The HIPAA Minimum Necessary Standard is a key component of HIPAA regulations. It requires covered entities to make reasonable efforts to limit access to physical or electronic protected health information (PHI) to only what is necessary.
Although HIPAA doesn’t define "minimum necessary information" or "reasonable efforts," the rule means that covered entities can only share necessary parts of PHI upon request. Based on the situation, they must decide what specific information can be disclosed or restricted.
Additionally, any decision to disclose or limit access to PHI should always be backed by a clear and logical justification.
The HIPAA Minimum Necessary Rule Standard Definition
The HIPAA Minimum Necessary Rule Standard applies to the use, sharing, and requests for protected health information (PHI) allowed by the HIPAA Privacy Rule. It ensures that covered entities use and disclose only the necessary amount of PHI.
How does the HIPAA Minimum Necessary Rule Standard work?
The HIPAA Minimum Necessary Rule Standard requires covered entities to make reasonable efforts to limit the use, sharing, or requests for protected health information (PHI) to only what's necessary. This applies to all situations involving PHI, such as names, birth dates, diagnoses, treatment notes, and electronic PHI (ePHI) like digital medical records.
Only those who need the information to do their jobs should have access to it. For example, in a clinic with multiple health care providers, only the one treating the patient should access their records.
Here are some examples of how the HIPAA Minimum Necessary Rule Standard works:
- A doctor can access patient records but not sensitive information like Social Security numbers or billing details unrelated to treatment.
- A billing specialist can see the name of a test a patient had but not the results.
- An insurance company can only obtain information relevant to a specific claim, not the patient's entire medical history.
- A physician cannot share a patient's diagnosis with unauthorized personnel or third parties
When does the HIPAA Minimum Necessary Rule Standard apply?
The HIPAA Minimum Necessary Rule Standard applies to all HIPAA-covered entities and health care providers, such as:
- Hospitals
- Insurance companies
- Healthcare clearing houses
