Identity and access management is a set of technologies that manage user identities and allow companies to control access to critical resources. The rise of remote working and SaaS tools make cloud-native IAM a popular option to secure networks.
IAM solutions have various components. Single sign-on (SSO) brings together many apps under one login system. Multi-factor authentication (MFA) strengthens access controls. Automation tools make it easier to manage profiles and track user activity.
IAM is proving its worth as an enterprise security and management tool with many potential applications. This glossary article will explain the primary identity and access management basics. We will explore some core challenges users face and quickly discuss whether IAM is the right solution to your access management issues.
Identity and access management benefits
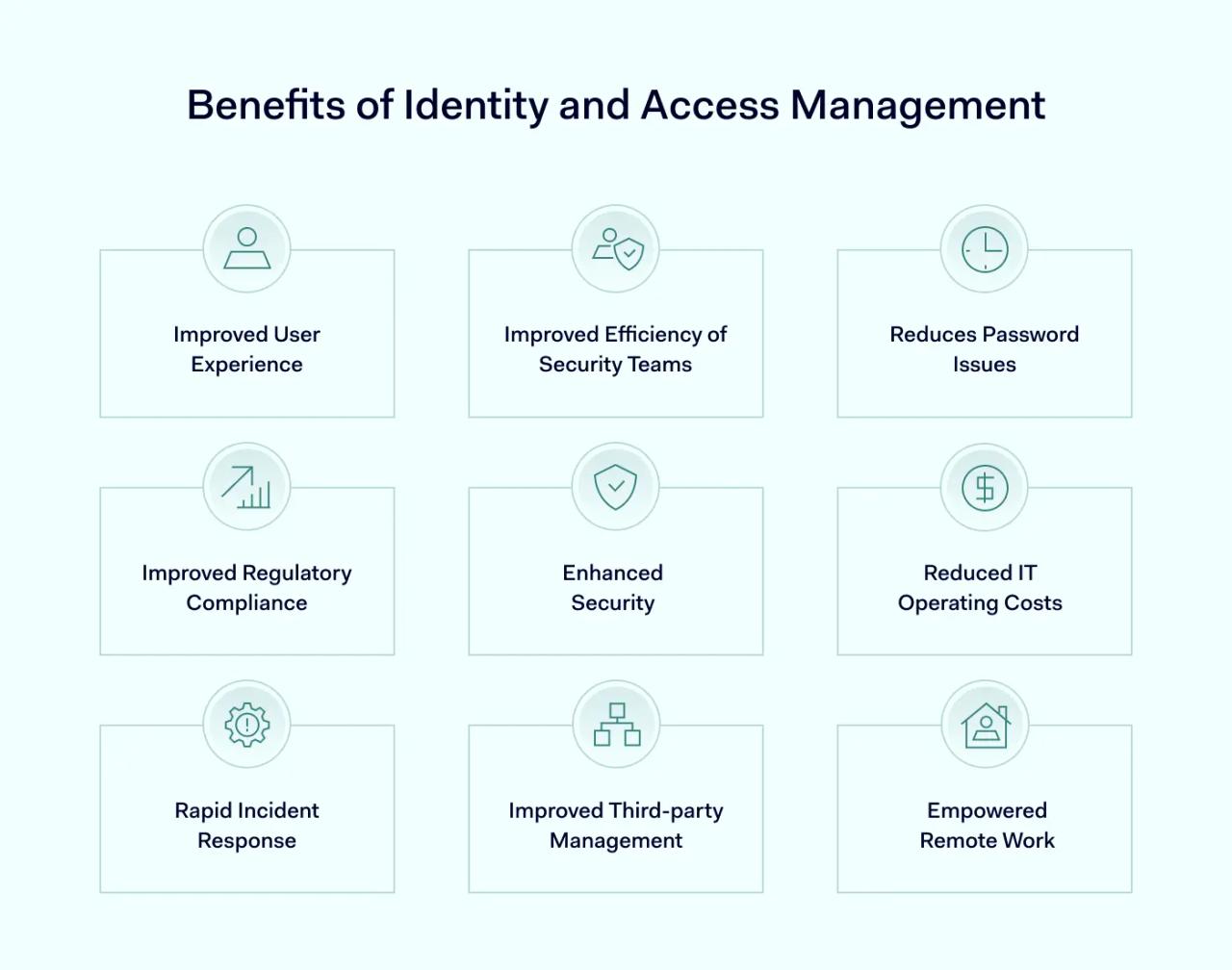
There are plenty of IAM benefits that users need to know about. Benefits include improved security for users and admin staff. But the advantages of IAM go beyond security, extending to information sharing and a more streamlined user experience.
