
Anastasiya Novikava
Copywriter
Anastasiya believes cybersecurity should be easy to understand. She is particularly interested in studying nation-state cyber-attacks. Outside of work, she enjoys history, 1930s screwball comedies, and Eurodance music.
Cybersecurity

Gone are the days of bank robbers in ski masks. Today's heists happen silently over the internet, making cybersecurity for financial services the most critical vault door you own. Banks, investment firms, and credit card companies—like most financial institutions—hold detailed payment info and extensive personally identifiable information. That’s why financial institutions are prime targets, and the global shift toward digital payments has expanded the attack surface even further. The financial industry must race to lock the vault as cyber threats evolve.
Enterprise cybersecurity is critical, and financial cybersecurity matters even more because fintech and banks face strict regulatory requirements. Because financial institutions handle highly sensitive client information, many regulatory compliance requirements apply to them. Most financial institutions must protect client data by law. For financial institutions, a breach can irreversibly ruin reputation and even trigger fines or license risk for mishandling private client data.
The financial sector moves fast, but cyber-attacks often move faster. For financial institutions, one major hurdle is legacy infrastructure clashing with modern digital demands. Many financial institutions rely on outdated core banking systems that cannot easily integrate with modern security protocols. This creates dangerous gaps that cyber threats exploit. Simultaneously, the aggressive push for mobile banking and instant payments expands the defensive perimeter, making securing financial services against sophisticated ransomware and phishing attacks increasingly difficult.
For financial institutions, third-party risk management is a massive headache for CISOs. Financial institutions rarely operate in isolation; they rely on a complex web of fintech partners, cloud providers, and vendors. If just a single vendor has weak security, the entire chain becomes vulnerable. In the financial industry, balancing strict regulatory compliance—such as GDPR or PCI DSS—while maintaining a seamless user experience is a tightrope walk that keeps security teams up at night.
Compliance regulations for financial institutions depends largely on the area of operations. The regulations will be somewhat different for US and EU institutions. Meanwhile, some standards like Payment Card Industry Data Security Standard (PCI DSS) apply to entities that store, process, or transmit payment card account data (and others that can affect the security of the cardholder data environment).
Still, almost universally, when trying to be more compliant with various regulations, the requirements boil down to these points:
Adoption of a cybersecurity program: it should include appropriate policies and procedures based on individual risk assessment.
Have a cybersecurity auditing mechanism: various risks and current organizations set up to withstand them should be periodically evaluated.
Have a chief information security officer (CISO): in financial cybersecurity, a CISO must own accountability for risk management.
Financial institutions must secure data in transit and at rest: sensitive data can’t be unencrypted.
Access to client data should be restricted: sensitive information should be granted after passing identity confirmation.
All network activities should be logged: during an inspection, auditors will have to see what was accessed and when.
Introduce cybersecurity awareness training: employees should receive training to be prepared to detect the most common social engineering examples.
Have an action plan in case of a data breach: if an organization was affected by a cybersecurity accident, there should be clear action steps on what should be done, i.e., what government institutions should be informed.
Still, depending on the handled data, there could be additional requirements.
Financial organizations must do more than keep the lights on. Let’s discuss some actionable best practices the financial services industry can use to secure financial assets and data.
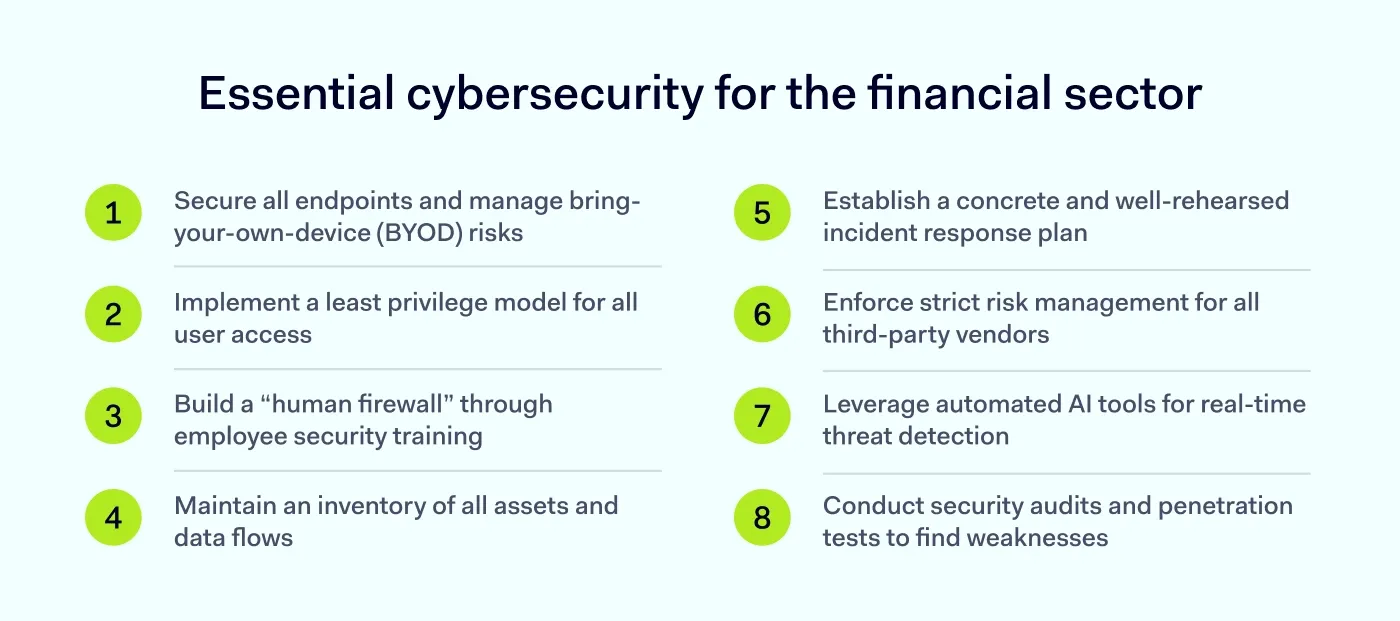
As organizations adopt “bring-your-own-device” (BYOD) strategies, they invite risk through the front door. For financial institutions, unmanaged devices introduce blind spots within the internal network. While flexibility boosts morale, the financial services industry cannot afford to be lax.