The standard mandates that these entities limit their use or disclosure of Protected Health Information to the minimum required. This applies to all forms of PHI, whether digital or physical, like files on USBs and laptops.
For instance, in a clinic with multiple health care providers, only a physician treating the patient should access their records. Similarly, if a hospital's coding department needs patient information for pre-authorization, they should only access the necessary details.
This standard also extends to communications between staff and patient interactions. It ensures that only essential PHI is shared, safeguarding patient privacy across various platforms.
Exceptions to the HIPAA Minimum Necessary Standard
Every rule has an exception, and the HIPAA Minimum Necessary Standard is no different. There are six exceptions where it doesn’t apply:
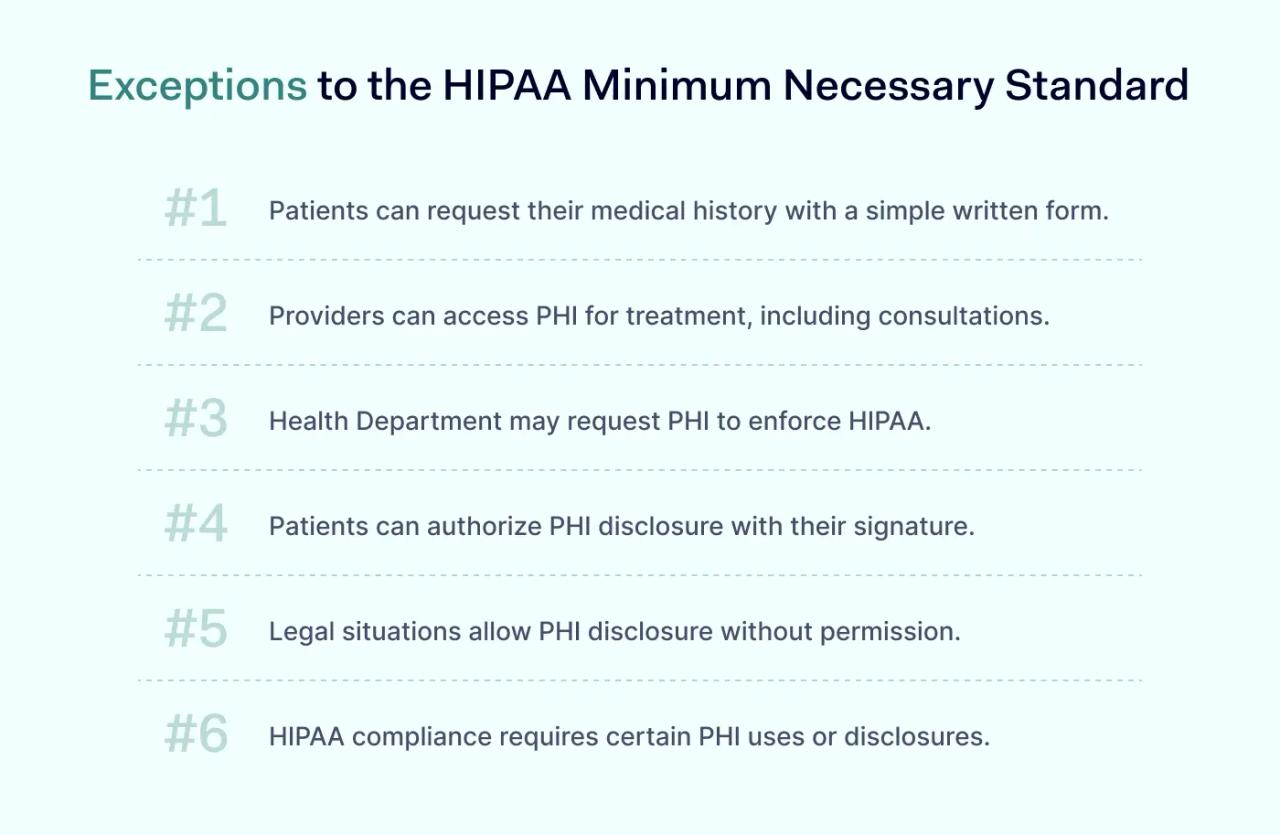
#1 Patient's access to their medical history
Patients have the right to access their own PHI. They can do it by making a written request with reasonable criteria.
#2 Treatment of a patient
A health care provider may access a patient's PHI to treat the patient. This also applies to consultations between providers regarding the patient’s care.
#3 HIPAA rules enforcement
The Department of Health and Human Services may request PHI disclosures based on HIPAA regulations, such as the HIPAA Enforcement Rule.
#4 Patient’s consent
When a patient gives written authorization, they can allow a covered entity to disclose or use their PHI.
#5 Requests required by law
HIPAA-covered entities may disclose PHI without consent if required by law, such as in cases of adult abuse, neglect, or domestic violence.
#6 Requests required for HIPAA compliance
PHI may be disclosed for compliance with the HIPAA Administrative Simplification Rule, which ensures smooth electronic communication and data exchange across the U.S. healthcare system.
Best practices for implementing the Minimum Necessary Rule Standard
While the Minimum Necessary Standard may seem straightforward, implementing it requires careful planning. Below is a list of the most effective strategies.
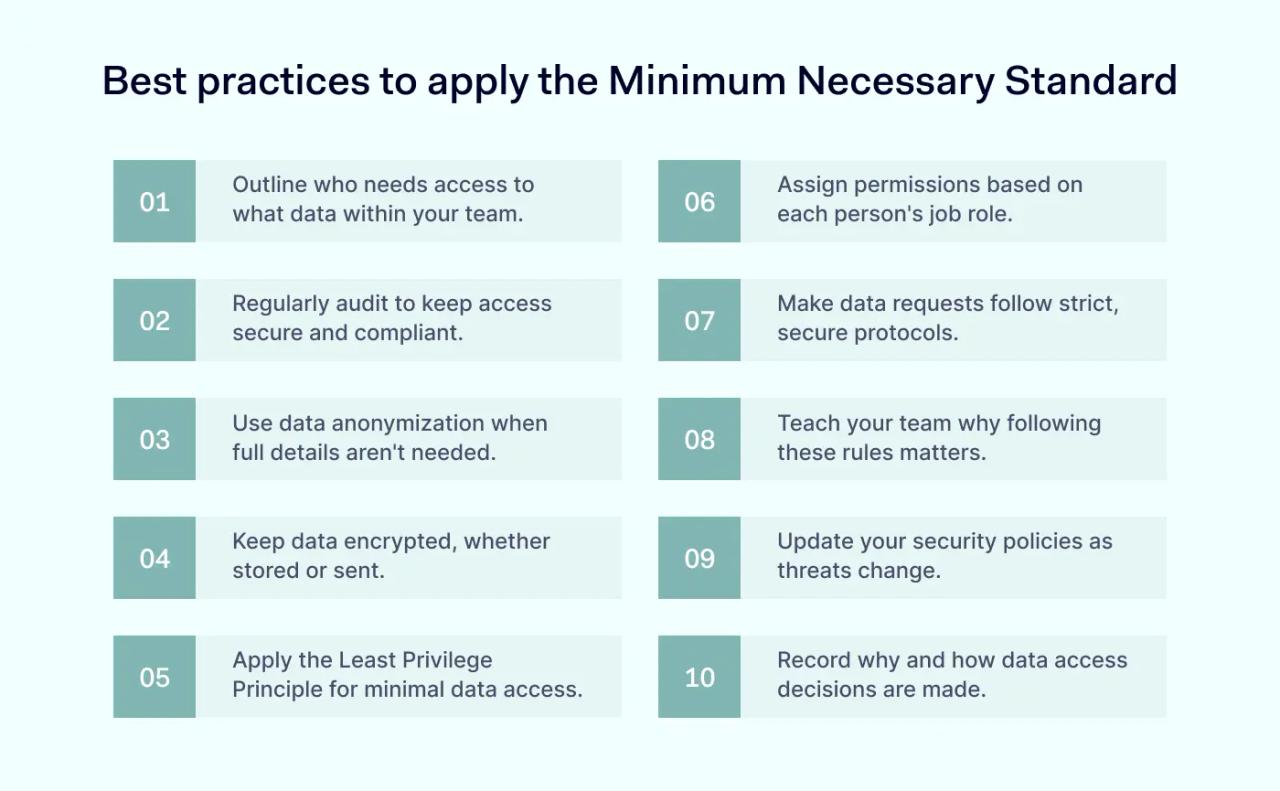
1. Define scope and access criteria
Begin by defining which data is necessary for specific roles within your organization. Not everyone needs access to all information. For example, a health care provider may need to see a patient's medical history, but not their financial details.
2. Use role-based permissions
