Handling patient health data comes with big responsibilities. You need to know where potential dangers hide. HIPAA mandates regular security checks for this data. Keeping it safe isn't just good practice; it's the law.
A HIPAA risk assessment acts like a roadmap. It shows where your protected health information (PHI) lives. It also pinpoints security weak spots needing attention. This guide walks you through creating that essential map.
What is a HIPAA risk assessment?
HIPAA risk assessments identify, classify, and address risks regarding health data and patient confidentiality. A HIPAA risk assessment ensures that covered entities and associates meet the standards set out in HIPAA regulations.
There are two main risk assessment types under HIPAA:
Security Rule risk assessments
The Security Management Process standard in the Security Rule states that risk analysis is mandatory. According to this process, organizations must carry out an “accurate and thorough assessment of the potential risks and vulnerabilities”. And they must safeguard the confidentiality, integrity, and availability of electronic protected health information”.
HIPAA Security Rule risk assessments map the location of Protected Health Information (PHI). They identify security vulnerabilities. And they determine critical risks that require urgent action.
Breach Notification Rule risk assessments
The Breach Notification Rule also requires risk assessments. Assessments are needed when organizations experience data breaches or PHI disclosure. Organizations must assess risks to determine whether the incident is reportable.
This article will focus on executing a HIPAA security risk assessment. Check out our breach notification rule guide for background on responding to security incidents.
Read on for a step-by-step guide for healthcare organizations to follow. And learn everything you need to know to carry out a comprehensive HIPAA risk assessment.
Why are HIPAA risk assessments important?
Most importantly, HIPAA risk assessments are non-negotiable parts of compliance strategies. Organizations that do not identify and address risks will likely face regulatory action from the Department for Health and Human Services (HHS). They will also be liable for penalties from the Office for Civil Rights (OCR).
HIPAA risk assessments play other critical roles in the healthcare sector. Comprehensive risk analysis:
- Maps the location and flow of Protected Health Information through covered entities
- Clarifies the security role of business associates and covered entities
- Protects patient data and cuts the risk of data breaches
- Builds trust between patients and providers. Assessments reassure patients that healthcare organizations understand the importance of addressing risks.
- Helps organizations update their health information technology to meet Security Rule requirements
- Contributes to building a culture of compliance within healthcare organizations
- Allows organizations to respond to breaches when required, saving time and resources
- Cuts the chance of receiving penalties from the Office for Civil Rights
Decide what systems and data to check
HHS does not specify a standard format for a HIPAA risk assessment. Regulators realize that the size and activities of healthcare organizations vary. What works in one context will not work elsewhere. However, in all cases, the goal is to identify and understand risks to PHI or ePHI.
A HIPAA risk assessment will usually have three sections. These sections apply to the majority of organizations:
- Technical safeguards. Organizations must assess the systems used to protect PHI. Controls include encryption, access management tools, firewalls, and threat detection systems. Assessors should identify any weaknesses. Examples could include the need for product updates or credential theft by malicious actors.
- Administrative safeguards. Organizations must assess the integrity and relevance of their policies and procedures. Do policies explain security controls, and are they HIPAA-compliant? Assessors should also verify that employees know their responsibilities and have adequate training.
- Physical safeguards. Organizations must look at physical protections for protected health data. Physical controls include locks on entry points and data storage devices. It covers surveillance systems and alarms. Risk analysis should extend to the physical premises of business associates that store or handle PHI.
In each area, assessors should examine whether security gaps exist. The HIPAA security risk assessment should focus on PHI exposure risks. It should aim to address those risks and prevent regulatory breaches.
