Firewalls create a secure network gateway between private networks and the public internet. They filter incoming and outgoing traffic, blocking threats and allowing authorized data flows. This role makes firewalls a critical security tool. But firewalls themselves can also be vulnerable to configuration errors and external attacks.
This article will explore important firewall threats and explain the major risks faced by security teams. We will run through a typical risk assessment process to mitigate firewall vulnerabilities. And we will finish with a short list of best practices to secure your perimeter and meet regulatory goals.
Importance of protecting your firewall
Firewalls are the most important barrier between external attackers and your company network. Every organization needs to block malware and prevent unauthorized access. And the best way to achieve this is by filtering traffic intelligently. That's exactly what a well-configured firewall does.
Maintaining an effective firewall is of critical importance. When firewall defenses malfunction, security teams lose control of traffic entering network resources. Networks can quickly fall victim to Distributed Denial of Service (DDoS) attacks. And data-leeching malware can infest applications without the knowledge of security managers.
Firewalls are not a "set-it-and-forget-it" tool. They require updates, audits, and changes to function properly. But with the right firewall maintenance strategy, IT teams can ensure constant perimeter protection.
Top firewall vulnerabilities
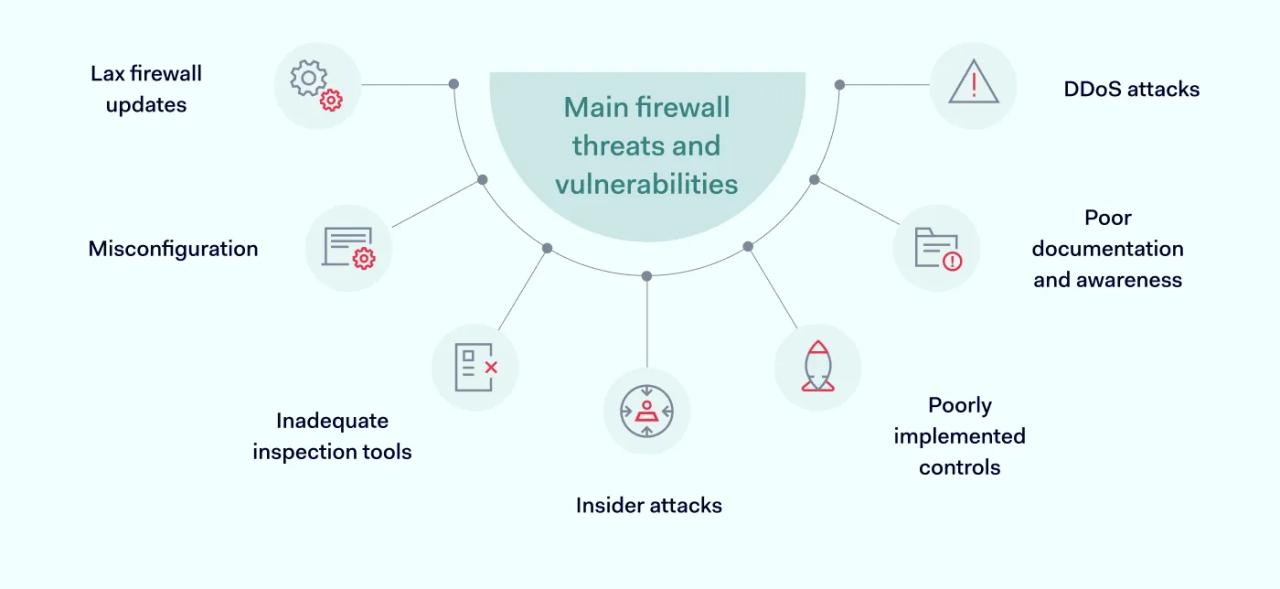
The first step in protecting firewalls is understanding the threats they face. Security managers can use this knowledge to risk assess their defenses. Common firewall threats to consider include:
1. Insider attacks
Some of the most dangerous firewall threats emerge from within organizations. Users with excessive privileges can breach perimeter defenses without any firewall intervention. When they gain access to internal network resources, they can steal data or damage digital infrastructure.
Insider threats make it important to apply network segmentation within the firewall perimeter. Companies can use cloud firewalls to create zones of trust and apply the principle of least privilege. This restricts users to small portions of the network and limits east-west movement.
2. DDoS attacks
Preventing DDoS attacks is one of the most important roles of a company firewall. DDoS attacks involve massive injections of access requests or data packets from malicious intruders. Without proper filters, large volumes of traffic can take down network resources. This leads to downtime and may cause data loss.
3. Poorly implemented controls
Firewalls usually come with extensive security controls to counter common threats. For instance, next-generation firewalls may feature anti-spoofing tools to block DDoS traffic. These controls are not always activated. Sometimes, users may not be aware they exist. But if you don't leverage all available threat mitigation tools, your security posture is incomplete.
