Zero trust is a strategic framework that enhances security and reduces the risk of breaches. It treats every user and device as a potential threat, requiring verification at every step rather than assuming everything inside the network is safe.
Due to its complexity, implementing zero trust can be challenging, often requiring extensive setup or system adjustments. However, the benefits of zero trust are substantial, offering secure access, improved compliance, and stronger overall security.
What is zero trust security?
The zero trust security model follows the principle of "never trust, always verify." This means users and devices are not automatically trusted just because they are inside the network. This approach helps prevent breaches.
Due to its complexity, implementing zero trust can be challenging, often requiring extensive setup or system adjustments. However, the benefits of zero trust are substantial, offering secure access, improved compliance, and stronger overall security
What is zero trust security?
The zero trust security model follows the principle of "never trust, always verify." This means users and devices are not automatically trusted just because they are inside the network. This approach helps prevent breaches.
The zero trust security: key takeaways
- Understanding zero trust security. The zero trust framework is a security strategy where trust is never assumed. Every user and device is verified, enhancing network security and preventing breaches.
- How zero trust works. Zero Trust Network Access (ZTNA) involves continuous verification, ensuring a secure and resilient network.
- Key aspects of zero trust. It's a strategic approach, not just a set of technologies. It extends beyond traditional network boundaries and involves rigorous verification throughout the network.
- Benefits and challenges of zero trust. It ensures secure access and strong network security. It also enhances compliance and endpoint security but it may be complex to implement and require frequent updates.
- Implementing zero trust security should focus on network segmentation and identity verification.
- The key elements of zero-trust architecture. User identity plays a central role in managing access rights and monitoring activity, ensuring that each person gets the right level of access. Device control helps secure network access by verifying each device. The network itself is segmented to improve control and security.
Core zero trust principles
Zero trust security is an approach that does not automatically trust any user or device inside and outside the network. It enforces mandatory checks at every access step, maintaining strict control through continuous monitoring of all activity. This ensures that security isn't just a one-time gate but an ongoing process of verification.
The key defense in the zero trust model is thorough authentication and re-authorization for every access request. It’s a radical shift from previous models that trusted connections based solely on their location within a network. With digital transformation making boundaries increasingly vague, relying on a traditional network perimeter for security is outdated. In modern enterprise IT environments, a device being inside the perimeter doesn’t make it trustworthy. Zero trust treats all traffic as untrustworthy—whether it originates from inside or outside—enforcing stricter controls for each user regardless of where they connect from.