How to conduct a HIPAA risk assessment
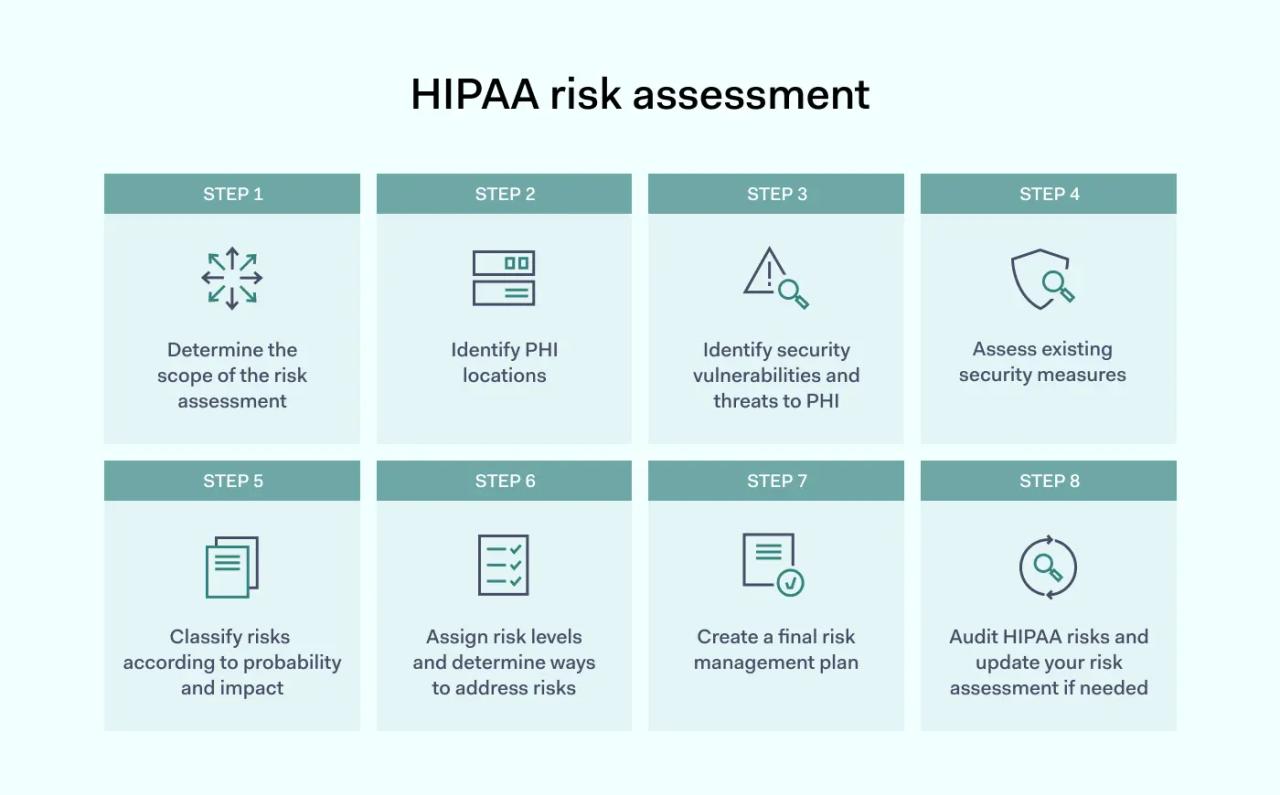
1. Determine the scope of the risk assessment
A HIPAA risk assessment examines systems or processes that deal with creating, using, storing, or disposing of Protected Health Information.
Some organizations must cover all of the areas. For instance, risk assessments by large providers will have broader scope. They must consider patient onboarding and health documentation throughout the patient-provider relationship. And they may have many data storage facilities or third-party business associates.
Other organizations need less extensive risk assessments. For example, a company might supply dental accessories to regional clinics. As a business associate, the company must secure access routes to PHI held by covered entities. Securing these routes is less laborious than assessing risks that large healthcare bodies face.
Take care to determine the scope of analysis. Refer to the HIPAA Security Rule and select assessment areas applicable to your organization. Areas to consider include:
- Which employees or assets have access to PHI
- Where PHI resides and how it is transmitted
- Third parties that may access PHI held on your systems
- Insider threats from employees
- Digital threats and the risk of physical theft
- Policy documents relating to the HIPAA rules
2. Identify PHI locations
When you have determined the scope of the HIPAA risk assessment, the next critical task is identifying PHI locations. Organizations must understand:
- Devices that store or process electronic Protected Health Information
- The location of physical PHI
- Whether PHI flows to and from remote devices used by employees
- How PHI flows through the organization. Include flows of PHI via third-party associates.
The amount of PHI handled by healthcare organizations varies. And not all health information is protected. Be sure to familiarize yourself with what constitutes HIPAA-protected health information. Match this definition with data stored on your servers, workstations, and removable media.