Implement role-based access control (RBAC) to grant permissions according to the user's role. It's like giving a chef access to the kitchen but not the entire restaurant.
3. Regular audits
Conduct regular audits to ensure compliance. It's like checking door locks regularly–it ensures that only authorized personnel have access.
4. Tighten data request protocols
Establish strict protocols for requesting data. Ensure requests go through a secure process, similar to having a single, guarded entrance to a facility.
5. Use data anonymization techniques
When full access to data isn't necessary, anonymize it. Think of it as blurring out faces in a crowd—you can still estimate the crowd's size without identifying individuals.
6. Train your staff
Educating your team on the importance of the HIPAA Minimum Necessary Rule Standard is like teaching drivers about respecting speed limits for safety. All employees and business associates should understand HIPAA compliance.
7. Encrypt data
Ensure data is encrypted both in rest and in transit—a strategy comparable to sending sealed letters instead of postcards.
8. Update policies regularly
Regularly update your policies to adapt to changing threats and data use cases.
9. Employ the Least Privilege Principle
Give users the minimum level of access needed to do their jobs—just like carrying a key to just one office, not the entire building.
10. Document procedures and rationale
Keep clear records of data access procedures and the reasons behind them. It's like using a guestbook at a private event to track who accessed what and why.
Before implementing the HIPAA Minimum Necessary Rule Standard, ensure your organization has established policies that define:
- Who can access sensitive data to perform their duties
- The categories or types of PHI accessible
- The appropriate conditions for access
It’s also crucial to define any exceptions, who they apply to, and under what circumstances.
How often is the HIPAA Minimum Necessary Rule Standard violated?
The exact frequency of violations of the HIPAA Minimum Necessary Rule isn't really documented. However, according to HHS Enforcement Highlights, these violations are the fifth most common type of non-compliance. They not only jeopardize the privacy of patient information but can also disrupt health insurance portability, making it difficult for individuals to transfer their coverage seamlessly between providers.