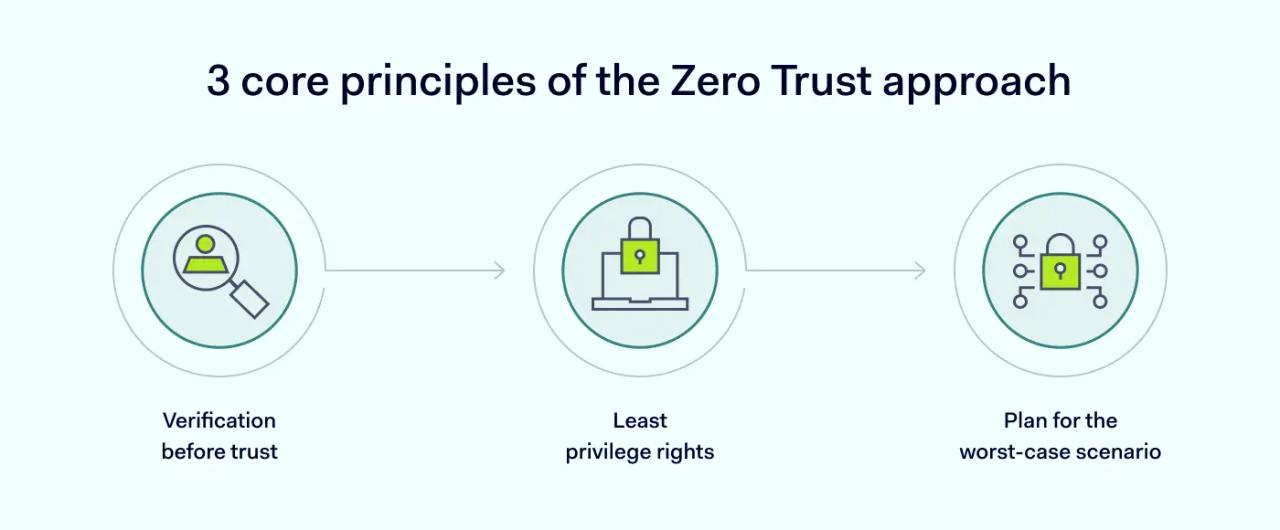
1. Verification before trust: every time a user or a device connects, their access rights must be verified.
2. Least-privilege access: users should be given only the access rights they need for their job. Additional rights should be granted only when necessary.
3. Assume breach: consider a data breach a real threat and reduce the attack surface as much as possible.
Pros and cons of zero trust security
The core of zero trust is built on the idea that no entity—inside or outside the network—should be granted access until it is fully authenticated. By removing assumed entry points, you create a more resilient defense for your team, data, and organization. Here are the main zero trust benefits:
- Cloud adaptability. Zero trust offers a dynamic and scalable solution tailored for cloud-based networking, aligning with modern business needs.
- Remote access compatibility. Zero trust ensures secure and efficient operations for organizations embracing remote work, regardless of location.
- Efficiency through SSO. Single Sign-On (SSO) simplifies access management, enhancing productivity by consolidating authentication across services.
- Centralized visibility. Gives IT and security teams comprehensive network activity and user behavior oversight, facilitating proactive security management.
- Strong security measures. Incorporates encryption, privileged access management (PAM), microsegmentation, and continuous monitoring to fortify defenses against cyber threats.
- Compliance and audit readiness. Streamlines compliance efforts with enhanced data security and clear audit trails, which can help reduce the regulatory burden.
Despite its many benefits, zero trust also has drawbacks. Here are some common zero trust challenges:
- Complex implementation: transitioning to a zero trust model requires careful planning and execution to minimize disruption and ensure continuity.
- Security strategy overhaul: adopting zero trust requires a thorough review of existing security protocols to prevent potential vulnerabilities during the switch.
- Legacy system compatibility: integration with older applications may present challenges, requiring strategic updates or replacements to maintain security integrity.
- Initial investment: the upfront costs of adopting zero trust can be significant.
How does the zero trust model work?
In practice, the zero trust model works by treating every access request as a potential risk. Instead of a one-time login, the system constantly evaluates context: is the user on a known device? Are they connecting from an expected IP address?
