A cloud firewall is a virtual device that protects cloud resources from external threats. Also known as Firewall-as-a-Service (FWaaS), cloud firewalls filter traffic crossing the network perimeter. But they also include features that go beyond traditional firewall appliances.
A robust cloud firewall secures the SaaS applications that modern businesses rely on. It helps to protect sensitive data, reducing the risk of damaging data breaches. And it provides security teams with greater visibility. FWaaS enables centralized control and awareness of all cloud-based assets.
This article will explain how cloud-based firewalls work and some of the core features they include. We will look at some cloud firewall benefits, as well as some common challenges users encounter when applying FWaaS.
Cloud firewall definition
Traditional firewalls filter traffic entering on-premises networks and individual devices. Cloud firewalls are similar, but with some important differences.
A cloud-based firewall protects SaaS assets by filtering incoming and outgoing traffic. But it does so using virtualized appliances. Cloud-based filters are cloud constructs that reside in the cloud. There is no need to install a hardware firewall or add software firewalls to user devices. And there is no need to backhaul traffic to a central data center.
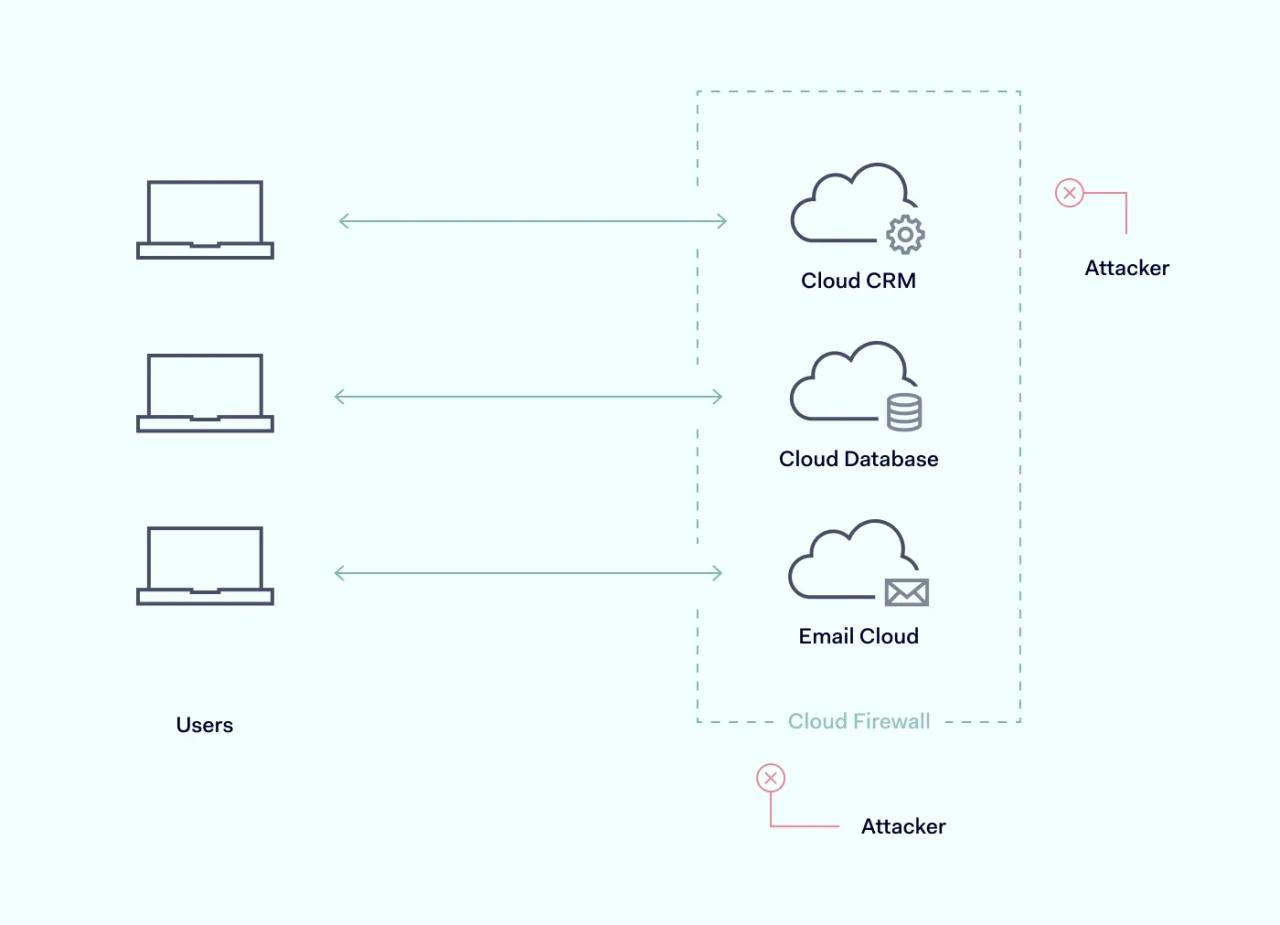
When users connect to cloud infrastructure, the firewall automatically screens their identity and monitors traffic. Users can access SaaS apps securely anywhere. IT teams can track their activity and take action when the firewall detects potential threats.