4. Lax firewall updates
Firewall providers regularly update the firmware that delivers their services. But customers may not apply firmware updates quickly enough to counter threats. In some cases, users may avoid updates completely to save time – a counterproductive and dangerous policy.
Network security teams should always prioritize firewall updates. External attackers constantly update their methods. Firewalls can become obsolete overnight as new agents appear and existing filters fail to recognize them. Fortunately, users can generally automate patch management to make sure their protection is up to date.
5. Poor documentation and awareness
Firewall management requires detailed knowledge of filtering policies and network architecture. But this can disappear if responsible individuals leave the organization without documenting their work.
Firewall technicians should always maintain written logs and documentation for all applications, along with comprehensive rule descriptions. This documentation enables smooth handovers when personnel change. If it does not exist, security teams must waste time recreating their firewall policy from scratch.
6. Inadequate inspection tools
Firewalls depend on inspection capabilities to detect suspicious traffic. But there is a huge difference between the inspection functions of a primitive packet filtering firewall and a next-generation firewall based on deep packet inspection (DPI).
DPI operates at layer 7 of the OSI model and inspects the contents of data packets. Packet filtering can only scan the outer layer of network packets. This blocks some malicious agents but can be compromised by IP address spoofing attacks. NGFWs with DPI are much less vulnerable to spoofing attacks and will deliver far better network protection.
7. Misconfiguration
Many firewall threats stem from simple misconfigurations. For instance, network technicians may retain default passwords when installing hardware firewalls. Without regularly-changed strong passwords, devices will be relatively easy to hack. And when attackers breach firewall passwords, they can easily enter network resources.
Firewalls may also conflict with existing hardware or software. For example, next-generation firewalls often work with intrusion detection systems. IDS tools can generate excessive traffic loads.
This can impair network performance, leading to traffic bottlenecks. And it can also compromise the effectiveness of firewall barriers, creating points of vulnerability.
Tips for carrying out a firewall risk assessment
Firewall risk assessments evaluate the configuration of firewalls to make sure they mitigate critical security and regulatory risks.
A properly executed risk assessment considers all relevant firewall threats and recommends mitigation actions. Without one, companies cannot provide evidence of risk management. And they won't enjoy full awareness of their firewall security environment. So learning how to assess firewall risks is crucial.
Firewall risk assessments must include a list of security controls to mitigate key risks. For each control, security teams must document:
- What controls seek to achieve
- How security controls will operate
- The benefits controls will deliver
Planners also need to prioritize firewall risks. Security teams should categorize risks as high, medium, or low priority. High-priority risks need to be handled urgently. These risks should consume most of the assessment resources, as they pose the greatest data security threat.
A good best practice is to divide your firewall risk assessment into several core areas. Follow these general steps to cover every risk properly:
1. Create a change management strategy
Risk assessments aim to change security practices and policies. This requires significant alterations in firewall architecture and configurations. Without a change management plan, security teams can make errors and miss key project goals.
Questions to answer when building a change management strategy include:
- Who owns the process? Have you authorized officers to implement changes?
- Are you ready to test firewall performance at every stage of the process?
- Are you recording firewall changes to meet regulatory requirements? Every change should be linked to a named individual, creating an audit trail for regulators to consult.
- Are internal stakeholders involved and informed? Do you have the necessary approvals to make the project work?
- Have you set realistic schedules to complete the firewall assessment?
2. Consider physical security issues
If you are using a hardware firewall, include a robust section on physical security. Firewall appliances must be secured from tampering – both from insiders and external threats. Questions to answer in this section include:
- Have devices been patched and updated to meet current standards?
- Have you hardened your operating system effectively?
- Are device maintenance and inspection policies functioning properly?
- Are firewall devices and proxy server devices secure from physical damage? Is access limited to a small number of individuals with appropriate authorization?
- Do you have a current roster of people with permission to enter firewall locations?
3. Inspect the rule base underlying your firewall architecture
All firewalls employ a rule base to block unwanted traffic. This set of rules can be clear and focused, or it can be cluttered and chaotic. Firewalls work best with simplified rule bases, so cleaning up your policy rules should be a priority.
Important clean-up actions at this stage include:
- Eliminating or disabling unnecessary firewall rules.
- Checking for and removing expired objects in the firewall rule set.
- Searching for duplicate rules and combining them to make policy delivery more efficient.
- Creating simplified naming systems for all objects.
- Logging all rule changes as they are made.
- Looking for excessively permissive rules that allow too much freedom for network traffic.
- Elimination of any unused connections or groups/users who are no longer with the organization.