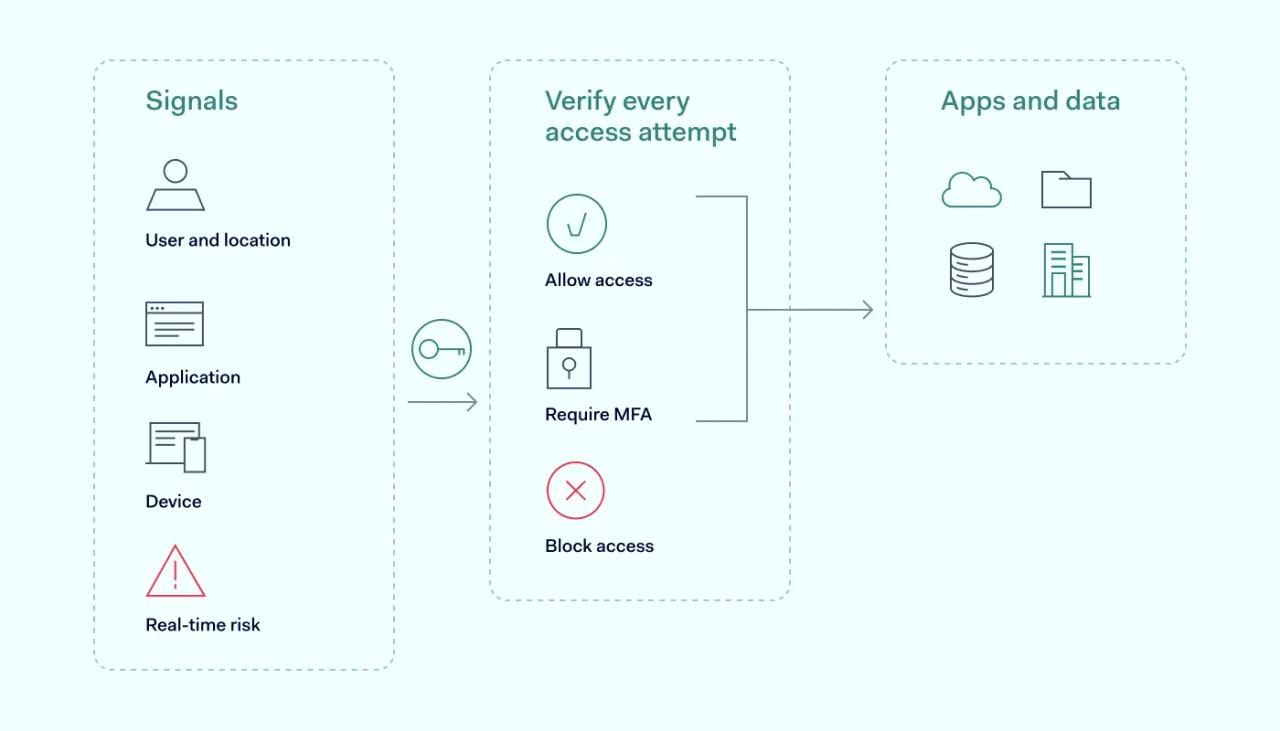
By using granular controls like multi-factor authentication (MFA) and the principle of least privilege (PoLP), the model ensures that users only access the specific data they need for their role. This prevents a single compromised account from moving laterally through your network. It transforms your security from a static network perimeter into a dynamic, continuous evaluation of every digital interaction.
Zero trust use cases
Zero trust is an adaptable security framework that addresses a wide range of modern cybersecurity challenges, making it ideal for various organizational needs. Whether you're managing a complex digital infrastructure or safeguarding sensitive data, zero trust can provide robust security solutions tailored to specific scenarios.
- Protecting multi-cloud & hybrid environments. As businesses increasingly adopt multi-cloud and hybrid cloud architectures, securing these diverse environments becomes critical. Zero trust ensures consistent security across different platforms, verifying every access request regardless of where it originates and protecting your assets from both external and internal threats.
- Mitigating ransomware & supply chain attacks. Ransomware and supply chain breaches are among the most significant threats today. Zero trust helps mitigate these risks by enforcing strict access controls, continuous authentication, and microsegmentation, preventing lateral movement within your network and minimizing the impact of such attacks.
- Securing remote workforces. With remote work becoming the norm, organizations face the challenge of securing a dispersed workforce. Zero trust offers secure access control for remote employees, ensuring that only authenticated and authorized users can access company resources, no matter where they are located.
- Enhancing compliance & data protection. For industries with stringent compliance requirements, Zero trust simplifies the process by enforcing security policies that align with regulations like PCI DSS and NIST SP 800-207. By isolating sensitive data and ensuring that all connections are secure and monitored, zero trust can also help organizations meet standards such as PCI DSS.
- Managing third-party access. Organizations often need to provide access to third-party vendors, contractors, or partners. Zero trust enables secure, least-privilege access, ensuring that external parties can only access the resources necessary for their roles, reducing the risk of unauthorized data exposure.
