The zero trust security model operates on a simple but powerful rule: never trust, always verify. This article explores the benefits of this modern approach, as well as the key challenges businesses face when making the switch.
What is zero trust?
Zero trust is a set of network security principles based on the concept “never trust, always verify”.
With zero trust, every network user and device is verified and constantly monitored. No one and nothing is authenticated by default.
The main idea is that within a zero trust environment, all traffic, devices, and users are hostile until proven otherwise. The aim is complete protection against both insider and external threats.
This security concept emerged in response to innovations that have made network perimeters less relevant. Growing use of cloud resources, web applications, IoT devices, and remote work has outpaced traditional core and perimeter models. Security must now follow workloads across locations and through multiple cloud resources.
Key takeaways
- The zero trust model operates on a “never trust, always verify” basis, requiring validation for every user and device on the network.
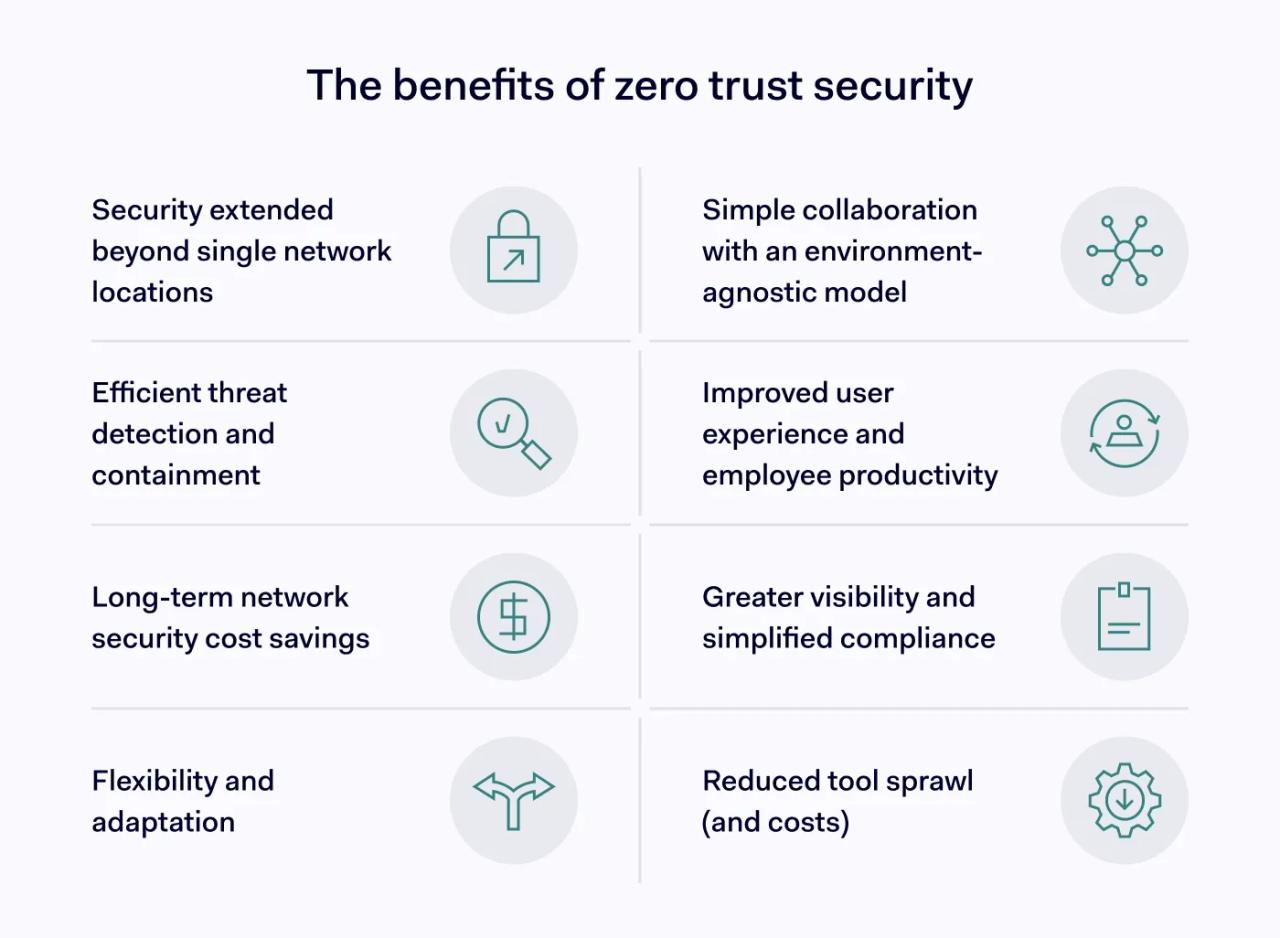
- Zero trust benefits include enhanced security beyond network perimeters, better collaboration, improved user experience, and long-term cost savings.