1. Better security for enterprises
The most important identity and access management benefits concern security. IAM improves security on an organizational level, creating strong defenses that are relevant to today's cloud environments.
Access management allows administrators to assign access privileges to specific roles or individuals. This limits users to the resources they need. Everything else remains out of reach and protected. If users with inappropriate access privileges try to access denied resources, the access management system blocks them and reports any suspicious activity.
IAM systems also strengthen the network perimeter. The use of SSO brings all critical resources under a single portal, including cloud and on-premises apps. This access point is protected by standard passwords and multi-factor authentication, creating a double layer of defense.
IAM provides two additional layers of network protection. First when users try to log on, but also when they move throughout a network.
IAM systems also make it possible to enforce security policies consistently across network architecture. Up-to-date user communities cover all devices, apps, and platforms. Identity and access management makes privilege creep far less likely.
Centralized tools make it easier to detect security policy breaches when they occur. Some IAM packages use machine learning to analyze user activity and improve security. Security teams can mitigate proactive risks and improve their overall security posture.
When violations occur, IAM allows admins to revoke privileges as required. Automated user management also reduces the risk of human error when off-boarding accounts or assigning permissions.
Overall, access management systems deliver key security services. They authenticate and authorize users, detect violations, and improve visibility – empowering security teams to achieve more.
2. Reduced operating costs through better resource organization
The cost of managing network access can rise exponentially in hybrid cloud and on-premises environments. IAM solves this problem by bundling diverse assets and creating a single access point.
Federated identity management connects internal user profiles with partner organizations. Managers can share application access across stakeholders without losing control over security. And using a single IAM app reduces the cost of managing complex user communities.
Streamlined password requests also save money. Every time a user requests a fresh password, security teams must verify their identity and find locations where passwords are stored. When you factor in lost productivity as users wait for access, the total cost per lost password is around $70. Automating the process vastly reduces this overhead and speeds up admin procedures as well.
Another cost benefit of IAM is that companies can accelerate their switch to cloud platforms. Cloud-native IAM removes the need for expensive on-premises systems and fits the needs of today's companies more closely.
Finally, a strong IAM setup will reduce the cost of data breaches. When only authorized users can access private data, it is much easier to exclude malicious actors.
3. Robust password management in complex settings
User credentials are a shared network vulnerability. This risk grows as employees have to handle passwords for multiple SaaS services and on-premises portals.
IAM provides a solution. Password management features in IAM packages make it possible to enforce strong passwords and require regular password updates. SSO simplifies the log-in procedure. Employees only need to enter one set of credentials. There is no need to use written reminders or rely on easy-to-remember weak passwords.
When workers forget their credentials, IAM makes it much easier to request password resets. Security admins can automate password requests. This saves time and also encourages users to use stronger passwords.
4. Compliance advantages
Regulations increasingly focus on implementing watertight data security policies. IAM is recognized by multiple regulations as a necessary part of securing sensitive data and achieving regulatory compliance.
A well-designed IAM setup will help companies meet the EU General Data Protection Regulation (GDPR) obligations. It is also a best practice in complying with Sarbanes Oxley (SOX), the Health Insurance Portability and Accountability Act (HIPAA), and PCI-DSS in the credit processing sector.
This makes perfect sense. Access control prevents access to networks by unauthenticated users. Privilege management enables managers to restrict data access and enforce the principle of least privilege. This is a core part of all data compliance strategies.
5. Better user experience for all users
Identity and access management benefits also include user experience improvements.
SSO simplifies user access, allowing employees to use one set of credentials for all assets. Automated password requests save time, while automated privileges management makes requesting access from IT teams unnecessary.
Information sharing is also easier with IAM solutions. Systems like federated identity management make sharing files and data between partners smoother and safer. Users authorized by identity access management can trust that they are genuine and collaborate freely.
IAM systems suit remote user access as well. Users can log in anywhere with any device. Users can access the resources they need if they can prove their digital identity.
6. Time savings across the organization
Organizations are always seeking to work smarter and save time. IAM systems play a role here as well.
Automated identity management takes the human element out of managing user communities. Security admins won't need to spend hours managing passwords, onboarding new hires, or filtering out orphaned accounts.
IAM tools make it easier to audit user privileges and apply changes across cloud environments. Companies can add new services or partners without lengthy administrative processes. And as new services are added to networks, identity management ensures that users won't become burdened by huge lists of passwords.