Zero-trust architecture and its requirements
Zero trust principles provide IT teams with a practical framework for infrastructure planning and security strategy. By using this approach as a core design philosophy, teams can implement specific zero trust strategies and network components that enforce strict, granular access control across the entire organization.
Zero trust network access offers a more flexible alternative by verifying users and devices without relying on network location alone.
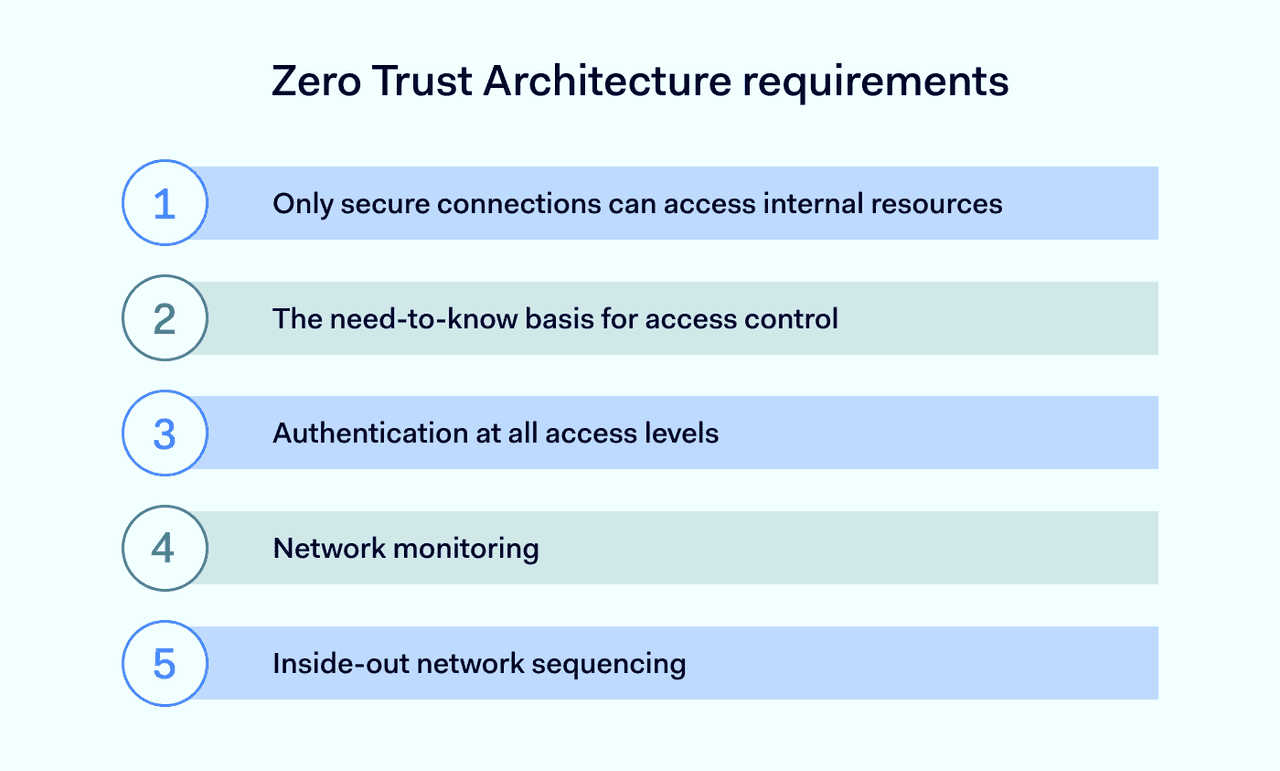
Some requirements apply when building a zero trust network:
1. Only secure connections can access internal resources
Technologies like VPNs and zero trust network access (ZTNA) can help encrypt data in transit, preventing hijacking. This ensures that only verified connections interact with your network. By doing this, the integrity and confidentiality of data are maintained, safeguarding against external threats.