Financial organizations need total visibility over what devices are plugged into the company network. You must plan containment strategies for when—not if—a user device gets infected. Implement clear policies that dictate connection requirements, such as mandatory OS updates and antivirus installation. If the device isn't up to code, it shouldn't get access.
Not everyone needs the keys to the data. Financial institutions should be ruthless when granting administrative privileges due to the critical nature of sensitive data. If an intern accounts for the same permission level as a senior admin, you are asking for trouble.
Adopt a tiered access model. The ability to bypass, override, or change system settings should be reserved strictly for network administrators. Every other user group should have the absolute minimum privileges required to do their job. This limits the blast radius if a user’s credentials are compromised in cyber-attacks, preventing threat actors from moving laterally across the network.
The most sophisticated firewall can’t stop an employee from clicking a bad link. The largest data breaches are often caused by social engineering. When building a financial cybersecurity strategy, you must address the human element.
Financial services staff are high-value targets for phishing, and cyber threats keep getting more convincing. Regular, updated training is essential—cyber threats change too fast for annual PowerPoints. New threats require real-time awareness. Prioritize training for new hires and run simulated phishing campaigns to identify who needs extra help. An educated workforce is your first line of defense against cyber threats.
It is impossible to have an effective strategy if you don't know where your financial assets and data live. Since financial institutions have sensitive data constantly circulating, you must map every route it travels and every server where it rests.
Pinpoint these data flows to prioritize encryption and authentication. Your most valuable assets require the highest entry bar. Practice risk-based access security and create a model that ensures client data isn't just sitting in an overlooked folder waiting to be stolen.
In financial cybersecurity, panic is not a strategy. IT teams in financial organizations must have dedicated protocols, testing schedules, and clear chains of command. When a breach occurs, financial institutions need everyone to know exactly what to do, who to call, and which regulators to notify.
Establish a “war room” mentality for emergencies. The team needs a decisive leader to spearhead containment and recovery initiatives. Tools should be in place to track cyber-attacks in real time once an incident starts. A structured, pre-planned approach limits confusion and drastically reduces the time attackers have to siphon off data.
The financial services industry is hyper-connected, and attackers know this. They often target smaller, less secure vendors to gain backdoor access to larger banks. Managing these third-party risks is critical. In financial cybersecurity, you are responsible for your data even when it’s in someone else’s hands.
Financial institutions should audit their supply chain relentlessly. Ensure that every vendor complies with your security standards before signing a contract. Access for vendors should be segmented. If a third-party tool is compromised, it shouldn't bring down your entire banking core.
The bad guys are using AI, so you should, too. Traditional manual monitoring cannot keep up with the volume of transactions that financial companies process daily. Automated solutions are necessary to spot anomalies that signal money laundering or cyber-attacks in real time.
Machine learning tools can analyze patterns faster than any human analyst, which helps spot cyber threats sooner. AI-driven threat detection helps you stay ahead of these statistics by flagging unusual behavior before data is exfiltrated.
Don’t wait for cyber-attacks to reveal your vulnerabilities. Regular security audits and penetration testing are vital for identifying weak points in your infrastructure. In financial cybersecurity, this stress-tests defenses against realistic scenarios.
Hire ethical hackers to attack your system. Their findings provide a roadmap for patching holes in your defense. With rules like the EU’s DORA applying from January 2025, many financial entities must establish and maintain a digital operational resilience testing program (with advanced TLPT requirements for certain entities). It is better to fail a test on your own terms than to fail in public during a real attack.
The financial sector attracts attackers due to the possession of sensitive financial and personal information. Finance-related service providers must prove reliable for clients to entrust their data and money.
Built around the Security Service Edge (SSE) framework—the security-focused portion of Secure Access Service Edge (SASE)—NordLayer is a secure remote access solution that offers an effective strategy for modern companies with remote teams of all sizes to transition to a safer environment. Easy to deploy, start, and scale with no hardware to maintain, NordLayer’s features can support your cybersecurity roadmap and compliance efforts.
Centered on data security and network access management, NordLayer helps enhance existing organizational infrastructure with operating tools and services. With Zero Trust Network Access (ZTNA) principles, NordLayer supports access control practices through its Business VPN (the foundation of NordLayer), traffic encryption (in transit), and tools you can use to implement a network segmentation strategy, plus options like dedicated IP addresses.
NordLayer’s design is valuable for upgrading the company to an up-to-date technology environment and refining reasonable cybersecurity practices with a centralized Control Panel—giving IT admins visibility into network access, connections, users, devices, and performance (without tracking what people do inside the network).
Despite challenges, achieving strong cybersecurity in financial services is simple. Get in touch and learn how to build security that adapts to your business needs.
Subscribe to our blog updates for in-depth perspectives on cybersecurity.