Excessive complexity is a major firewall risk. Over time, rule sets tend to grow in scope, resulting in imprecision and duplication. Time spent cleaning the rule set makes auditing firewall performance simpler. It makes firewall systems easier to understand, allowing security teams to focus on applying the right controls.
4. Assess firewall rules in relation to regulatory goals
The next stage is conducting a risk assessment of firewall threats. This process considers whether rules conform to regulatory frameworks such as PCI-DSS or HIPAA.
Every company has its regulatory context. Choose relevant frameworks and use them to measure your firewall risks. Create a ranking of firewall rules according to how likely they are to breach regulatory requirements. Use this ranking as the basis for risk mitigation strategies.
This stage of the process varies between organizations. But common challenges include:
- Checking that rule changes and firewall configuration changes have been made properly.
- Logging all rule set changes and hardware alterations.
- Discovering any network resources with direct connections to the external internet, and explaining why these connections are permitted under firewall rules.
- Checking that firewall rules conform to internal security policies, and why such differences exist.
- Discovering any entry points between firewall DMZs and internal network resources.
- Finding any rules that may create openings for malicious traffic.
- Assessing physical firewall threats and applying relevant controls to prevent unauthorized access.
If you find any concerns, add an entry to the firewall risk ledger. Prioritize the risk and agree on a mitigation strategy. Set time limits to complete the mitigation action, and ensure schedule audits to check that the risk has been countered.
5. Risk auditing
The final stage in the risk assessment is creating auditing processes. Audits show evidence of continuous compliance. They prove to regulators that companies are mitigating firewall risks, and discover areas of improvement for future risk management projects.
Creating a robust audit trail is critical. Actions to prioritize include:
- Following the change management plan until the audit stage.
- Automating systems audit processes where possible to avoid human error.
- Creating alerts to highlight emerging risks, new regulations, or modifications to network infrastructure.
- Scheduling regular firewall audits with appropriate penetration testing.
- Documenting all alerts and audit exercises. Secure backup storage is advisable.
Best practices to minimize the risks associated with firewalls
During the risk assessment and mitigation process, there are certain things to keep in mind. Here are some firewall security best practices to help you manage risks and protect your perimeter:
1. Map your firewall architecture
During change processes, it is vital to understand how firewalls fit into the network architecture. Create a map of firewall deployments in your organization, showing how firewalls connect networks, segments, and devices. Use this map as the basis for applying rules and testing security policies.
2. Centralize firewall management
Mapping firewall deployments also makes it possible to apply centralized management solutions. Bring together all firewall devices under a single point of control. This applies to single and multiple-vendor firewall environments.
Protect the firewall management interface via a dedicated network if possible. This will prevent access for malicious actors and safeguard a critical point of failure.
3. Update firewall software
Firmware and OS patches are crucial parts of firewall security assessments. Ensure all appliances or software tools are up to date. Apply automation processes where available to minimize the risk of security gaps.
4. Disable unsafe protocols
Some transfer protocols pose a critical security risk to internet-facing networks. Consider disabling Simple Network Management Protocol (SNMP) and telnet connections. And avoid any unsecured FTP connections.
5. Back up firewall rules
Losing firewall configurations leads to unnecessary work and security gaps. Back up your firewall databases and rule bases regularly. Think about enlisting specialist firewall management partners to log valuable data to use in forensic firewall analysis.
6. Schedule regular firewall audits
Security teams should monitor firewalls to ensure security rules are relevant and consistent. Schedule audits to track performance and log any configuration changes. Record any policy violations and take mitigation actions in response. Make sure audit records are available for compliance purposes.
Testing is an important component of firewall audits. Use path analysis for existing rules to prove their effectiveness and discover new policy rules where applicable. Testing also discovers duplicated objects, making it possible to refine firewall operations.
7. Limit administrative access
Admins require the ability to change firewall settings. But administrative privileges should be assigned sparingly. Log all administrative access requests along with any changes made to firewall setups.
8. Apply robust traffic filtering
Adopt a default policy of blocking all traffic and build your access policy from there. All traffic entering the network should be transferred by authenticated and authorized users. Create access categories for all users to define privileges and define allowed traffic types for each role.
9. Close unnecessary ports
Open TCP/UDP ports expand the attack surface for port scanners. This makes it easier to mount external attacks and breach or damage firewall defenses. Close any ports that are not in use, and double-check port status regularly.
External firewall attacks
Carrying out a full risk assessment and following our best practices will help you protect your firewall. Despite this, it's important to be aware of external attacks, and factor them into your planning.
For instance, your risk assessment should plan mitigation strategies against port scanning, network traffic floods, IP spoofing, and DDoS attacks based on packet fragmentation.
A properly configured firewall defends against known threats by allowing legitimate traffic and neutralizing DDoS floods or malware agents. A comprehensive risk assessment creates a documented pathway to achieve this, making it a critical part of any organization's security planning.