7. Rapid incident response
IAM systems continuously monitor user activity and permissions, enabling real-time alerts for suspicious behavior.
For instance, let's say an employee who typically accesses files only within regular business hours suddenly attempts to download large volumes of sensitive data at 2 a.m. An advanced IAM system would flag this strange behavior in real time, allowing the IT admin to promptly investigate the matter. Immediate actions can range from temporarily locking down the account to triggering MFA challenges or alerting human supervisors for a quick decision.
This real-time alerting mechanism cuts down on what cybersecurity experts call the dwell time, which is the time that threat actors go undetected within a system. Reducing dwell time is crucial for minimizing the damage and costs associated with security incidents. So, the capability for rapid incident response is not just a nice to have; it's a significant asset in a security toolkit.
8. Vendor and third-party management
Managing external parties like vendors can be a weak link in your cybersecurity chain. Here, the benefits of IAM become particularly evident. With an IAM system, you can implement least privilege access. It essentially gives third parties only the bare minimum permissions they need to perform their role. Think of this as giving a guest a visitor's pass to your office that only opens specific doors.
In this context, exploring Vendor Access Management solutions can be particularly beneficial. These tailored solutions address challenges and security needs when granting access to third-party vendors. Organizations can significantly mitigate associated risks by ensuring that robust access management protocols govern these external entities.
For example, if you're an IT admin working with a third-party marketing agency, you can set permissions so that this group only has access to the marketing folder in your cloud storage and nothing more. You can also set time-based controls, automatically revoking access after completing a project. This way, you reduce the attack surface available to potential bad actors without hampering the third party's ability to complete their work efficiently.
9. Empowered remote work
In the age of remote work, ensuring secure, seamless access to company resources is more crucial than ever.
For an IT admin, this remote capability means fewer headaches. With IAM, you can apply consistent access policies regardless of where an employee is logging in from. Features like MFA can be triggered based on unusual login times or unfamiliar locations. Additionally, SSO features make it easier for remote staff to access various tools without the hassle of remembering multiple passwords.
In a nutshell, IAM systems provide a secure yet flexible framework that supports and enhances remote work's effectiveness.
IAM challenges
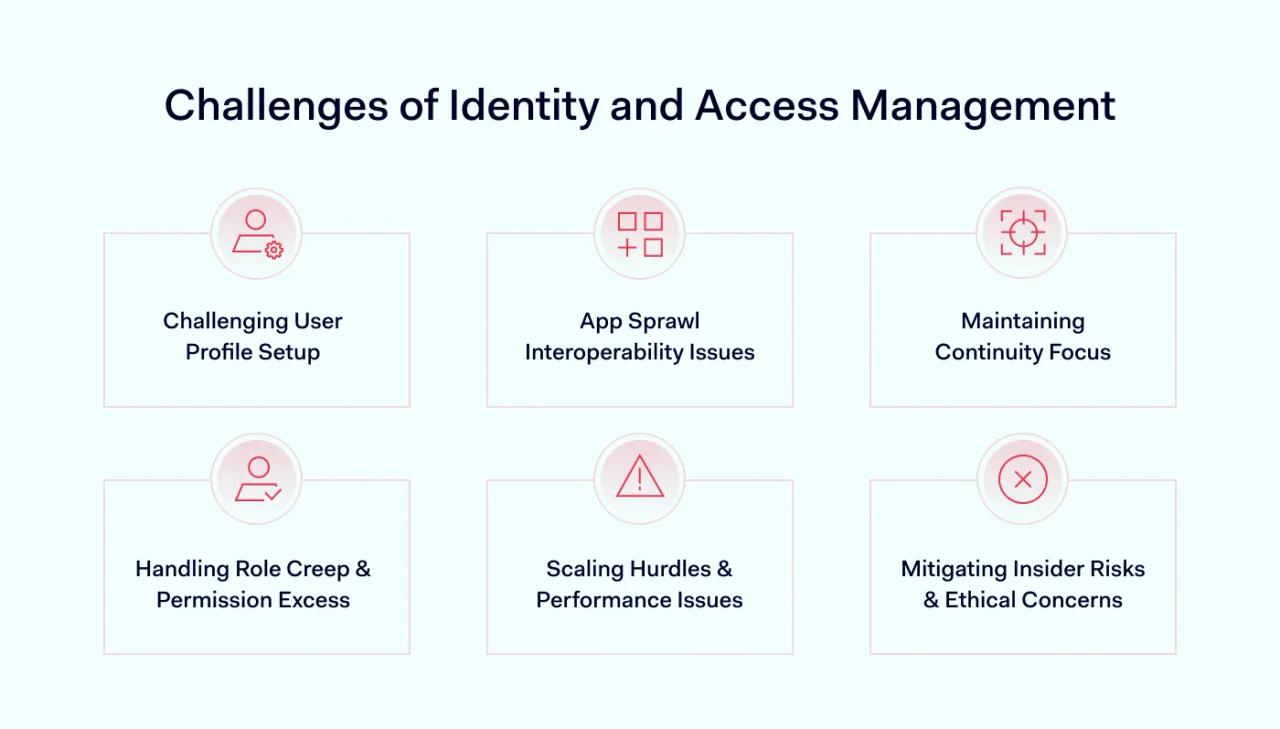
1. Setting up user profiles
Before IAM is operational, security teams must onboard existing users with the right role description, user credentials, and access privileges. This can be a daunting task in large companies, across multiple departments, locations, and even continents.
