Remote work rarely breaks security through one dramatic “hack.” More often, it breaks because remote access gets treated like an on/off switch: connect once, then roam. That’s how traditional security models turn a single compromised account or device into broad network exposure.
Zero Trust Network Access (ZTNA) has changed the security model for remote access. It uses access control built around users and devices, then grants secure access to applications rather than access to the network.
What is ZTNA?
ZTNA (Zero Trust Network Access) is an access control approach that verifies authorized users and their devices before it grants access to applications and data. It checks identity and other context (like location or risk signals), then applies granular access control to specific resources.
Instead of trusting someone because they “made it onto the network,” ZTNA treats every access request as a fresh decision. Access to applications stays scoped, monitored, and easier to revoke when something changes.
Key takeaways
- Zero Trust Network Access assumes trust is earned per request, not granted by default — inside or outside the network
- ZTNA limits access to applications (including private apps) instead of exposing the internal network
- Policies can factor in users and devices, device posture, and context to tighten secure access
- ZTNA reduces attack surface and helps prevent lateral movement if a device or account gets compromised
- ZTNA is commonly deployed on its own or as part of SASE/SSE approaches that bundle multiple secure access services
How does ZTNA work?
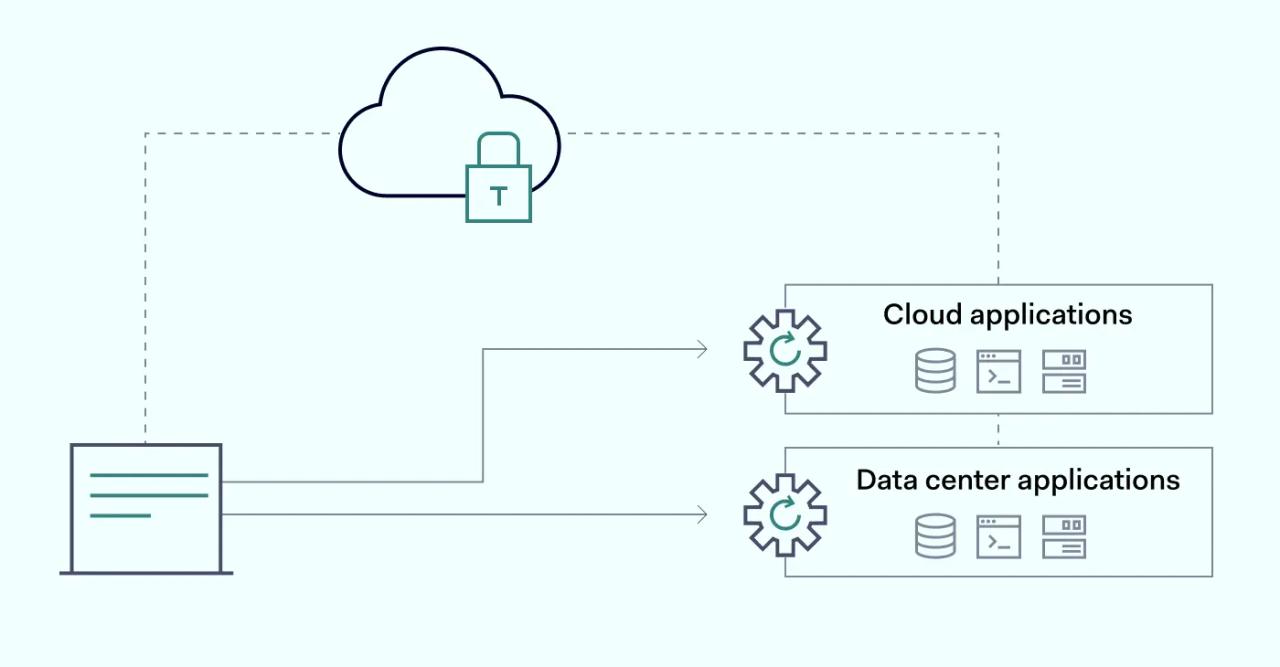
Zero Trust Network Access applies the zero trust security model to secure remote access. Instead of putting users “on the network,” ZTNA brokers access to applications and services after it validates identity and device posture, then enforces policy for that specific session.
That’s the practical gap between ZTNA and many VPN deployments. A VPN often grants network-level access after one successful login, which can expose more resources than a user needs. ZTNA focuses on access to applications, which helps cut the blast radius when something goes wrong.
At its core, Zero Trust Network Access combines two ideas: hide what doesn’t need to be seen, and verify what requests access.
- Application-level access, not network-wide access. ZTNA grants access to specific apps and services instead of dropping users onto the internal network (as many traditional VPN setups do).
