Privileged accounts can make fundamental changes to network infrastructure or applications. When hackers gain access to privileged accounts, they can easily damage systems and steal data. This makes privileged access management (PAM) a critical security issue for all organizations.
Privileged access management seeks to secure all privileged accounts within a network community. These accounts include system admins, root accounts, domain administrators, and service accounts. They also include all staff members with access to firewalls and routers, and privileged accounts may also apply to database admins.
A robust privileged access management setup makes it possible to:
- Authenticate all privileged user access requests
- Authorize privileged users according to the principle of least privilege
- Supply temporary privileges as required for system tasks
- Monitor user activity and alert IT teams about suspicious behavior
- Document user sessions and supply an audit trail for compliance purposes
How can you create a PAM setup that delivers these features? This article will discuss several PAM best practices to manage privileged accounts without compromising the productivity of users.
10 privileged access management best practices
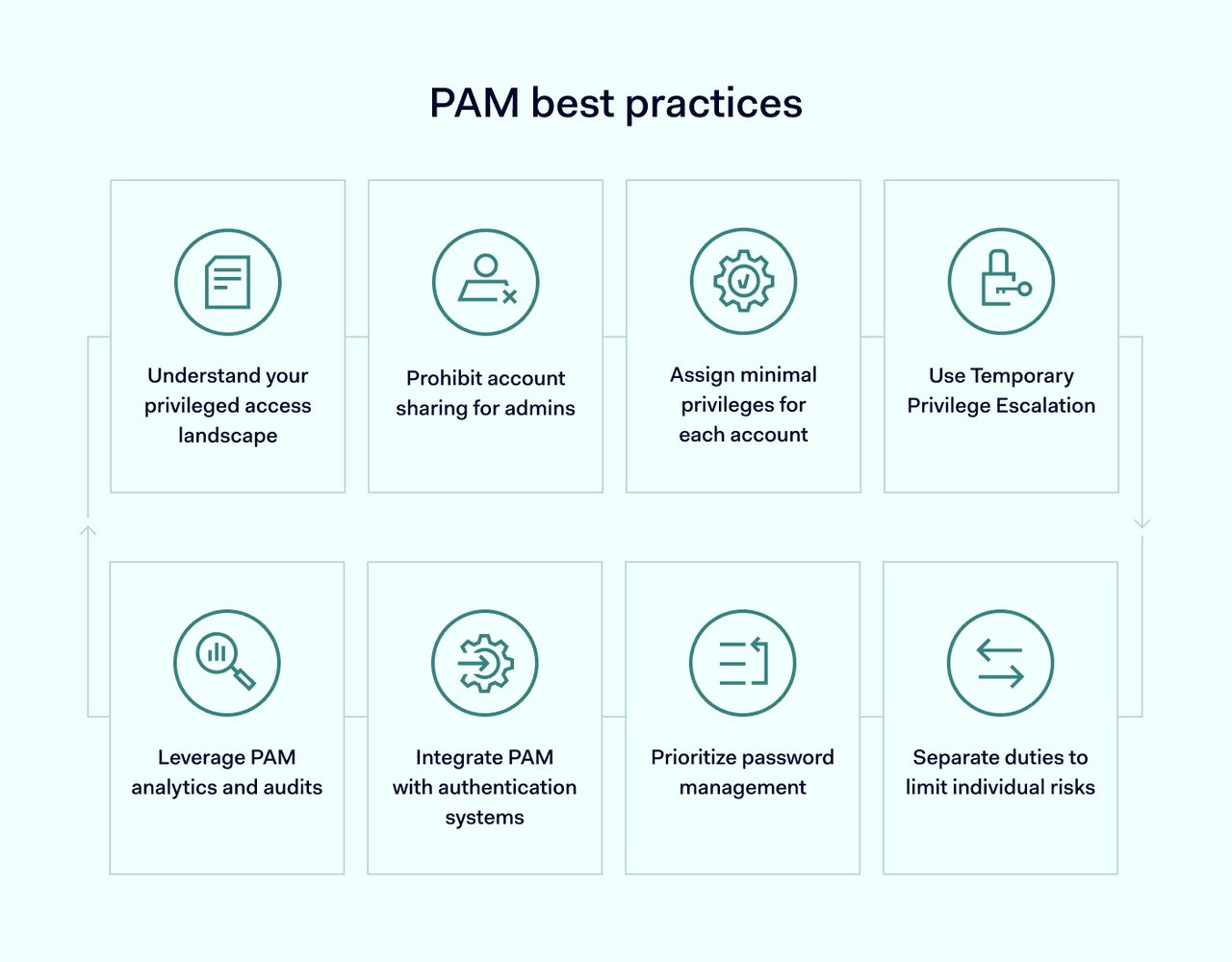
Privileged access management is a flexible tool. Each organization will have unique priorities. But some general principles apply to almost all settings. Here are some best practices for privileged access management:
1. Understand your privileged access landscape
The starting point for protecting privileged access is knowing which accounts to control. To apply controls**, planners must also categorize privileged accounts accurately.**
The definition of a “privileged user” varies between organizations. Assess your network and application environment. Determine which accounts have far-reaching powers, and which users pose the greatest security risk.
Now, create an inventory of high-priority accounts with administrative roles. Include Active Directory domains, business app owners, hardware maintenance teams, and any root account holders.
Clearly identify who owns the privileged account and why they have those privileges. Risk assesses each account based on the scope of its privileges. This risk assessment should consider the potential security risks attached to each account. Focus on the riskiest accounts first and work down to less critical privileged accounts.
Document everything and create a register of privileges. Use this register as a foundation for future extra controls.
2. Prohibit account sharing for admins