- Implementing zero trust can be challenging. It often involves configuration issues with legacy tools and requires planning to avoid security gaps.
- This security approach is essential for businesses that rely on remote work, cloud resources, and collaboration with partners.
- A well-implemented zero trust system provides better network visibility, simplifies compliance efforts, and contains threats by limiting lateral movement within the network.
Core zero trust technologies
To maximize the benefits of zero trust, organizations are transitioning to a dynamic, identity-centric stack. It’s about shifting from static network perimeters to a continuous, real-time validation loop that protects your data no matter where it lives.
Here is a breakdown of the core zero trust technologies that make this granular level of security possible:

User authentication
Zero Trust Network Access (ZTNA) generally adopts single sign-on (SSO) access control to enable simple authentication. SSO allows users to access resources quickly, while single or multi-factor authentication delivers a high degree of validation. Per-session access is also preferred to maximize security.
Device authentication
User devices are scanned and can gain access to network resources only when they have been authenticated and received security approval.
Privileges management
Identity and Access Management (IAM) systems set out the privileges for each user, which is a key part of applying zero trust principles. Users are allowed to access the resources they need, and nothing more.
Network segmentation
Network architecture is divided into sections via Software Defined Perimeter (SDP) tools. SDP manages privileges and contains any threats if they emerge.
Threat monitoring
Zero Trust Network Access (ZTNA) employs continuous threat monitoring, providing real-time information to security teams about potential threats. User activity is logged and available for audit as required.
One way to view a zero trust architecture is via the triad comprising the policy engine, the policy enforcement point, and the policy administrator.
The policy engine is the software that provides privileged access to core resources. The enforcement point allows users to access those resources, while the administrator communicates between the two nodes.
Unlike traditional setups that rely on legacy firewalls and VPNs, zero trust uses SDP tools to dynamically protect workloads as they pass through network resources. This agile approach fits cloud-native teams and the modern "work from anywhere" environments.
What are the benefits of zero trust?
Let’s start by stating who zero trust is best for. It has now become the standard for any modern organization, but it is particularly essential for businesses that:
- Rely on remote work or hybrid remote and on-premises working.
- Regularly collaborate with external contractors and partners.
- They depend on cloud resources and cannot rely on the performance of cloud security providers (CSPs).
- Need to protect sensitive data against data breaches and insider threats.
Adopting the zero trust model is about building a smarter, more agile infrastructure. Ensuring that every device and user is vetted before they can access the network focuses security on identity. This shift offers several benefits of zero trust:
1. Secures modern networks
A zero trust approach secures modern networks that have grown beyond a single or multiple physical locations.
The traditional network perimeter no longer exists. Many companies rely on access to cloud apps or data centers. They may also need secure access for remote workers or manage workloads on private and public cloud environments.
Zero trust is the answer to the security needs of those companies. Software-defined perimeters and microsegmentation allow workloads to travel wherever they need to go within the entire network, while applying strict user access privileges.
Security is based on user authentication and privileges, which follow the user across multiple locations. There is no need to supply credentials to access specific applications or services.
2. Improved collaboration
With ZTNA, different network architectures can also communicate securely without major structural updates or policy changes. Users simply require the correct privileges to access resources of any kind.
The granular approach enhances collaboration within the organization. Companies can precisely determine who can access apps and resources such as documents and work files. It makes collaboration smoother and safer, strengthening the protection of your intellectual property (IP) and reducing the need for time-consuming security processes.
3. Efficient threat response
With a zero trust security model, it is easier for companies to adopt a dynamic security posture prepared for sudden threat alerts.
If a user acts in a suspicious way, such as firing off unexpected access requests, they can be isolated via network segmentation, and the zero trust framework limits lateral movement through direct user-to-app connections. Cybercriminals can be contained rapidly and tightly, giving them a minimal opportunity to access sensitive data or compromise core assets.
All users are monitored in real-time, delivering instant insights to managers. Monitoring tools also generate a legible audit trail that feeds into security responses, compliance, and risk mitigation strategies.
On top of that, traffic on zero trust networks is rendered invisible to the external internet via high-grade encryption. This invisibility reduces the threat surface even more and makes a damaging security breach less likely.
4. Improved user experience
Implementing zero trust actually makes life easier for your employees and partners when it comes to accessing resources. SSO gateways remove the need to use separate passwords for multiple applications, and enabling MFA is faster and more secure than typing out a one-time code every ten minutes.
The feedback from companies moving to zero trust architecture is clear: it has many benefits for remote workers. It strips away the complexity of hybrid environments, giving your global workforce seamless, 24/7 access to both cloud and on-prem assets without the usual login headaches.
5. Long-term cost savings
While making the switch requires an initial investment of time and resources, the long-term benefits of zero trust more than pay for themselves.