- Outbound-initiated access. Apps stay hidden behind outbound connections and aren’t directly reachable from the public internet, which reduces exposed attack surface.
- Least-privilege via network segmentation. Policies and segmentation limit each user (and device) to the minimum set of apps they need, reducing lateral movement risk if an account gets compromised.
- User-to-app control with continuous checks. Access decisions center on identity and context, and can be re-evaluated during a session rather than relying on a one-time “on the network” trust model.
Zero Trust Network Access fits modern remote access because it assumes people, devices, and networks change constantly. That assumption is what traditional security models struggle with.
Benefits of ZTNA
ZTNA supports network growth without handing out blanket access. It can also simplify secure access when apps spread across data centers, multiple clouds, and SaaS platforms.
1. Better network visibility
ZTNA solutions push access to applications through a consistent control point, which means cleaner logs and clearer context. Instead of guessing who reached what, you can track events like access requests, policy decisions, app sign-ins, and session changes.
That level of detail helps network visibility because you see which user, which device posture state, which private app, and which policy allowed a connection.
2. Increased data protection
When a user only gets access to a specific app, damage stays contained. If an account gets compromised, the attacker doesn’t automatically gain broad network traffic visibility or a map of internal resources.
ZTNA solutions also make it harder to turn one foothold into many. Granular access control and segmentation reduce lateral movement options, which helps protect sensitive systems even when something slips.
3. Mitigates remote employee risks
Remote access expands the attack surface fast: home Wi-Fi, hotel networks, personal devices, stale patches, and reused passwords. Traditional security models often treat that mix like a “trusted connection” once the tunnel is up.
Zero Trust Network Access reduces the risk by checking users and devices before access, then tying access to device and policy. If the device fails posture checks (or if signals look wrong) ZTNA can deny access or narrow access to applications immediately.
4. Time-efficient automatizations
ZTNA solutions depend on repeatable policy decisions: who can access what, from which devices, under which conditions. Once you set those rules, access control becomes consistent and less manual.
That consistency cuts the daily overhead of “can you open this port?” and “can you add this network route?” IT teams spend less time babysitting remote access and more time tightening policy and reviewing the events that matter.
Top ZTNA use cases
Zero Trust Network Access helps when you need secure access without exposing the network.
1. Limiting remote access
If you’re looking into how to strike a balance between work-from-home and business network security, ZTNA might be helpful. Zero trust provides access to specific applications without giving too much freedom to roam the internal corporate network.
It’s a much more efficient solution that doesn’t clog up internal bandwidth. Users are connecting directly to where the resources are hosted. Not to mention that application access is denied by default unless the authorized users have passed authentication.
2. Better alternative to VPNs and MPLS
There aren’t many technologies that allow closed-off networking that would be viable in a business setting. For instance, multiprotocol label switching (MPLS) can offer predictable connectivity, but it usually comes with cost and operational complexity. VPNs can be cheaper, but many setups backhaul traffic and expand network exposure in the process.
ZTNA often becomes the middle ground for access to applications: secure access to private apps and internal systems without handing out broad network access. For many teams, that means fewer reasons to stretch VPNs into places they were never meant to cover.
3. Internal network isolation
In a lot of environments, remote access exposes more than a role needs because segmentation is hard to maintain. That turns one compromised device into a springboard for lateral movement.
Zero Trust Network Access supports the principle of least privilege by scoping access to applications per user, per device, and per context. If a data breach starts with one account, ZTNA helps keep it from spreading across the internal network.
Types of ZTNA
ZTNA solutions can focus on different access paths, depending on what you need to protect and connect.
1. ZTNA for access management
This is the most common model: authorized users get secure access to applications through identity checks, device evaluation, and policy. Access control stays granular, and users connect to specific private apps or services rather than to the whole network.
2. ZTNA for resource protection
Some teams extend Zero Trust Network Access concepts to workload communication. Policies restrict which services can talk to which services and help limit lateral movement between workloads, environments, or segments.
3. ZTNA for endpoint security
In hybrid and BYOD environments, device posture signals matter as much as identity. ZTNA can use device health, compliance state, and risk signals to decide whether to allow access to applications, require step-up authentication, or block access entirely.
ZTNA 2.0
“ZTNA 2.0” is a label many vendors use for broader Zero Trust Network Access capabilities. In practice, it usually means tighter continuous checks, richer context, and deeper integrations across secure access services.
In stronger “2.0-style” deployments, access control decisions don’t stop at login. They keep watching signals during the session, and they can change access fast when risk changes, especially when ZTNA runs alongside security services that inspect and control network traffic.