2. Need-to-know basis for access control
Granting only limited access rights prevents privilege escalation and limits potential damage from compromised accounts. This access strategy minimizes risk exposure and ensures that users can only reach the information essential for their roles.
3. Authentication at all access levels
Users must authenticate at network entry and undergo additional checks for specific data, reinforcing security at each step. This multi-layered approach, deeply rooted in user identity verification, ensures that each interaction within the network is validated, adding depth to the security protocol.
4. Network monitoring
Constant surveillance of your network detects unusual behavior, helping to prevent breaches before they escalate. This ongoing vigilance allows for quick response to threats and continuous adaptation of security measures.
5. Protect high-value resources first
Start with stringent controls inside the network, then apply these rules outward, ensuring a solid core that's progressively secured. It first fortifies the most critical assets, then layers security outward, creating a comprehensive protective shield.
These zero trust principles work together to add extra checks, making it harder for attackers to get into the network. Even if they breach the perimeter, strict authorization controls limit what they can reach.
Trends like using personal devices for work (BYOD) and remote work have boosted the popularity of zero trust. Its design is evolving as more people connect from outside the traditional network. In 2021, the U.S. government started requiring zero trust across all departments, and it's useful for companies dealing with sensitive data.
Zero trust is a forward-thinking strategy that's set to grow in importance, helping to protect against threats from both inside and outside an organization.
6 pillars of zero trust
The zero-trust architecture (ZTA) model is grounded in six fundamental pillars that support a strong zero trust strategy.
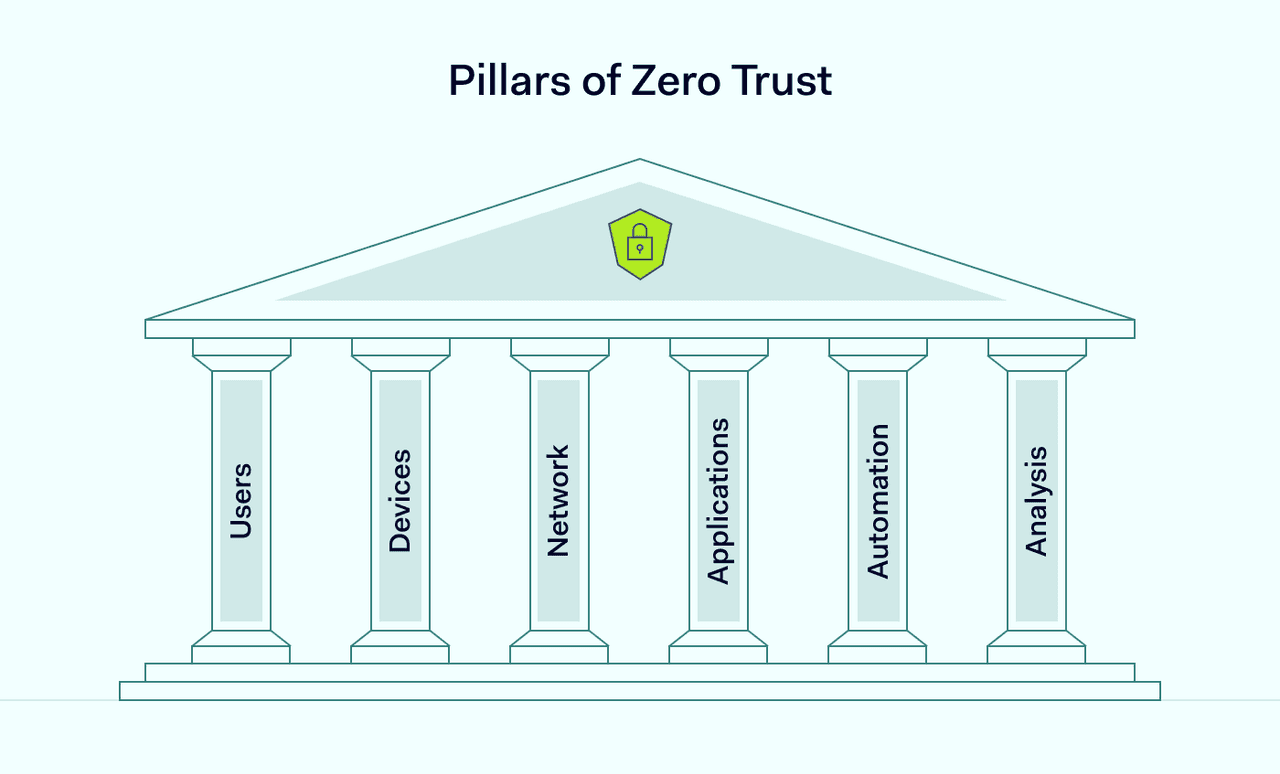
#1 Users
Users are crucial in the zero trust framework as they can be targets for cyber-attacks. It's important to manage their access rights carefully, limiting them enough to secure the network but not so much that it hinders their work. This requires strong authentication tools and ongoing monitoring.
