Keeping digital assets safe is a big challenge with today's scattered networks. That's why many organizations are turning to Firewall as a Service (FWaaS) to secure their cloud resources and remote teams effectively. A cloud-based approach offers solid protection without the hassle of traditional hardware, giving organizations security that can grow with their needs and be managed centrally.
Read on to see how its advanced security features can safeguard your digital world and simplify security management. First up, let's define FWaaS.
Firewall as a Service definition
Firewall as a Service (FWaaS) is a cloud-delivered security model that provides comprehensive network security capabilities—the kind you’d expect from on-site firewall appliances—but as a subscription service. This means core firewall tasks like traffic inspection, policy enforcement, web filtering, intrusion prevention, and threat detection are all cloud-based and managed by a provider.
The big plus? You ditch the physical hardware. This lets you use a secure firewall to protect everything from your office network to remote users and cloud applications, all with more flexibility and easier scaling.
Why do companies need FWaaS?
Firewall-as-a-Service is a reliable way to secure complex cloud environments. It is well-suited to businesses with large communities of remote workers, especially organizations reliant on SaaS, PaaS, or IaaS implementations.
Traditional network security revolved around moat and castle concepts and static perimeters. Important assets were held on-site. Attackers needed to penetrate fixed boundaries to reach those assets. In that context, standard firewalls were an effective solution.
With the rise of cloud computing, the network perimeter has melted away. Now, assets are held worldwide in third-party data centers. Users can access cloud apps from any location using a wide range of devices. Companies must now secure the junction between users and cloud applications.
FWaaS provides a solution. With firewall-as-a-service, companies can shield all cloud apps behind a consistent, robust defensive barrier. Employees access cloud assets via the firewall, whether they are working from home or in the office. IT teams gain total visibility of cloud usage and can apply controls via a central panel.
The result is improved security for cloud environments. Moreover, companies can easily combine FWaaS with SD-WAN technology to engineer Secure Access Service Edge (SASE) solutions. This combines security and ease of use, enabling managers to lock down sensitive data and apply granular access controls.
How does FWaaS work?
FWaaS transplants the familiar firewall model to a cloud context. Essentially, it acts as a proxy firewall inside the cloud.
Third-party providers create cloud environments with the capacity to host vast numbers of firewall implementations. Each customer hires a private section that is virtually isolated to ensure security.
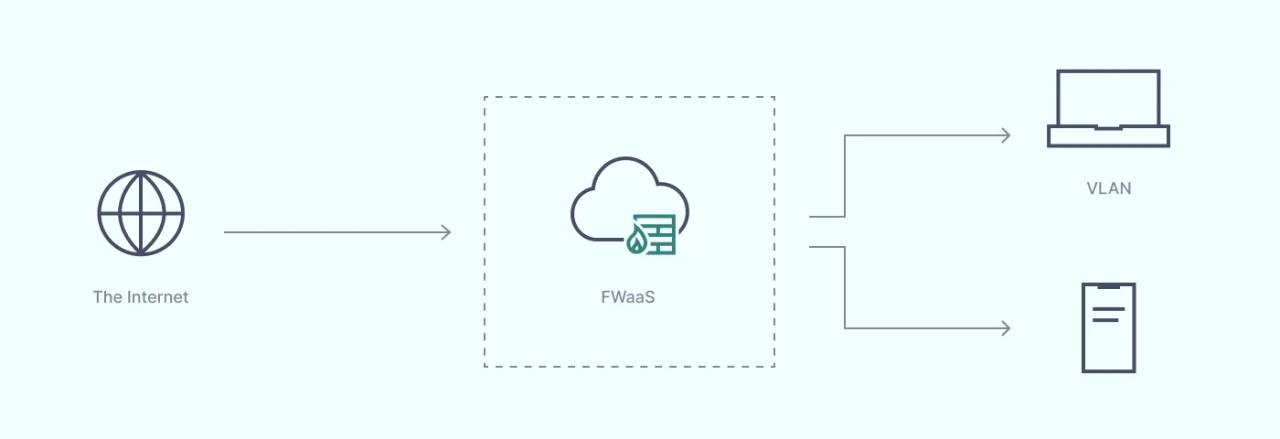
The firewall provider then creates an FWaaS instance. Customers can apply controls via a familiar firewall configuration panel. They can change filtering rules, implement app-specific controls, change DNS options, and generally customize firewall protection.
When the configuration phase is complete, customers set their local hardware to route traffic via the virtual firewall. At that point, FWaaS protection kicks in, and local firewalls become redundant.
The cloud firewall now stands between company assets and the wider internet. Cloud resources lie behind the virtual firewall, ensuring robust protection from external threats.
The result is a secure firewall that suits remote workers and companies with multiple branch offices. Users can connect anywhere, but firewall protection always applies.