Matching users and privileges is a complex process. Individuals require access to different cloud resources. This may involve additional permissions, such as content management systems or accounting tools, within a specific application.
Role-based access control tools can help here. The right tools guide security admins as they set up profiles. But, constant testing and vigilance are needed to ensure privileges work correctly.
2. Interoperability and app sprawl
IAM services also have to work with many different network assets. They may need to manage access to on-premises legacy applications, SaaS tools, PaaS suites, and third-party resources. Device identities range from mobile and work-from-home devices to IoT sensors. Getting everything to work together is challenging.
IAM services are designed to provide secure access to existing cloud platforms. But there may still be compatibility issues with individual apps. Your security team needs to ensure that access management systems fit their needs before commissioning any products.
SSO can resolve these problems. With the right single sign-on system, companies can gather all assets together. This makes managing communities of cloud apps much simpler.
3. Continuity – maintaining focus
IAM is not a one-time purchase or technical fix. It is a constantly evolving process that adapts to changing business needs. Security teams need to plan for audits and revisions as events unfold. They cannot rely on automated profile management and SSO to run without regular checks.
Companies need to know that new hires are receiving appropriate privileges. They need to be sure that privileges are accurate and protect sensitive data. And they need assurance that users are de-provisioned when they leave the organization.
4. Role creep and permission glut
In the world of IAM, role creep is akin to the clutter that accumulates in a drawer over time. As employees transition through different roles within an organization, their access permissions can pile up, leading to a condition known as a permission glut.
This isn't just organizational untidiness; it's a security risk. Employees who no longer need sensitive data access may still have it, creating opportunities for accidental or intentional misuse.
Automation tools that can prune these excess permissions exist, but they're not foolproof and often require manual oversight. Consequently, IT admins need to regularly audit and adjust permissions, a task that's easier said than done. This challenge underscores the need for a balanced approach to IAM—one that combines technological solutions with vigilant governance.
5. Scaling hurdles and performance drag
Scaling issues, one of the IAM challenges, often resemble a traffic bottleneck on a growing highway. As an organization expands, the IAM system must accommodate an ever-increasing number of users and applications.
Unfortunately, not all IAM systems are built to scale efficiently. The symptoms of these constraints are often noticeable: authentication processes slow down, leading to delays that frustrate users and put extra pressure on IT staff.
This performance degradation isn't merely an annoyance; it could be a sign that the IAM system is reaching its operational limits. A failure to address these scaling issues could result in broader security vulnerabilities, requiring IT management's tactical and strategic attention to resolve effectively.
6. Insider risks and ethical dilemmas
While external threats often make headlines, risks from within the organization can be just as significant. Employees with elevated access permissions may misuse their powers, either intentionally or inadvertently, posing a complex challenge to manage.
Trust within a team is vital for a functional workplace, but balancing that trust with the need for security oversight is tricky. Constant monitoring can erode employee morale, but lax oversight can lead to security breaches.
Therefore, this challenge demands a carefully calibrated approach combining technology with policies to ensure trust and security coexist. It underscores the need for comprehensive and ongoing training and regular audits to mitigate the risks without compromising the work environment.
Should your business use IAM?
Most likely, yes. Identity and access management is available for large and small enterprises. It is a sound investment for all companies that rely on cloud infrastructure and remote work.
Implementing IAM is complex and requires careful planning. However, as we've seen, access management has many benefits that make the process worthwhile.
IAM services protect critical data and applications from external and internal threats. SSO portals simplify the workload of admins and users. And the overall IAM package helps companies comply with demanding information security regulations. These are crucial functions that would benefit almost any organization.
