Summary: Endpoint encryption secures data by making it unreadable without a decryption key, protecting lost or stolen devices from breaches. Learn how it works.
A stolen company device can result in data theft. Endpoint encryption solutions are a key defense against this risk, ensuring that sensitive information remains inaccessible to unauthorized parties. By converting data into ciphertext, this security layer renders files unreadable without the correct decryption key.
While encryption won’t fix every security threat, it’s the ultimate safety net for your data if a phone or laptop ends up in the wrong hands.
In this guide, we break down what endpoint encryption is, compare the main encryption types, and provide a roadmap for a successful enterprise-wide rollout.
What is endpoint encryption?
Endpoint encryption is a process that scrambles or encodes data stored on endpoints, making it useless to unauthorized users without the correct decryption key. It functions through full-disk encryption or file/folder-level encryption. It ensures data remains secure even if the device where it’s stored is stolen or falls victim to an "evil maid" (a physical tampering) attack.
How does endpoint encryption protect sensitive data?
Endpoint encryption software transforms data into an unreadable ciphertext using symmetric algorithms such as the Advanced Encryption Standard (AES). Asymmetric algorithms like Rivest-Shamir-Adleman (RSA) may be used to protect or exchange the encryption keys. When data is saved to a device, the encryption algorithm scrambles the information, ensuring it remains inaccessible to anyone without the correct decryption key.
Both AES-256, ChaCha20, and RSA algorithms are publicly documented standards. They, however, serve different purposes:
AES-256 (symmetric encryption). AES-256 is used for
data at rest (for example, on hard drives). It replaced the older Data Encryption Standard (DES), which is more vulnerable to brute-force attacks.
ChaCha20 (symmetric encryption). ChaCha20 is also a symmetric cipher and is commonly used to protect data in transit in modern protocols (for example, TLS and VPNs).
RSA (asymmetric encryption). Primarily used to protect or exchange encryption keys (and enable digital signatures), RSA uses a dual-key system—one to encrypt and a separate recipient key to decrypt.
Close the endpoint-to-network gap for SMBs with ease
Types of endpoint encryption
There are two primary methods for securing device data: full-disk encryption (FDE), which encrypts the entire operating system and hardware, and file, folder, and removable media (FFRM) encryption, which selectively protects specific sets of data.
Full-disk encryption (FDE)
FDE encrypts the entire hard drive, i.e., the operating system (OS), all user data, and system files, except for the small boot components needed to start the system. This allows the device to boot and load what’s needed for unlocking the system. This prevents unauthorized users from accessing data when an endpoint is lost or stolen.
In FDE, data is decrypted after a user is authenticated and the system has booted. Here are the methods for authenticating a user:
The drive boots into the OS, and a user signs in with credentials before accessing data.
Pre-boot authentication requires a PIN or credentials before the OS loads. The data stays encrypted until authentication is finished.
Related articles

Agnė SrėbaliūtėOct 22, 20248 min read

Joanna KrysińskaDec 18, 20258 min read
File, folder, and removable media encryption (FFRM)
