Network security protects the boundary between internal and external networks, keeping sensitive data and vital applications safe from unauthorized outsiders. A strong network security infrastructure is essential for any company's overall security. But to create a functional security setup, it's vital to understand why networks are vulnerable and the many threats they face.
What are network security threats?
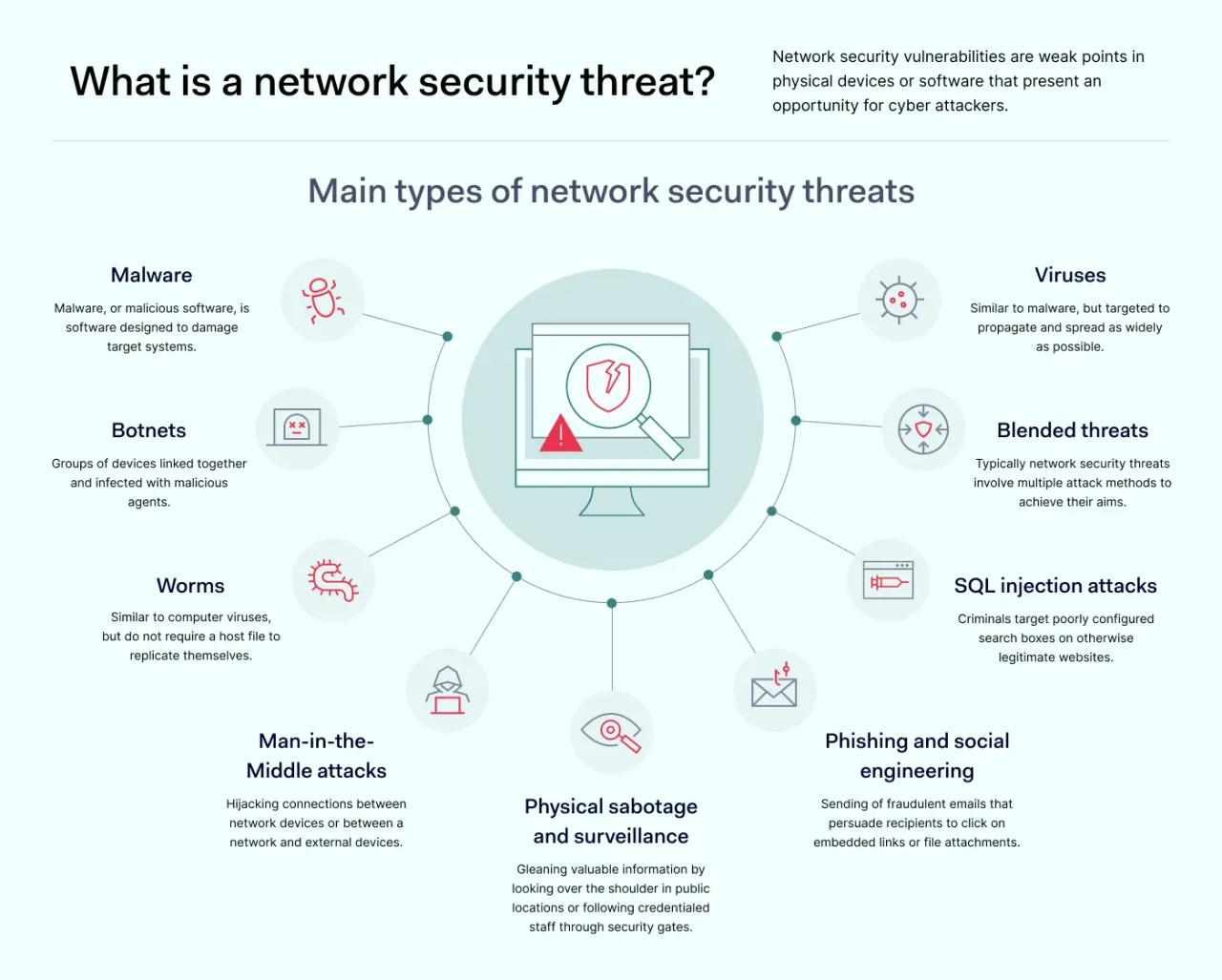
Network security threats are specific attack methods that exploit vulnerabilities – weaknesses in systems, devices, or processes. There are multiple ways to launch such attacks, and all of them should be addressed in network security policies.