A cloud firewall usually matches the deep inspection capabilities of next-generation firewalls. But not all next-generation firewalls are adapted for the cloud. This is an important fact to keep in mind when protecting data on the public cloud.
Importance of cloud firewalls
Why has Firewall-as-a-Service become an important network security tool? The main reason is the increasing importance of cloud computing.
- Traditional network security tools struggle to extend traffic filtering and threat detection to cloud environments. Cloud firewall systems integrate automatically with SaaS or PaaS deployments and use a virtual security stack to fill the security gap.
- Cloud-based firewall systems scale smoothly as cloud environments expand. They are well-adapted to the needs of businesses as they add new SaaS apps and provision remote workers with cloud access.
- The shared responsibility model used in cloud computing is another factor. Users and cloud providers share network security roles. The cloud service provider (CSP) must protect the underlying cloud infrastructure. But customers need to safeguard apps and data. The CSP will not filter incoming traffic or manage user identities. A cloud firewall solution steps in to perform those roles.
- Cloud-native firewalls are better at neutralizing threats on the cloud. They can mitigate Distributed-Denial-of-Service (DDoS) attacks efficiently. And they can apply granular control settings to segment cloud environments. Attackers will struggle to move between apps or databases, making client data more secure.
Purpose of firewalls
Firewalls perform a range of important functions in the cloud network. This includes familiar functions like network traffic filtering. But it also extends to more advanced, cloud-native purposes. Key functions include:
- Tracking traffic entering and leaving the cloud platform.
- Blocking access to unapproved identities. Approving secure access for legitimate users.
- Application visibility across all cloud assets, including multi-cloud settings.
- Delivery of firewall security policies to all endpoints.
- Segmentation of cloud resources to limit east-west traffic and protect confidential data.
- Automated threat reporting for threat response and audits.
Cloud firewall types
Cloud firewalls are now an essential component of network security. These firewalls come in various forms, each tailored to meet specific needs and environments.
- Public cloud firewalls, usually deployed in services like AWS or Azure, provide functionality similar to hardware firewalls. Yet, in hybrid cloud environments, public firewalls have more benefits than on-premises appliances when it comes to scalability and availability.
- Firewall as a Service (FWaaS) uses next-generation firewall (NGFW) technology. It encompasses deep packet filtering, URL filtering, advanced threat prevention, IPS, and DNS security. FWaaS eliminates the need for physical appliances, simplifies IT infrastructure, and centralizes management for consistent policy enforcement.
- Software-as-a-service (SaaS) firewalls protect networks by filtering incoming traffic and blocking threats. Variants include Security as a Service (SECaaS), a subscription-based network security service, and FWaaS, which scales according to network needs.
- Web Application Firewalls (WAFs) secure web applications from threats like cross-site scripting (XSS) and SQL injection by analyzing and blocking malicious traffic based on predefined rules. WAFs also help enforce security policies and ensure compliance with industry standards.
Cloud firewall features
Public cloud firewalls leverage various features to perform their core functions. Important features to know about include:
Security policies and rules
Security policies determine how firewalls filter traffic and manage access control. All firewalls use security policies to set conditions for access. Cloud-based firewall tools are no different in this regard.
Matching conditions include IP addresses, geographical locations, URL and DNS data, user behavior, and device information. Requests that meet those conditions are approved. If not, the firewall denies access.
Unlike traditional firewalls, cloud firewalls offer in-depth policy management. Security teams can create grouped firewall rules for applications or user groups. Or they can set rules separately for each resource. Policies synchronize with identity and access management systems to manage user access on a granular level.
Real-time threat protection
Public cloud firewalls track and block threats in real-time. This could include DDoS floods, ransomware attacks, or zero-hour exploits. The firewall assesses all incoming data before it arrives at cloud assets. Suspicious files are sandboxed for analysis and may be denied access.
Threat protection goes beyond data filtering. Cloud firewalls are multi-layered. They leverage packet inspection to detect CSS attacks, trojans, or SQL injection. Traditional firewalls rarely have that ability.
Cloud-based firewall systems also utilize global threat intelligence. Security services use data from vast global databases. This allows the firewall to block emerging exploits and malware agents.
Advanced reporting and analytics
FWaaS services combine threat detection with centralized management tools. This provides maximum visibility for security teams. Administrators can track user activity and device connections. They can access data about network performance, and respond to security alerts before threats become critical.
Data flows are presented in real time. There is no lag between data gathering and analysis. If needed, admins can also filter data by user groups, regions, apps, or time periods. The entire cloud environment is visible and easy to manage.
Data collection also feeds into security audits. IT teams can use historical data to improve their security posture. Audit data also makes it easier to meet compliance goals. Companies can prove that their cloud environments are secure and that customer data is safe.
Flexibility and scalability
Cloud firewall services are built to scale smoothly as more apps and containers come online. Traditional firewalls run into difficulties as a cloud network grows. Data must be backhauled for inspection, and managing remote access endpoints becomes increasingly difficult. FWaaS solves these issues.