FFRM provides selective control, allowing for encryption of specific sensitive documents or folders, depending on the organization’s security policies. It can help keep individual files protected when shared across networks or stored in cloud services, depending on how encryption keys and access policies are managed. In FFRM, data is encrypted until a user opens it. This means the encrypted file is safe, even if it is shared via email, because a recipient will need a proper decryption key to access it.
| Full-disk encryption (FDE) | File/folder-level and removable media encryption (FFRM) |
|---|
| The entire hard drive, including the operating system, system files, and all user data | Selected files, specific folders, or removable media |
|---|
| Lost or stolen laptops/devices | Sensitive documents or data shared across networks or stored in the cloud |
|---|
| | |
|---|
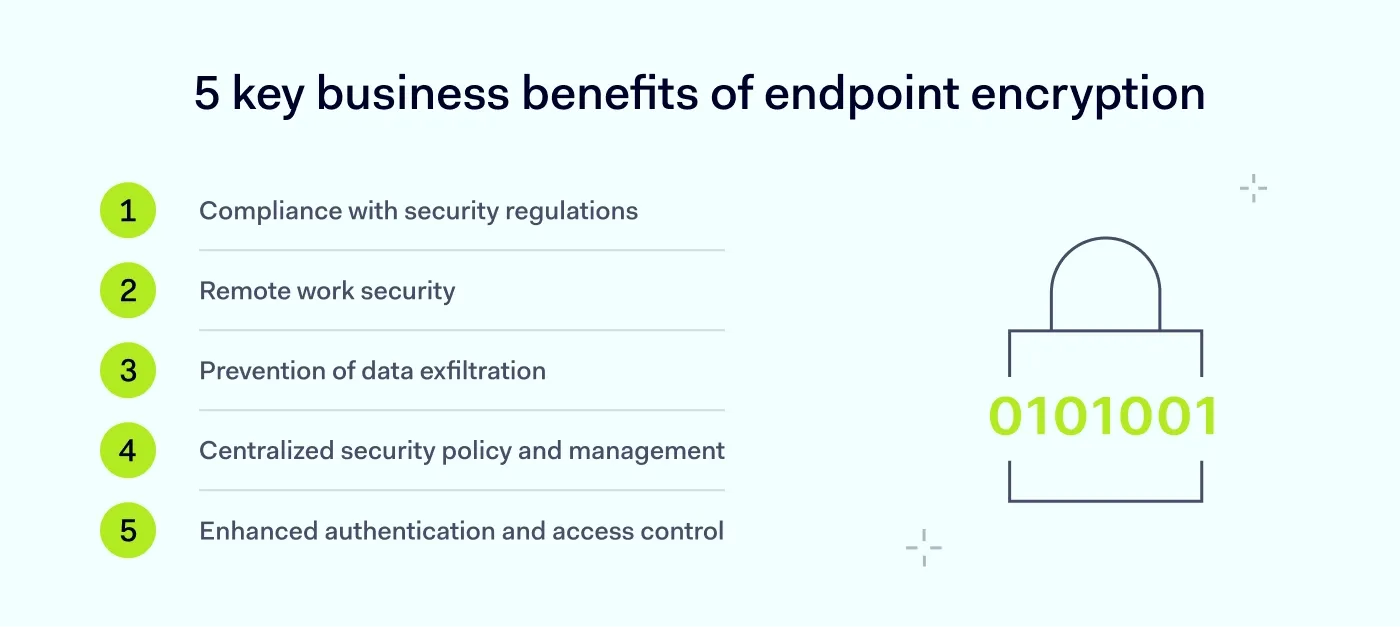
5 key business benefits of endpoint encryption
Investing in endpoint encryption isn’t just about ticking a box. It’s a strategic move that protects your sensitive data. Here are 5 reasons why businesses should prioritize device-level encryption.
Benefit #1: compliance with security regulations
Encryption is now a core legal requirement for handling sensitive data. Major frameworks like the Health Insurance Portability and Accountability (HIPAA), General Data Protection (GDPR), or Payment Card Industry Data Security Standard (PCI-DSS) require strict data protection measures that include encryption.
But beyond just following the rules, implementing endpoint encryption may also reduce reporting obligations in some jurisdictions (sometimes called the “safe harbor” effect). For example, if a lost laptop is fully encrypted, it may not even count as a reportable breach under certain rules, helping you to avoid fines and legal exposure.
Benefit #2: remote work security
Remote work often involves accessing sensitive company data from homes, cafés, or airports. Adopting encryption helps protect sensitive data in public spaces from physical and network threats. This includes risks like juice jacking, a threat where cybercriminals use public USB charging stations to install malware or attempt to export sensitive data from your device. If your endpoint is encrypted, you add a critical layer of protection that keeps stored data inaccessible even if the device is lost or accessed without authorization.
Benefit #3: data security
According to Infosecurity Magazine, drive and device thefts (41%) actually trigger more data loss than ransomware (32%). That’s why endpoint encryption is a critical line of defense. Even if a threat actor steals an encrypted device, the data remains inaccessible as scrambled, indecipherable code. This prevents not only data exposure but also unauthorized data exfiltration.
Benefit #4: centralized security policy and management
Endpoint encryption provides granular visibility and control over encryption protocols across all endpoints. Beyond simply protecting data, it monitors logging status and activity of every hard disk or removable media encryption application in one place. It also automates security policy enforcement and provides immediate response capabilities in the event of a breach.
Benefit #5: enhanced authentication and access control
Endpoint encryption enforces robust access requirements, ranging from complex passwords to multi-factor authentication (MFA). This ensures that data remains accessible only to verified users. Beyond simple login security, it provides critical pre-boot protection that helps prevent access to stolen devices before the operating system even loads.