ZTNA 1.0 vs. 2.0
Zero Trust Network Access has evolved in how vendors package and extend it. A useful way to think about it is “typical early focus” vs. “typical expanded focus,” since exact features vary by provider.
ZTNA 1.0 (typical focus) | ZTNA 2.0 (typical focus) |
|---|---|
Access decision mainly at session start | Continuous checks and step-up controls during sessions |
Limited context inputs | Broader context (identity, device posture, risk signals, integrations) |
Strong focus on private apps | Broader coverage (varies by vendor) |
Basic policy enforcement | More granular access control and richer policy options |
Monitoring exists, but can be basic | Deeper visibility and faster response when signals change |
If you evaluate “ZTNA 2.0,” focus on what the product actually enforces: continuous checks, device posture inputs, policy depth, and how it limits attack surface and lateral movement.
How to implement ZTNA?
ZTNA can be implemented using either software on endpoints, connectors near apps, or a mix, depending on your environment and what you need to protect.
Two common connection approaches:
Agent-based (endpoint-initiated) — install a client on the user device. The client sends identity and device posture signals, then requests access based on policy.
Connector/proxy-based (service-initiated) — place a connector near the application (often for private apps). Users connect through a broker that enforces access control without exposing the app directly to the internet.
Two common delivery modes:
Self-managed (standalone) — your team deploys and manages the ZTNA components, policies, and supporting infrastructure.
As-a-service — you consume ZTNA solutions from a provider. The provider runs the service, and your team focuses on identity, device posture sources, policies, and rollout.
ZTNA user flow
Exact steps vary by product, but the access flow usually looks like this:
- A user requests access to an application over a secure channel
- The ZTNA policy engine evaluates identity plus device posture and context
- If checks fail, access is denied. If checks pass, access is granted to that specific application
- The session can trigger extra steps (like multi-factor authentication) based on policy and risk signals
- The system continues to watch signals and can tighten or revoke access if risk changes
ZTNA vs. other technologies
ZTNA often gets compared to VPNs, SASE, firewalls, and CASB because they all touch access and security, but they solve different problems. The main difference comes down to what they protect (network vs. apps), how they grant access, and how much trust they assume after login.
ZTNA vs. VPN
Both ZTNA and VPN support remote access, but they use different security models.
Remote access VPN typically creates a tunnel into a network. Depending on configuration, that can expose internal resources and network traffic paths a user doesn’t need. ZTNA focuses on access to apps and applies granular access control per user, per device posture state, and per policy.
ZTNA can also isolate traffic per app session, which helps reduce lateral movement if a user device becomes compromised. VPNs can be hardened and segmented, but ZTNA starts from the assumption that broad network access is the wrong default.
ZTNA vs. SASE
Secure Access Service Edge (SASE) is a framework that combines networking and security functions delivered from cloud points of presence (PoPs). Many descriptions group components like SD-WAN plus security services such as SWG, CASB, ZTNA, and FWaaS.
In SASE-style deployments, those PoPs sit close to users and enforce access control near the edge. That can simplify remote access because users connect to nearby PoPs for secure access, while policies govern app access across environments.
Using a SASE solution generally means you get ZTNA plus other secure access services in one package, rather than deploying each piece separately.
ZTNA vs. firewall
Firewalls control network traffic based on IPs, ports, protocols, and rules, often at the boundary between networks. They can protect resources, but they don’t always map cleanly to user identity and device posture, especially for remote access across mixed environments.
ZTNA solutions focus on access control for users and devices and tie access to applications directly. That can reduce the need to expose internal services and can reduce the attack surface by keeping private apps less reachable from the public internet.
In many environments, ZTNA and firewalls work together. Firewalls protect network segments and workloads, while ZTNA governs secure app access with granular access control and identity-driven policy.
ZTNA vs. CASB
While ZTNA and CASB (Cloud Access Security Broker) both aim to strengthen security, they approach it in different ways.
ZTNA’s goal is to carefully verify anyone requesting access to protected network resources before granting approval. Through multi-factor authentication and continuous authentication checks, ZTNA confirms someone is who they say they are.
CASB focuses on governance and protection for SaaS usage. It helps enforce policy inside cloud applications: data controls, access policies, and visibility into how users interact with SaaS tools.
Put together, they cover more ground. ZTNA handles secure access paths to applications, while CASB governs what users can do inside cloud apps once access is granted.
Conclusion
If your current remote access model exposes too much of your network, start by listing the apps people actually need. Map each app to a policy that includes identity, device posture, and least-privilege access control, then pilot ZTNA with a small set of private apps before you expand it across the rest of your application access.