Common network security threats include malicious programs, malware, phishing, denial-of-service (DoS), and Man-in-the-Middle (MitM) attacks. These threats succeed by targeting network security vulnerabilities, which are the weak points in physical devices or software that present an opportunity for hackers. These weaknesses can range from poor server monitoring and physical protection to inadequate operating system and antivirus updates.
The common types of network security threats
Malware
Malware, or malicious software, is software designed to damage or disrupt target systems. It is an umbrella term for several types of cyber threats and can have various effects; some versions cause systems to slow down or operations to freeze, while others facilitate data exfiltration.
Most malware attacks result from unauthorized access, human error, and zero-day exploits targeting unpatched applications or operating systems. However, phishing, Man-in-the-Middle attacks, and insecure file sharing are often equally to blame for a system compromise.
1. Keyloggers
Keyloggers log the keystrokes of infected devices. Generally created to steal login credentials and personal information, they usually spread via email attachments or downloadable files on malicious websites.
Some keyloggers also take regular screenshots or hijack the device's camera. In that case, virtual meetings can be compromised, along with other sensitive information.
Keyloggers can be easy to detect when they operate at a surface level, but they can also be installed via rootkits deep inside a device at the kernel level. Deeper-rooted keyloggers are uncommon but more concerning. Simpler versions tend to be vulnerable to standard anti-malware scanners.
2. Trojans
Trojans take their name from the "Trojan Horse" which enabled ancient Greek soldiers to conquer Troy while the residents slept.
Trojans are engineered to appear legitimate, just like the horse. Victims download these apps as usual. When opened, infected apps automatically install malware, leading to various serious consequences.
For instance, banking Trojans harvest financial login details. Backdoor Trojans create routes for attackers to steal information from devices. Mailfinders scan for email contact details, while downloaders constantly download and seed new forms of malware.
The good news about Trojans is that they cannot replicate autonomously. Additionally, if malware scanners find them, they can usually neutralize them quickly.
3. Ransomware
Ransomware is a sophisticated category of cyber threats that holds users and organizations to ransom by locking devices or applications and demanding specific actions before restoring system functionality. These attacks typically demand payment in traditional currency or cryptocurrency; however, payment is no guarantee of recovery. Historically, nearly a quarter of organizations that chose to pay attackers still failed to recover their data. Additionally, according to NordStellar’s research, ransomware surged 45% in 2025, led by Qilin and new groups targeting US manufacturing SMBs.
As with other malware varieties, ransomware spreads via malicious emails, infected websites, and compromised app downloads. Because these attacks often exploit human error or unauthorized access to enter a network, modern security relies heavily on advanced threat detection. These systems are designed to identify and neutralize ransomware behavior in real-time before it can encrypt critical files.
4. Adware
Adware forces victims to see pop-up ads whether they want to or not. Relatively harmless compared to other threats, adware can still be a considerable drain on system resources and a sign that systems are insecure.
5. Spyware
Unlike ransomware, spyware leaves few traces. It keeps a low profile, hiding from anti-malware scanners while gathering potentially useful information.
This information could include device profiles, location data, keystrokes, emails, camera images, contacts, or financial data. Sometimes, information gathered feeds back to adware networks, determining which pop-ups appear. In other cases, data feeds straight to criminals for sale on the dark web or use in phishing attacks.
6. Logic bombs
Logic bombs trigger at a specific time or when a condition has been met. This target could be something completely arbitrary such as sending 500 emails. Or it could be targeted at business operations.
When the trigger point arrives, the logic bomb "explodes". The result could be the release of a worm or virus, with unpredictable consequences.
7. Pharming
Pharming implants software on target devices to exploit DNS protocol vulnerabilities. Attackers can then automatically redirect targeted web users to fake websites or downloads.
Pharming can also directly target unsecured DNS servers – redirecting network users to unsafe destinations.
Viruses
Viruses are similar to malware, but with one difference: they are created specifically to propagate and spread as widely as possible.
Viruses are the most common form of digital threat and can spread in numerous ways. Infected emails, messaging services, website downloads, and even infected USB sticks are all potential vectors.
Most computer viruses require a host file to spread. Unfortunately, this commonly targets popular formats like .doc, .exe, or .xml files – all formats that can appear legitimate when disguised by skilled attackers.
Worms
Worms are similar to computer viruses but do not require a host file to replicate themselves. They can often infiltrate devices without being detected, and when worms infest networks, they are difficult to remove.