Create a document that maps PHI locations. It may be helpful to consult with employees at this stage. Ask employees how they use and transfer PHI. Their feedback will provide insights into potential risks. It may also uncover unknown devices such as external drives or personal assistants.
3. Identify security vulnerabilities and threats to PHI
When you know the identity and location of PHI, you can complete a HIPAA security risk assessment. Identify potential threats that could compromise stored health data. Threats could include:
- Malware introduced by cyberattacks
- Phishing attacks seeking confidential data
- Physical theft of PHI storage devices
- Unauthorized access to Protected Health Information
- Exposure by improper PHI disposal or device re-use
Remember that the HIPAA Security Rule includes a “reasonable and appropriate” clause. HHS does not expect organizations to apply every possible security control. Identify risks and focus on threats that pose the most risk to PHI.
4. Assess existing security measures
Most covered entities and business associates install cyber-security and physical security systems. The HIPAA security risk assessment process aims to align these existing systems with regulatory requirements.
Document existing security measures. Determine whether these security measures provide sufficient protection against identified threats. Carry out penetration testing or test access controls to verify that controls function as they should.
Technical safeguards to consider when identifying risks include:
- Privileged access management systems. Privileged Access Management assigns privileges needed for users to carry out their duties. They limit access to all other PHI and network assets.
- Multi-factor authentication (MFA). MFA screens access requests. It demands more than one unique identifier before allowing access.
- Encryption. This security measure renders stored data unreadable without the necessary encryption keys.
- Secure key storage. Stores encryption keys in a separate location with robust security protection.
- Firewalls. Screens traffic entering and leaving the network. Allows security teams to set access control lists. Security teams can verify users and exclude unknown actors.
- Intrusion Detection Systems (IDS). Track threats at the network edge. IDS systems identify malware and unknown agents. They neutralize threats and limit damage when attacks occur.
- Data Loss Prevention (DLP). Classifies and protects PHI. Policies determine who can view or edit PHI. Users can only transfer confidential data according to DLP settings.
- Logging and auditing systems. Centralized logging systems store user activity data. They record access requests and changes to PHI. Audit trails enable accurate audits and identify potential threats.
This section of the risk assessment should also cover physical security measures. Organizations must assess whether their physical premises are secure.
- Buildings or rooms holding PHI should have access controls.
- Surveillance cameras should cover areas where employees use or store PHI.
- Alarms should alert security teams if unauthorized individuals enter sensitive areas.
Assessors should also consider administrative safeguards.
- Audit policy libraries. Ensure there are policies for critical security areas like access management and PHI sharing. Document any missing or incomplete policies.
- Check training processes as well. Look for areas where HIPAA compliance is weak. For example, training for new hires may not cover PHI storage and sharing policies. Secure remote working training may be outdated. Record areas where training is insufficient as potential risks.
Check that your organization has these controls in place. The absence of security measures represents a potential risk. Assessors should document that absence and identify potential risks.
5. Classify risks according to probability and impact
At this stage, you should be aware of your PHI-related assets. And you should have a comprehensive record of security vulnerabilities. When you conduct risk assessments, the next stage is risk classification.
HIPAA risk analysis decides critical risks and those requiring less urgent attention. Analysts record criticality by assigning a risk score. Risk scores combine the probability of risks occurring with the impact they have.
Critical risks are very likely to occur. They have a high impact on PHI security. For example, access controls may be inadequate. In this case, the risk of unauthorized individuals accessing ePHI is high. Disclosure of unsecured PHI has a serious impact. The risk score would be very high.
6. Assign risk levels and determine ways to address risks
Document risk classifications for every vulnerability identified earlier in the risk assessment process.
This document is the foundation for your risk management plan. It provides a single point of reference and compiles all assigned risk levels. Compliance teams should easily be able to identify critical unaddressed risks.
Every significant risk should have a mitigation strategy. Match mitigation measures to risks. Assign an individual with the responsibility to address risks.
7. Create a final risk management plan
Combine all administrative, technical, and physical security risks into one document. Document vulnerabilities and risk classifications. Include implementation specifications to address each risk. This document is the basis for a risk management plan.
Your risk management plan should assign responsible individuals to manage risk mitigation. For example, you may recruit a HIPAA security officer to update access controls. Employees from the HR department can help when addressing training issues.