Blocking shared accounts is an easy win for any PAM architect. Shared accounts pose a serious access control risk, providing an open door for hackers to gain access and steal sensitive data.
It’s a good idea to name individual account holders and specify their responsibilities. Holders must know the policy about sharing accounts. Tracking systems should check who is using high-privileged accounts and whether sharing exists.
3. Assign minimal privileges for each account
Use the account inventory to apply the principle of least privilege across all admin accounts.
This principle states that users should have the permissions needed to access relevant workloads. Beyond that point, access to network controls and resources should be limited. In line with Zero Trust concepts, users should have limited access rights without authorization and authentication.

Role-based and attribute-based controls allow admins to distribute privileges in granular detail. Attributes include read/write privileges for databases, deletion rights, and the ability to create app instances. Roles make it easy to limit administrative privileges to specific tasks.
Cloud-based controls are also important in modern network settings. IT teams can use Active Directory to assign role-based privileges for cloud services, reducing their workload and limiting the risk of human error.
Managers should also focus on machine or service accounts. These accounts need password access to carry out their duties. Limit their privileges and bring service accounts under automated management. Remember to audit them as thoroughly as human-operated accounts.
4. Use temporary privilege escalation
IT teams can enhance their privileged access management by operating temporary privilege escalation. This provides privileges on a just-in-time basis. Escalation applies for a defined period. Permissions are limited to specific object attributes, devices, or network operations.
Record all requests for privilege escalation and ensure that these requests are approved. This creates a solid audit trail and adds another layer of scrutiny to avoid security incidents.
Escalation is also a useful tool when applying Zero Trust ideas. Users cannot exercise privileges outside of set periods and can only use permissions after supplying verified credentials.
5. Separate duties to limit individual risks
Separation of duties is a core risk management principle and a key aspect of privileged account management. No user should have wide-ranging powers to make system-wide changes. Any high-privileged actions should require approval before execution.
Network managers should divide privileged actions for applications or systems. Dividing access rights limits the ability of a single attacker to breach critical resources or steal data.