Companies do not need to manage firewall hardware. Cloud partners handle maintenance and updates. Firewalls in the cloud also automatically balance bandwidth loads to suit network demands.
Remote workers can access cloud infrastructure wherever they are. The firewall provides global protection. Organizations can therefore be much more flexible about travel and working from home.
Benefits of using a cloud firewall
Using a cloud firewall makes sense for companies that are dependent on cloud applications and storage. Firewall-as-a-Service has several benefits that encourage better security and general efficiency:
Improved security and compliance
Cloud-native firewalls block malicious traffic from malware and bots. They also segment application environments. The firewall isolates critical apps. It limits access to a small number of users and minimizes east-west traffic between virtual assets.
Firewalls apply cloud security policies consistently across hybrid clouds and every network endpoint. Software-defined networks enjoy comprehensive firewall protection, while managers can toggle settings for different resources if the need arises.
Stronger internet security leads to more robust compliance. Companies can show that client data is secure. Points of sale are separate from employee workloads. Endpoints are locked down and malicious agents are screened before entering the network environment.
Cost-effectiveness
The cost of traditional firewalls can spiral as cloud deployments grow. But public cloud firewalls solve this problem. A security-as-a-service solution saves money in various ways:
- There is no need to install hardware across branches or remote work locations.
- Maintenance costs are low. Firewall protection is provided on a subscription basis and users can purchase extra features if needed.
- Public cloud firewalls are automatically updated. There is no downtime during the update procedure.
- Firewall downtime is generally much lower. Cloud coverage operates 24/7.
- Companies do not need to worry about adding redundancy to ensure high firewall availability.
- Better data security reduces costs associated with data loss or regulatory breaches.
Ease of deployment and management
Easy deployment is another major strength of cloud firewalls. Thanks to cloud architecture, security teams can deploy a cloud firewall anywhere. It doesn't matter whether workers are stationed in New York or Sydney. Cloud firewall protection will apply when they log onto SaaS resources.
Public cloud firewalls also scale easily. Organizations can open new branches and use cloud security tools to control access. They do not need to provision hardware or software firewalls to users. Firewall protection also scales virtually. As cloud resources expand, FWaaS tools adapt. Bandwidth is not an issue, unlike legacy firewall systems.
Reduced downtime and increased productivity
One of the biggest benefits of cloud firewalls is less downtime and greater productivity. Cloud firewalls are available 24/7. They do not suffer periodic downtime due to local power networks or maintenance schedules. The firewall operates constantly. This is a major benefit for organizations with global workforces and a 24/7 work cycle.
Public cloud firewalls also include automation features that reduce the IT workload. Centralized control panels enable administrators to automatically distribute security policies to all endpoints. Virtualized instances make manually provisioning firewalls unnecessary. Firewall protection exists inside the cloud, not on user devices.
Challenges in using cloud firewalls
Cloud-based firewalls have advanced features and fit neatly into cloud architecture. Despite this, users of cloud firewall systems often encounter challenges. These challenges include:
Integration with existing security systems
Public cloud firewalls may need integration with on-premises networks. Companies often run hybrid cloud deployments. Security teams must manage network devices like servers, routers, and hardware firewalls. But they need to ensure these local resources interface with cloud firewall protection.
Cloud firewall tools must also integrate with existing Identity and Access Management solutions. Firewalls must access and leverage identity directories to approve requests. Compatibility issues can compromise firewall coverage and cause performance problems for network users.
Managing firewall rules and policies
Application sprawl can expand the threat surface. But administrators may lack visibility as cloud deployments grow. Users may add SaaS apps without central knowledge. They may add APIs or service accounts to connect cloud assets. Security policies must extend to all cloud resources. If not, unknown assets will pose a major security risk.
Ensuring data privacy and security
Cloud firewalls do not encrypt data. They can control access to specific cloud apps, but offer few protective features for critical data. This can lead to complacency. Organizations may feel secure. But if data is poorly protected, attackers breaching the firewall can extract information very easily. That's why data encryption and data loss prevention tools are also essential.
Key takeaways
Cloud firewalls build on traditional firewall systems, adding cloud-native functionality. They allow organizations to protect assets in the public cloud. Cloud firewalls manage access and integrate with IAM systems, preventing unauthorized access and defending critical data.
Summary: benefits and importance of a cloud firewall
Cloud firewalls:
- Monitor network traffic entering cloud environments.
- Block malicious files and unauthorized access requests.
- Allow authorized access according to cloud security policies.
- Quarantine and analyze threats.
- Apply global threat intelligence to provide up-to-date protection.
- Segment cloud environments in line with Zero Trust principles.
- Scale easily to add more bandwidth.
- Reduce the costs of protecting cloud assets compared with legacy firewalls.
Enhance your data security with a customized cloud firewall
All companies that depend on cloud storage and SaaS applications should consider switching to a specialist cloud firewall. Cloud-native security services protect data, allow safe remote access, and optimize performance. Explore the options with Nordlayer's cloud solutions today.