role definitions, Zero Trust, automation, and regular audits help you avoid common mistakes that lead to breaches. Getting IAM right means your data stays safe, your team spends less time fixing issues, and your company can easily meet compliance standards. By following these identity and access management best practices, organizations can build a strong security posture that balances protection with productivity.