Benefits of FWaaS
Important benefits of Firewall-as-a-Service include:
Cloud-native solutions
With the rise of cloud computing, securing critical data is challenging. Data may reside in the cloud and never touch on-premises networks. Backhauling traffic to central filtering hardware is an extremely inefficient solution. FWaaS functions inside the cloud, securing every endpoint without compromising performance.
Capacity
Traditional firewalls become network choke points as cloud environments grow. Even next-generation firewalls are not adapted for use with cloud applications. But cloud-based firewalls handle the data demands of cloud technology without suffering speed or security issues.
Simplicity
FWaaS allows companies to simplify their network architecture. There is no need for expensive and hard-to-maintain physical firewall equipment. IT teams do not have to replicate security stacks at different locations. A single firewall service provides security with a low hardware footprint.
Centralization
Centralized control panels streamline security management. IT teams can easily keep track of patch management. Security experts can manage outage sessions to carry out maintenance. And they can distribute security policies consistently to all endpoints with a single click.
SSL inspection
Most firewalls cannot deal with SSL-encrypted network traffic. SSL is a critically important encryption protocol, so workarounds are often necessary. This isn’t the case with FWaaS. Cloud firewalls include SSL inspection as standard. This makes it easier to combine encryption and firewall inspection, resulting in a more robust security posture.
Third-party management
Cloud firewalls are maintained and delivered by third-party providers. Customers simply choose options and route data as required. This reduces the workload on IT teams and eliminates costs linked to building in-house firewalls.
Easy scaling
With FWaaS, expanding protection is easy. Companies can consult with their provider and add extra capacity or features. If companies over-purchase, they can usually roll back to earlier setups until they find a suitable scale.
Traditional firewall vs. FWaaS
Companies transitioning from traditional firewalls can realize huge gains from cloud-based Firewall-as-a-Service.
Traditional firewalls tend to be installed on workstations via firewall software or on-premises hardware. Both solutions involve complex management and installation. IT teams need to update firmware and extend coverage to new locations. This adds extra costs and absorbs valuable time.
FWaaS removes the need for on-site management. Firewalls exist in the cloud. There is no need for hardware or software installation. Admins can change filter settings and extend coverage using centralized panels. Third-party providers handle updates, and local staff can concentrate on other challenges.
Firewall-as-a-Service is also optimized to protect cloud assets. Employees connect through the firewall instance. They can log in wherever they are, without compromising network protection. Cloud assets are placed behind the virtual firewall, and admins can change settings for different apps as needed.
Cloud firewalls also replicate the functionality of next-generation firewalls, offering enhanced network security capabilities. Deep Packet Inspection and IPS offer far stronger threat protection than traditional firewalls. Companies benefit from cloud-optimized efficiency and cutting-edge security.
Costs are also a factor. Traditional firewalls are expensive to run as networks expand. Network security teams must backhaul network traffic to central servers and replicate security stacks for different locations. With cloud firewalls, companies can expand their coverage affordably and rapidly.
FWaaS vs. NGFWs
FWaaS delivers important benefits compared with next-generation firewalls.
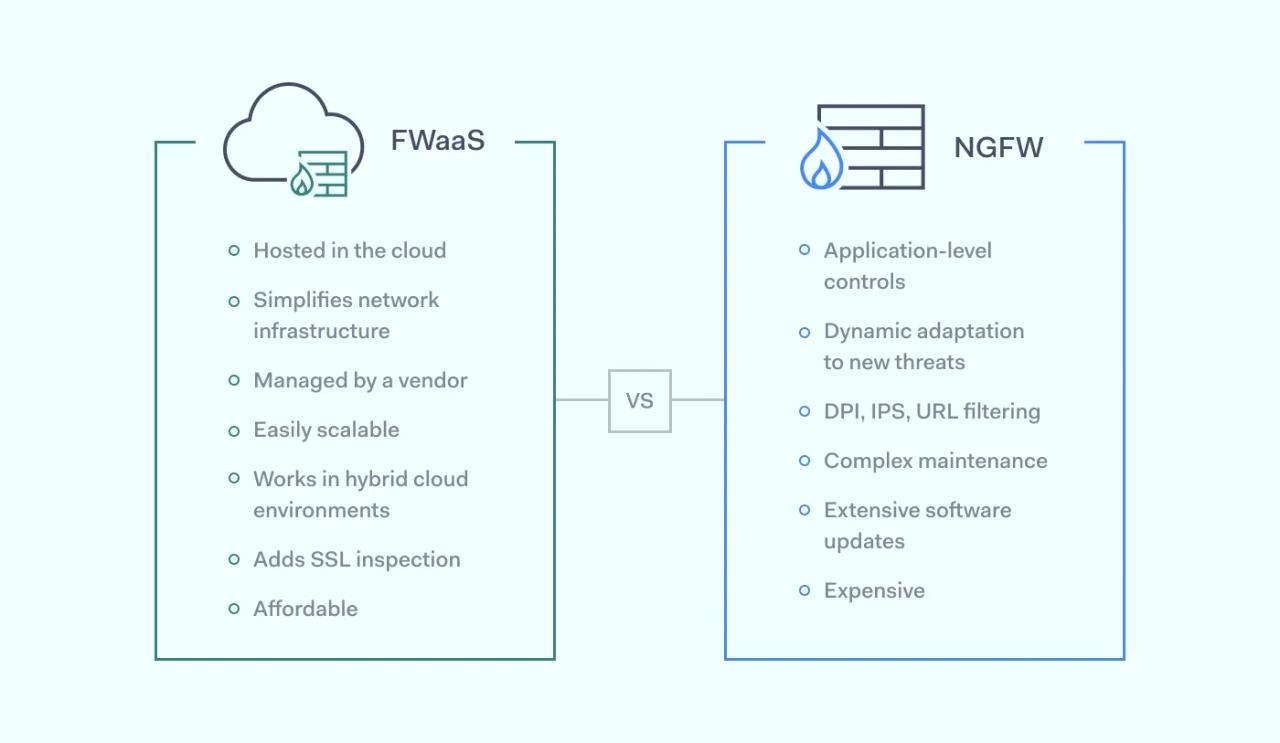
Next-generation firewalls include DPI, IPS, URL filtering, and application-level controls. Unlike older firewalls, they include dynamic learning that adapts to emerging threats. However, the growth of cloud computing has changed the security landscape. NGFWs now suffer in comparison to FWaaS:
- A cloud firewall enables managers to simplify network architecture. Maintaining a next-generation firewall is complex. IT teams must update software across the enterprise and cover all endpoints, including remote work devices. FWaaS is managed by third parties and easily extends to all connected endpoints.
- Next-generation firewalls were not designed to protect hybrid cloud environments. Today’s networks can include multiple cloud platforms, such as Google Cloud, AWS, or Microsoft Azure. Companies may need to protect hundreds of SaaS apps, with endpoints across the world. This isn’t possible via on-site firewalls.
- Costs are also generally lower when applying FWaaS solutions. Companies can choose a suitable subscription with the features they need.
- NGFW capabilities as standard with a cloud firewall. They include the core features of a next-generation firewall, such as DPI, and incorporate advanced security features. Cloud firewalls add features like SSL inspection that NGFWs lack. Always-on cloud intrusion prevention systems also scan for known cloud threats and mitigate attacks.
FWaaS vs. SD-WAN
Firewall-as-a-service complements software-defined wide-area networking. There is no conflict between the two technologies. They work together to enable SASE architecture and Zero Trust security solutions.
Software-defined networking moves on-premises infrastructure to virtual networks in the cloud. Users connect remotely to cloud resources instead of local network infrastructure. Software routes data intelligently to cloud assets, removing the need for on-site hardware.
This fits perfectly with cloud-based firewalls. FWaaS protects SD-WAN implementations. Firewalls cast a protective cloak around software-defined networks, making remote access more secure.
Cloud firewalls also remove the need for data backhauling. Security and connectivity are delivered via the cloud. This makes software-defined networking more efficient and safer to use.
Key FWaaS features
FWaaS is a modern, cloud-optimized alternative to traditional on-premises firewalls. Hosted on cloud servers, FWaaS can guard ever-changing SaaS deployments and allow safe remote access. Key features that make this possible include:
- Cloud-native security tools. Deep Packet Inspection, Intrusion Prevention System tools, DNS, URL, and web filtering create a robust defensive wall around cloud infrastructure. Firewalls inspect data packet contents, including SSL-encrypted traffic.
- Centralized management consoles. Admins calibrate FWaaS via a single pane of glass. Users can control filters and access settings, and distribute security policies instantly across all endpoints.
- Visibility and logging. Cloud firewalls include logging and visualization systems that make cloud assets visible. Activity logs integrate easily with cloud SIEM technology, providing a comprehensive record of network activity.
- Instant scaling. Customers can expand cloud firewall coverage rapidly by purchasing additional capacity. There is no need to add hardware.
- Third-party management. Specialist cloud firewall providers handle infrastructure, ensuring high levels of reliability. Local IT teams experience a reduced workload and can redeploy their expertise to other network security tasks.
FAQ
Is Firewall-as-a-Service (FWaaS) different from cloud firewalls?
No. You may see FWaaS referred to as cloud firewalls, but there is no difference between these products. A cloud firewall will provide the same protection as FWaaS and deliver the same benefits compared with legacy firewall solutions.
How well does FWaaS fit in the SASE framework?
FWaaS is a natural fit for Secure Access Service Edge network security implementations. SASE decentralizes network infrastructure. It applies software-defined networking, which requires security tools to prevent unauthorized network access.
FWaaS secures cloud infrastructure by filtering malicious content and expanding the network perimeter to cover all remote devices. IT teams can use firewall controls to block unauthorized traffic in line with Zero Trust policies.