Worms generally also spread more quickly than viruses. For instance, they may be designed to exploit a specific security vulnerability in a Windows release. In that case, the worm could replicate automatically from system to system if that vulnerability is present.
Botnets
Botnets are groups of devices infected with malicious agents. These devices are linked together, allowing attackers to control them remotely. Affected devices may not show any noticeable changes. But when used in tandem, thousands of bots can cause havoc on internal networks and the wider internet.
Most importantly, botnets are responsible for crippling Distributed Denial of Service (DDoS) attacks. Controllers often sell their services to attackers via DDoS-for-hire websites. These criminals then mount DDoS attacks, flooding targeted websites with data and potentially destroying their ability to function.
Botnets are closely associated with IoT devices that are often poorly configured, leaving them wide open for attackers.
Phishing and social engineering
Phishing is a deceptive security threat that involves sending fraudulent emails to persuade recipients to click on embedded links or file attachments. This method relies heavily on human error, tricking individuals into bypassing standard security protocols. When a recipient clicks a malicious link, they are redirected to harmful content, which can range from automatic malware downloads to sophisticated fake e-commerce portals designed to steal credentials.
Because it exploits human psychology rather than just software bugs, phishing remains a highly flexible attack method with multiple strategies. Common varieties include:
1. Spear phishing
Phishers create detailed profiles of targets via malware or surveillance and use this information to write emails tailored to that individual.
2. Whaling
Attackers target high-level executives with broad security clearances and valuable contact information.
3. Vishing
Vishing, or voice phishing, uses phone calls or voice messages. Attackers may use voice over Internet Protocol (VoIP) tools to imitate legitimate contacts, persuading targets to hand over sensitive information.
4. Smishing
Attackers use SMS messages in phishing attacks. Attackers closely copy trusted sources and employ carefully chosen urgent language to make targets click embedded links.
5. Spam
The oldest phishing technique on the list. Spamming involves sending large amounts of mail with a low success rate but high value when targets respond.
SQL injection attacks
In SQL injection attacks, attackers exploit input fields on vulnerable websites or applications. By entering malicious code, they can manipulate database queries and access, change, or delete data.
Physical sabotage and surveillance
Network security strategies also need to take into account physical threats. For instance, attackers could employ "shoulder-surfing" techniques, looking over the shoulder of employees in public Wi-Fi locations to glean valuable information.
There have also been examples of tailgating, where attackers gain access to offices and server rooms by following credentialed staff through security gates. Dumpster diving to obtain personal information is even a possibility.
Any information could be valuable to phishers mounting social engineering attacks. Companies should shred documents and use professional waste management partners to minimize the risk of data breaches.
Man-in-the-Middle attacks
MITM attacks occur when attackers hijack connections between network devices or between a network and external devices. By doing so, attackers can eavesdrop on traffic, extracting data transfers and information that can be used in social engineering attacks or sold to third parties.
While they are commonly associated with remote working, MITM attacks can occur in any situation where devices interact via login portals. This makes secure single sign-on (SSO) systems and network encryption essential.
Blended threats
The list of network threats above is highly simplified. In reality, many network security threats involve multiple attack methods to achieve their aims.
For example, the WannaCry attack in 2017 exploited a known vulnerability, ransomware demanding payment, and a worm that sought the same exploit on connected systems. This method spread to hundreds of thousands of systems in just a few days, showing how rapidly global threats can emerge.
Strengthen your network security
Now with 22% off yearly protection plans
How to identify network security threats
Identifying and neutralizing cyber threats is key to ensuring the safety and integrity of your organization's data and operations. Here’re six essential strategies to help you effectively detect and mitigate cybersecurity threats.
From maintaining a vigilant watch over your network to using advanced threat intelligence, these proactive measures will empower your business to stay one step ahead of cyber adversaries.
1. Keep a close eye on your network
Ensure comprehensive visibility into your network's vulnerabilities and potential threats. Adopt the perspective of an attacker to identify weaknesses and fortify your defenses accordingly.
2. Use threat intelligence
Stay informed about prevalent cyber threats and attacks targeting organizations similar to yours. Use threat intelligence to protect your business against threats proactively.
3. Conduct penetration testing
Identify weak points in your defenses through simulated attacks. Penetration testing reveals areas of susceptibility, including vulnerabilities exploited by malicious actors and potential human errors.