#2 Devices
With more devices connecting to networks, controlling each device is vital in zero trust. This means possibly removing devices that pose a threat and using methods like allowlisting to permit only certain devices on the network.
#3 Network
Network administrators should segment internal networks into smaller subsections to ensure better oversight and control. Access should be limited to only those users who need specific resources. With micro-segmentation and data-focused approaches, the zero trust approach focuses more on protecting data than just securing the perimeter.
#4 Applications
Applications should be monitored, and their use should be controlled within the company's network and the cloud. Controlling access at the application level is paramount when implementing the zero trust model. Each application used within an enterprise is a potential attack vector and shouldn't be overlooked.
#5 Automation
Automated monitoring and controlling application use within the network and cloud are essential. Automation helps detect suspicious behavior and real-time threats faster. Each application is a potential risk, so controlling access at this level is crucial in zero trust. Automation also frees up admins' time for more complex tasks.
#6 Analysis
Tools like security information and event management (SIEM) and user and entity behavior analytics (UEBA) provide insights into network activity. Regardless of network location, device, and user count, better visibility also contributes to stronger overall security.
This helps in preparing for threats, not just reacting to them. The difference between zero trust and traditional security is often largely invisible to users, as most changes happen behind the scenes.
How to implement zero trust
Implementing zero trust shifts your approach from trusting anyone inside the network to verifying everyone, every time, ensuring a single compromised set of credentials doesn't turn into a company-wide crisis. To get started, focus on these core best practices:
- Map your data and assets. Identify where your sensitive information lives and who actually needs access to it.
- Enforce least-privilege access. Give employees access only to the specific systems they need for their roles. This limits the potential damage if an account is ever compromised.
- Require multi-factor authentication (MFA). Even if a password ends up on a dark web forum, MFA can stop an unauthorized login in its tracks.
- Monitor in real time. Use tools that detect suspicious activity early and help your team respond before attackers can use stolen credentials or compromised accounts.
While these are the foundational first steps toward a more resilient defense, they create the necessary baseline to eventually move toward more automated, context-aware security.
NIST 800-207 and zero trust
In 2020, the National Institute of Standards and Technology (NIST) released Special Publication (SP) 800-207, a guide to zero-trust architecture. This guide explains that zero trust focuses on protecting users, assets, and resources rather than relying on network location alone. Here are some of the key ideas it highlights:
- Use policy-based access controls.
- Break the network into segments with their own rules and access policies.
- Verify identities and adjust access based on context.