It’s unclear who reports these violations—whether they are self-reported by the entities involved or reported by patients or health plan customers.
So, when do violations of the HIPAA Minimum Necessary Rule Standard happen?
- A doctor may need access to a patient's medical records for treatment but could accidentally view sensitive data, such as the patient’s Social Security number or payment details.
- A gynecologist may share information about a celebrity patient's pregnancy with a colleague during lunch. If this information is overheard by others, such as a cafeteria worker, it counts as a violation.
- An IT professional working on a hospital's database might click on patient medical files without permission while performing maintenance.
- A nurse might disclose information that a patient has hepatitis C in a public area, which could be overheard by other patients. If this happens, the patient can file a complaint about the unauthorized disclosure of their PHI.
These examples illustrate common scenarios where violations can occur, highlighting the importance of safeguarding sensitive patient information.
The effects of sharing more than the minimum necessary PHI
The consequences of sharing more than the minimum standard PHI are serious. Apart from financial penalties, organizations lose their reputation, patient trust, and their ability to operate a business.
For instance, Filefax, a medical storage company, agreed to pay$100,000 to settle potential HIPAA violations of the HIPAA Privacy Rule. Although Filefax ceased its operations during the Office for Civil Rights investigation, it still faced additional fines and penalties.
While the Privacy Rule does allow for incidental or accidental disclosures, it’s key to understand the difference between these two.
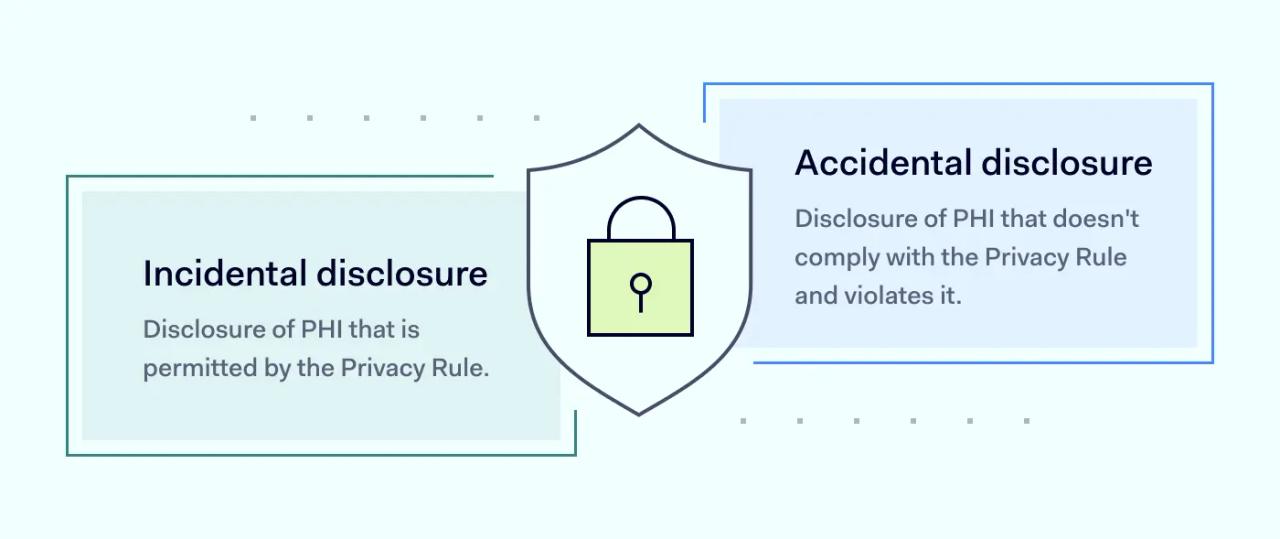
For example, an authorized physician accidentally shares the wrong patient's PHI with another authorized physician. This accidental disclosure breaks HIPAA rules.
On the other hand, incidental exposure might occur when someone visiting a relative in the hospital inadvertently sees another patient's X-ray displayed on a monitor or overhears nurses discussing another patient’s condition. These situations represent incidental access to Protected Health Information.
Disclaimer: This article is for informational purposes only and not legal advice. Use it at your own risk and consider consulting a licensed professional for legal matters. Content may not be up-to-date or applicable to your jurisdiction and is subject to change without notice.