The management plan should include timescales for delivery. Use a green-amber-red color scale to separate addressed and outstanding risks. This color scale will ensure everyone stays focused and on course.
8. Audit HIPAA risks and update your risk assessment if needed
HIPAA risk assessment is not a set-it-and-forget-it exercise. Organizations must audit their risk assessments annually. Compliance officers must check that mitigation measures are functioning correctly. And they must also look for new risks that the original assessment missed.
Employees can backslide. Training may not take root. Policies can become obsolete. And new threats emerge all the time. PHI is never completely secure. Because of this, covered entities and business associates should adopt continuous risk management.
Make a plan to fix the risks you found
Risk management plans turn risk assessments into meaningful action. Managing risks is crucial to remain HIPAA-compliant. And there are several things to consider when creating an ongoing risk management strategy.
- Documentation is critical. Risk assessments must be easy to understand and comprehensive. A newly hired compliance officer should be able to examine a risk management plan and know how to assess HIPAA risks. Create a standard format for assessments, management plans, and HIPAA policies. Store documents in a compliance library so all relevant information is readily available.
- Adopt a proactive attitude. Risk management plans should focus on taking essential action. Compliance teams should identify mitigation measures and complete tasks within tight timescales. But they should not stop there. Organizations should anticipate threats and breaches. The plan should be ready for deployment when a security incident occurs.
- Don’t forget staff training. Risk managers sometimes focus too much on security controls and neglect the human side of HIPAA compliance. Integrate privacy and security training into risk analysis. And audit training systems regularly. Many data breaches and disclosures stem from poor employee behavior. Training is the best way to avoid these situations.
- Schedule access management audits. Access management is another area where vigilance is crucial. Controls can be too broad, allowing excessive access for third parties. Accounts of ex-employees can remain active, posing a security risk. And devices proliferate. Organizations must know who is accessing their network and how they do so. Frequent audits make this possible.
- Test security systems. HIPAA does not require regular penetration testing. But testing security systems is advisable. Penetration tests provide reassurance that security controls are fit for purpose. Regulators also recommend that covered entities include them in their risk management strategies.
FAQ
What is the difference between HIPAA risk analysis and assessment?
In the world of HIPAA, risk analysis and risk assessment have slightly different meanings.
HIPAA regulations refer to risk assessment in connection to the Breach Notification Rule. Organizations must carry out risk assessments following breaches. Assessments determine whether breaches have exposed PHI and whether notification is needed.
Risk analysis relates to Security Rule compliance. Covered entities must analyze risks that compromise the “confidentiality, integrity, and availability” of PHI. A HIPAA risk analysis assesses all security systems. It considers technical, administrative, and physical controls. The aim is to improve PHI protection measures and bring controls into line with HIPAA requirements.
How often do organizations need to execute a HIPAA Risk Assessment?
HIPAA regulations are not specific regarding the frequency of risk assessments. Rules state that organizations must assess risks “as needed” to protect PHI.
In practice, regulations demand continuous assessment. Compliance teams should constantly look for vulnerabilities and compliance weaknesses. And they should update their risk management policies when necessary.
In practice, the frequency depends on the type of organization involved. Organizations that process large amounts of Protected Health Information should carry out risk assessments at least annually. Business associates handling relatively little PHI can update their risk assessments every 2-3 years.
How much does a HIPAA risk assessment cost?
Risk assessment costs vary. Costs will be higher for larger organizations and bodies that process large amounts of PHI. Initial HIPAA risk assessments tend to cost more than updates. This is because first assessments need more investigation and investment to make systems HIPAA-compliant.
A rough cost estimate is $10,000 for basic risk assessments. This cost rises to $50,000 for wide-ranging risk analysis. These numbers do not include investments to address risks. So the eventual costs can be higher.
Conclusion: Stay compliant and do risk assessments
Managing risks is a core part of HIPAA compliance. Healthcare organizations can only protect PHI by carrying out comprehensive risk assessments. Without risk assessments, organizations will miss critical vulnerabilities. The result will be data breaches and PHI exposure. Eventually, poor risk management inevitably leads to HIPAA violation penalties and reputational harm.
Disclaimer: This article is for informational purposes only and not legal advice. Use it at your own risk and consider consulting a licensed professional for legal matters. Content may not be up-to-date or applicable to your jurisdiction and is subject to change without notice.