4. Implement effective permission management
Enhance security by segmenting your network and meticulously managing user permissions. Limit access to sensitive resources, mitigating the risk of data breaches and insider threats.
5. Fortify your network with firewalls
Deploy robust firewall solutions internally and externally to enforce network security policies. Prevent unauthorized access and monitor network traffic to detect and thwart suspicious activities.
6. Monitor your network constantly
Maintain vigilant oversight of your network's security foundation. Regularly monitor and update security controls to stay ahead ofthreats, ensuring timely detection and response to potential risks.
How to mitigate network security vulnerabilities
To effectively address network security vulnerabilities, understanding the basics of preparation is crucial. Because common network security threats like malware, ransomware, and phishing are constantly evolving, here are several strategies to bolster your network's defenses.
1. Update software as quickly as possible
Zero-day exploits target software vulnerabilities in commonly used operating systems and apps, posing an immediate threat to users. The only way to safeguard your network assets against exploits is by regularly patching software when updates become available. Pay attention to "end-of-ife" dates and ensure employees source updates only from trusted websites.
2. Ensure complete network visibility
Network visibility allows security teams to track user behavior, detecting signs of insider network threats and external infiltration before it becomes a critical danger. Map every device connected to the network, including remote work laptops, smartphones, and other IoT devices. Implement strict access controls and monitoring systems to ensure that only privileged users can reach sensitive data.
3. Secure your perimeter
Install perimeter protections like firewalls and Virtual Private Network (VPN) encryption. A vital component of modern defense is the use of identity management systems such as multi-factor authentication (MFA). By requiring more than just a password, multi-factor authentication significantly reduces the risk of unauthorized access stemming from human error or stolen credentials. Ensuring that every entry point to your network infrastructure is gated by MFA creates a strong barrier against both automated and targeted network threats.
4. Create deep security protection with Software Defined Perimeter (SDP) tools
As the threat surface expands into the cloud, traditional perimeters are less effective. Cloud-adapted network security tools like SDP create encrypted boundaries around every user, following them as they use third-party software, on-premises servers, and remote devices. Under this model, access controls are granular; users can only access resources according to strict permission settings, and network segmentation prevents lateral movement by attackers.
Beyond providing protection, SDP significantly improves advanced threat detection within cloud infrastructure. By centralizing visibility, security teams can monitor user activity with high precision, ensuring that any attempts to bypass access controls or breach security policies are identified and addressed immediately.
5. Focus on physical network security
Companies need policies to detect and neutralize physical threats to network infrastructure and data. Security measures could include surveillance cameras and sensors to protect servers, alongside access management tools like biometric or card scanning.
6. Use antivirus and anti-malware tools
Security teams should equip all network devices with tools to scan for viruses and malware. Security policies should include an authorized set of tools for users to install. These tools should be capable of detecting threats, and staff training should cover how to use them effectively.
7. Train staff to be vigilant
The human side of threat detection is also critical. Staff must be aware of the dangers posed by phishing and social engineering. They should know how to use email safely, and avoid dangerous remote working practices such as using unsecured public wifi or improperly secured mobile devices.
Employees can flag potential phishing strategies or holes in network security, and a well-trained, knowledgeable workforce is a strong guarantee against insider threats.
8. Actively detect disturbed denial-of-service (DDoS) attacks
Disturbed denial-of-service attacks are a major security threat but are relatively simple to detect via packet monitoring tools. Track DNS requests and responses, Transmission Control Protocol (TCP) SYN packets, User Datagram Protocol (UDP), and Internet Control Message Protocol (ICMP) traffic. Sudden spikes in any packet variant should alert security teams to potential attacks.
Because DDoS attacks aim to overwhelm network resources and cause significant downtime, implementing automated mitigation services is essential for maintaining availability. Furthermore, analyzing the source and scale of these DDoS attacks helps organizations refine their firewall rules to prevent similar traffic surges from disrupting operations in the future.
Understand network security threats and minimize vulnerabilities
Every network is vulnerable to cyberattacks and insider threats. A single poorly configured device can bring an entire network down, while the stolen credentials of a single employee can be used to extract millions of dollars’ worth of data. That's why network security is crucial.
Take action to address network vulnerabilities and counter malware, phishing, viruses, and physical network threats. Investment in prevention always outweighs the cost of failure.