More effective threat neutralization systems result in lower mitigation costs when data breaches occur. IBM has calculated that companies implementing zero trust save $1.76 million per data breach, so the savings can be substantial.
Other studies suggest that long-term security costs fall by 31 percent with an effective zero trust solution. This fall is probably due to lower licensing costs and savings from more efficient hosting setups.
6. Reduced tool sprawl (and costs)
One of the most underrated benefits of zero trust is how it cleans up your tech stack. Instead of managing a collection of disconnected security and networking products, zero trust lets you consolidate everything into a single, unified platform. This effectively kills off the headache of overlapping tools and siloed policies that usually force security teams to jump between half a dozen different dashboards just to verify one user.
By ditching the "tool sprawl," you aren't just saving on licensing costs—you're also preventing the gaps in protection that happen when different tools don’t talk to each other. When you combine that with fewer breaches and a better experience for your users, the ROI becomes clear.
7. Greater visibility and compliance
Complete visibility of corporate network traffic and user behavior is one of the greatest benefits of zero trust systems. Having this level of insight helps security teams analyze internal performance, adjust network architecture, and provide feedback to corporate managers.
Visibility is also a key part of network security compliance initiatives. ZTNA helps to reduce compliance risks posed by overprivileged software and uncontrolled user privileges. Real-time threat monitoring ensures continuous compliance, while seamless audit trails provide valuable information you need to meet industry regulations such as NIST 800-207.
You can also segment and lock down specific data assets needed to meet regulatory requirements. This focused segmentation can be particularly beneficial in sectors like healthcare, where the Health Insurance Portability and Accountability Act (HIPAA) makes rigorous demands on data security.
8. Flexibility and adaptation
Traditional network setups often turn adding new devices or resources into a security challenge. However, with ZTNA, IT teams have greater flexibility to reshape which devices, resources, apps, and services connect to their networks.
Resources can be moved rapidly from a private data center to any cloud environment without the need for creating new security policies. A single security policy applies across all resources.
IT teams can revise security policies via centralized tools before migrating them as needed, and low-level policy changes can be automated to save time. Centralized security policy management also means that companies can usually add zero trust architecture above existing assets with a few fundamental changes.
All of this means that organizations can efficiently scale up network operations, switch between cloud providers, shift to a different model of work, and tackle many other aspects of digital transformations.
Challenges of zero trust
Transitioning to a "never trust, always verify" model is a fundamental restructuring of an organization. While the long-term benefits of zero trust are clear, the path to implementation may be rocky. Let’s look at some of these challenges.

1. Configuration issues with legacy tools
Not all existing assets are set up to operate with zero trust systems. For instance, developers did not design many legacy payroll software tools to work with the principle of least privilege and microsegmentation.
Surveys have found that many companies claim to implement zero trust principles, while struggling to authenticate and monitor users in the real world. It is essential to assess legacy applications and platforms, and ensure that existing assets can operate with SSO, IAM, and other ZTNA tools.
2. Mitigating insider threats
ZTNA systems minimize potential risks while ensuring seamless user experiences. However, they remain vulnerable to threats involving employees or partners with valid login credentials.
PAM systems like biometric MFA can help to keep these risks to a minimum. MFA makes it much harder for insiders to pass credentials to outsiders for malicious use. The design of a well-configured zero trust architecture also makes lateral movement harder, limiting the freedom of intruders.
However, the threat remains, and it is vital to consider insider threats when formulating security policies.
3. Security gaps from poor planning
There is always a risk of leaving security gaps while constructing a zero trust architecture. Most companies choose a phased digital transformation to fill these gaps, including extensive testing and vendor trials.
Adopting zero trust can involve a fair amount of work. IT teams need to assess every device and application. Teams must create profiles for every user, with no exceptions.
Meticulous planning can also lead to a secondary risk of moving too slowly. If companies are excessively cautious, the process can become costly, while commissioned solutions could also become outdated when the process is complete.
4. Excessive disruption
Adopting a zero trust architecture can also be highly disruptive, causing problems for workforces and managers. Workers may encounter difficulties accessing core resources or logging into accounts remotely. Privileges can be improperly assigned, while conflicts with legacy software can lead to delays.
These potential problems make it essential to plan project milestones and inform staff at every stage of the zero trust rollout.
Conclusion
Modern businesses deal with a diverse and dispersed ecosystem that traditional security models are incapable of protecting. Zero trust security offers a logical solution to a practical problem, but it comes with its own obstacles.
This model offers benefits such as better cloud networking, remote work management, single sign-on, and enhanced monitoring. However, it can be costly to start, disrupt current workflows, and may have compatibility issues with old applications. While different from old security measures, the zero trust approach is capable of providing a holistic, dynamic security model that can adapt to modern digital environments.