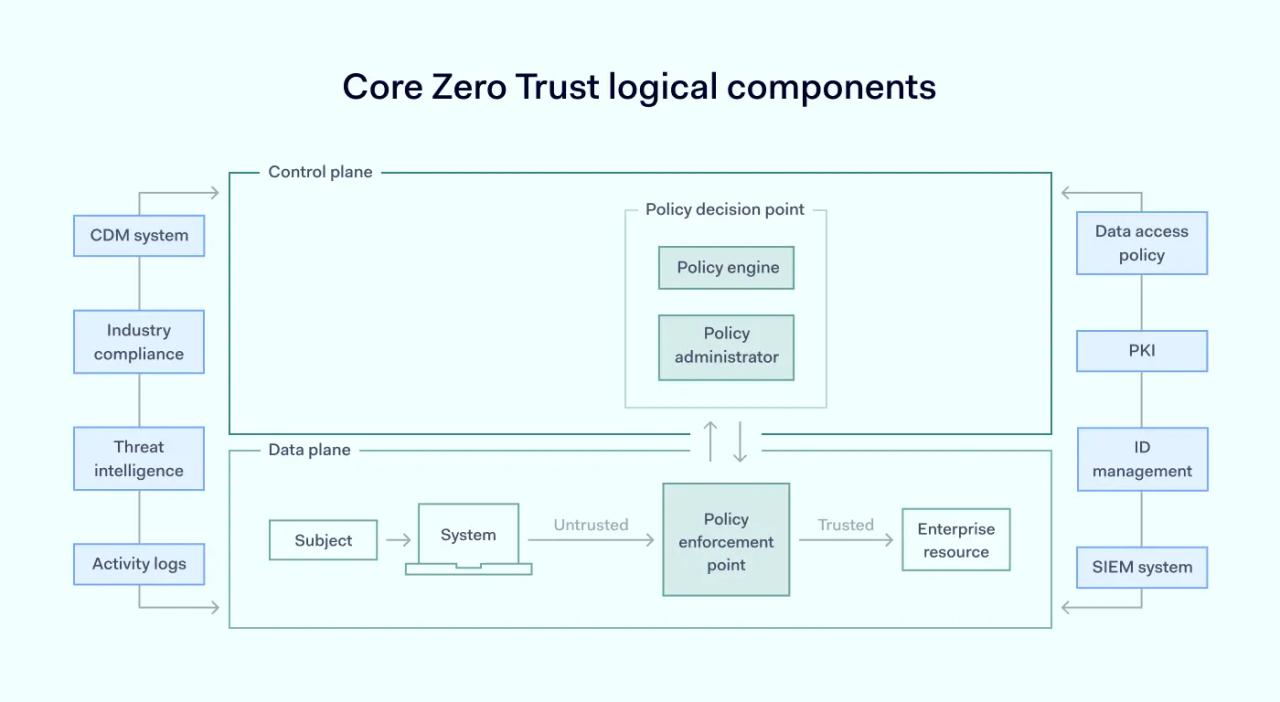
A zero-trust architecture deployment in a business consists of several key parts. These can be managed either on-site or through cloud services. This basic model below shows how these parts interact:
In this ideal setup, the policy decision point is split into two parts: the policy engine and the policy administrator. ZTA's components communicate via a separate control channel, while the application data moves through a different channel.
Here is how these components of zero trust work:
- Policy engine: allows or denies the user access to company resources.
- Policy enforcement point (PEP): monitors connections between users and company resources.
- Policy administrator: acts as an intermediary between the policy engine and PEP. It sends commands to PEP depending on the policy engine's decision.
It's important to note the flexibility in the implementation of these components. They don't have to be separate entities; they can be integrated into a single asset. Conversely, several different assets might handle just one component.
Zero trust security for enterprises
Implementing zero trust in your business means rethinking how you manage users, applications, and infrastructure. It involves seeing users as both potential risks and assets, with a focus on robust identity verification and limited access.
The zero trust approach also shifts the emphasis from broad network connectivity to controlled application and resource access, which helps minimize the attack surface. In this model, infrastructure primarily facilitates connectivity, while security depends on clear access policies and continuous verification.. This strategic shift aligns well with modern cybersecurity challenges, making it a smart business move.
Discover NordLayer's zero trust solutions to explore how this approach can be integrated into your business, helping improve overall security.