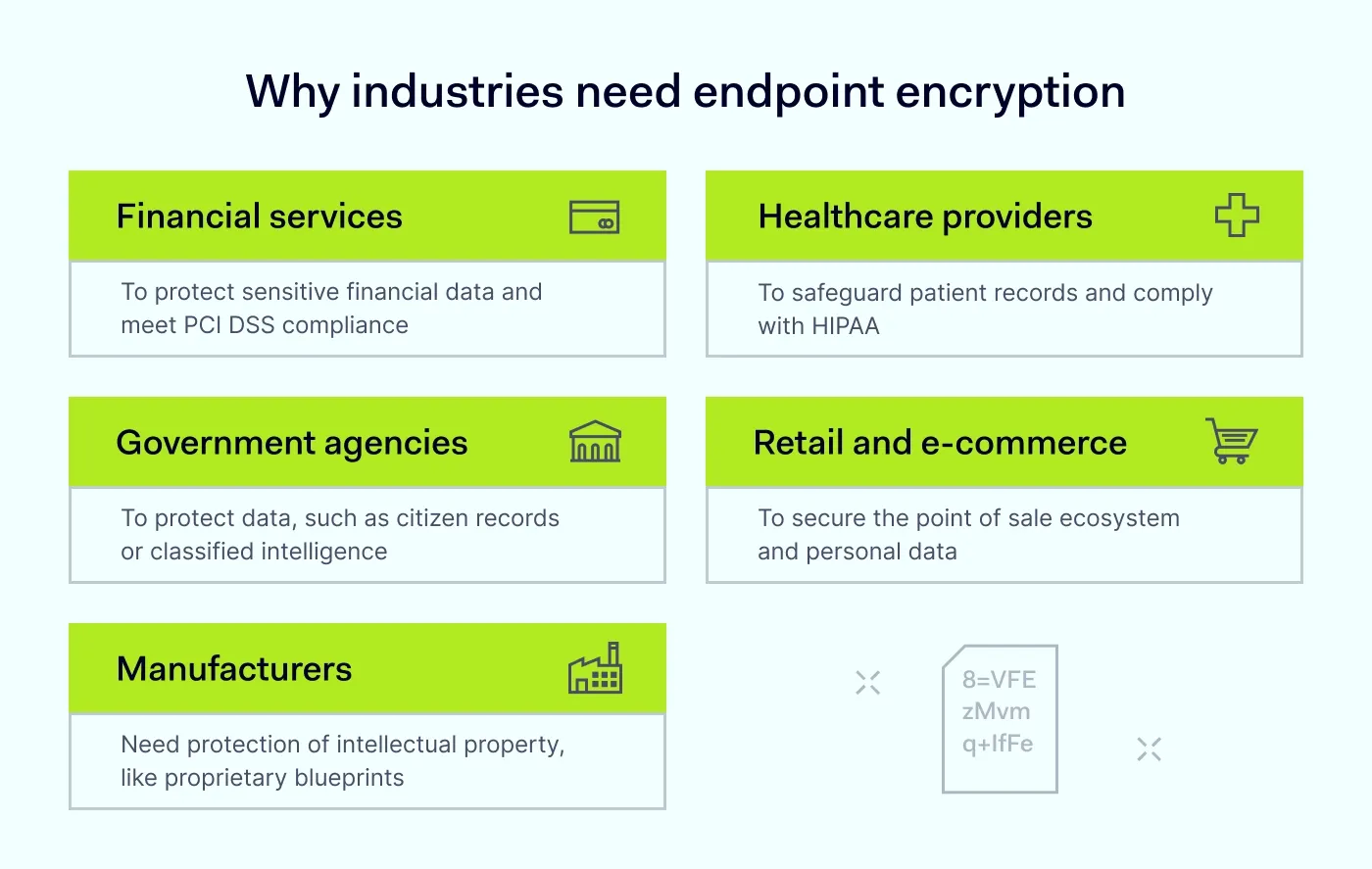
Practical applications: how industries use endpoint encryption
Endpoint encryption is a foundational requirement across diverse sectors, each facing unique regulatory and security challenges.
Financial services. Institutions must protect highly sensitive data like account numbers, credit card details, or personal information. Endpoint encryption can help meet
PCI DSS compliance and defend against targeted credential theft.
Healthcare. Healthcare providers handle large amounts of patient records and also need to comply with
HIPAA regulations. Endpoint encryption is a vital safeguard against data exposure resulting from intercepted or lost devices.
Government agencies. Processing everything from citizen records to classified intelligence, government bodies use endpoint encryption to ensure data security and prevent unauthorized access to it.
Retail and e-commerce. With the constant flow of credit card data and personally identifiable information (PII), retailers use endpoint encryption to secure the point-of-sale ecosystem and mitigate the risk of breaches.
Manufacturing. Manufacturers need to protect intellectual property. Deploying endpoint encryption helps them shield proprietary blueprints and industrial designs from corporate espionage and unauthorized access by competitors.
While these represent primary use cases, any organization handling proprietary and sensitive data can use endpoint encryption to build a resilient, multi-layered defense. This way, businesses can neutralize threats before they result in a catastrophic data loss.
Enhancing endpoint security with CrowdStrike and NordLayer
For small and medium-sized businesses, implementing endpoint encryption solutions is a survival tactic. By combining NordLayer’s network defense with CrowdStrike’s industry-leading technology, you can protect your sensitive data from the network level all the way to the individual device.
The NordLayer and CrowdStrike partnership offers comprehensive endpoint protection tailored to SMBs. CrowdStrike provides AI-driven threat detection and intelligence to secure your endpoints, and gives you full visibility and control over device activity, helping mitigate risks such as malware or unauthorized peripheral use.
NordLayer’s Business VPN encrypts network traffic routed through secure tunnels to protect your data and employee privacy, and Zero Trust Network Access (ZTNA) verifies every user and device before they are granted access to private resources.
This layered approach ensures that even if a device is lost or a remote connection is targeted, your data remains an unreadable "secure island."
By choosing this integrated bundle, you reduce the risk of a data breach. It’s a professional, high-performance way to ensure that as your business grows, your security remains one step ahead of threat actors.

Joanna Krysińska
Senior Copywriter
Joanna's family has a history in math and engineering, and she has dedicated her life to simplifying complicated technical ideas. She helps people understand how hackers think and how to stay ahead of them by concentrating on the human side of cybersecurity.