6. Prioritize password management
Password management is a critical part of protecting privileged access. With a single set of privileged credentials, hackers can launch data breach attacks and damage systems. These attacks can pass unnoticed under the cover of legitimate privileged activity, making them very hard to counter.
Weak, rarely changed privileged account passwords expand the attack surface. Enforce a strict password policy for privileged accounts. Include strong passwords, with regular changes. And make sure users with access to several accounts use different passwords for each.
Sometimes IT teams keep default passwords for routers or firewall appliances. This is risky, as default passwords are easy to guess and widely known. Require strong passwords for all newly installed network assets.
Combine these issues in a robust password security policy. This document should explain the definition of a strong password, the rules for changing passwords, and the penalties for unsafe password management. Make this policy available and integrate it into staff security training.
7. Integrate PAM with authentication systems
Privileged access management deals with access control inside the network perimeter. But it’s equally important to control access when privileged users log into resources.
Every privileged session should start with multifactor authentication (MFA). Provide account holders with secure authentication tokens or biometric scanners, or choose a smartphone-based alternative.
Extra authentication factors make it much harder to breach critical resources. They should work alongside PAM in a company’s security policies.
8. Leverage PAM analytics and audits
Last but not least, one of the best practices for privileged access management is recording privileged activity. This step is critical as security teams must document all sessions, both historically and in real time.
Log data must be clearly recorded and legible. Monitoring data should provide timely alerts when security issues arise. Logging feeds into auditing and compliance work streams. This supplies valuable evidence of privileged account protection while strengthening general data protection.
Audits can find inactive privileged accounts, which admins should delete right away. They also spot privilege creep, where users have unnecessary access rights.
Rule-based access controls are less effective once users are within the network boundary. Advanced analytics detect unusual patterns of behavior that rules often miss.
For example, data like mouse movements, key presses, and time of access can flag up potential security incidents. Without PAM, companies can overlook intrusions before it's too late.
9. Apply adaptive access policies
One of the emerging PAM best practices is using adaptive access policies that respond to real-time risk indicators. These policies analyze contextual signals—such as user location, device health, or login behavior—and adjust access privileges accordingly. If a login attempt originates from an unfamiliar country or during off-hours, access can be automatically restricted, or additional authentication required.
Adaptive access strengthens your PAM strategy by aligning privileges with dynamic risk levels. This minimizes unnecessary friction for legitimate users while increasing protection against abnormal behavior. For example, tools like NordLayer’s Network Access Control (NAC) can help enforce location-based access restrictions. It adds a layer of intelligence in line with Zero Trust and modern PAM best practices.
10. Integrate PAM with DevOps workflows
DevOps environments frequently rely on automation scripts and CI/CD pipelines that require privileged credentials. Incorporating PAM best practices into these workflows ensures secrets are never hard-coded or exposed manually. Automating credential rotation, logging privileged activity, and applying role-based access across tools reduces the risk of credential leaks.
By embedding these controls directly into the DevOps lifecycle, organizations create secure-by-design development pipelines. This not only strengthens operational security but also supports compliance. The right PAM solution also applies strict access rules to automated tools and systems, not just people—making sure everything follows the same high security standards.
Implement PAM on your critical assets
Managing privileged accounts is a constant challenge. A single poorly secured admin account can bring down an entire e-commerce platform or company network. Efficient PAM systems provide reassurance and enhanced security. Use our best practices to design a system that maximizes security and boosts productivity.
Today, adopting PAM best practices is essential for risk management and operational continuity. These practices help organizations stay ahead of cyber threats by enforcing consistent, granular control over privileged accounts. Whether you're working with cloud infrastructure, on-premises systems, or a hybrid of both, strong PAM strategies limit exposure and improve oversight.
From audit-ready compliance to real-time behavioral monitoring, PAM isn't just a set-and-forget tool—it’s an evolving discipline. Align your controls with business goals and integrate access management deeply into your IT and security fabric. Investing in a PAM solution built for flexibility and scalability will help secure critical assets now and into the future.
