Summary: Learn OpenClaw security best practices to reduce risk, protect AI environments, and safely manage agent access, integrations, and automation workflows.
AI tools have moved past answering questions. They act, remember, and make decisions. People today expect these technologies to follow through, not just respond, and tools like OpenClaw are starting to do that.
OpenClaw allows an AI agent to interact directly with systems, data, and workflows, often operating within your local machine or connected environments. That level of access changes the balance: the same capabilities that enable automation can also expand your attack surface.
Without the right safeguards, organizations risk exposing sensitive data, mishandling API keys, or leaving themselves vulnerable to threats like prompt injection.
In this guide, we’ll break down what OpenClaw is, outline key risks, and walk through practical steps to strengthen your OpenClaw setup and overall security.
Key takeaways
OpenClaw shifts AI from passive responses to real-world execution, meaning the agent can directly impact systems, data, and workflows.
The biggest risks don’t come from the tool itself, but from how access, permissions, and integrations are configured.
Threats like prompt injection can turn simple inputs into unintended actions, especially in loosely controlled environments.
OpenClaw security best practices focus on limiting access, isolating the agent environment, and reducing overall exposure.
Maintaining a secure setup requires continuous visibility: through monitoring, network controls, and clearly defined boundaries for how agents operate.
What is OpenClaw?
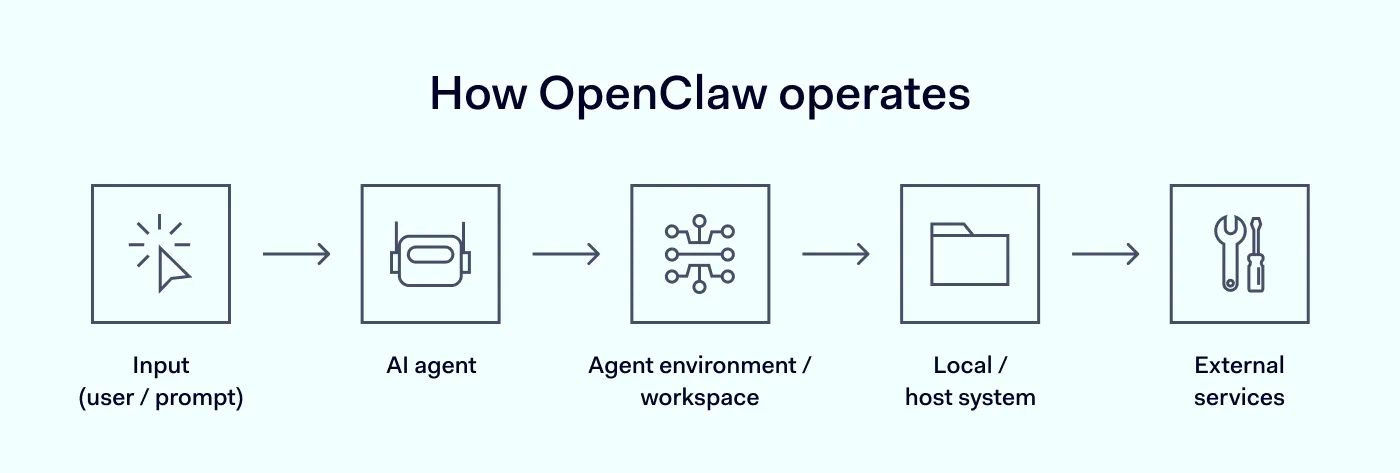
OpenClaw is one of the tools pushing LLMs beyond chat and into real tasks. Instead of generating answers, it enables an AI agent to take action inside real environments. That includes interacting with files, calling APIs (access tokens that allow systems to communicate with each other), and executing tasks that previously required direct human input.
OpenClaw connects AI models directly to operational systems—files, APIs, and tasks that previously required human input. It runs within a defined agent workspace, often close to or directly within your local environment, giving agents a level of autonomy that traditional tools don’t offer.
This design is intentional. OpenClaw operates under a model where there is typically one trusted operator boundary (you) and potentially many agents acting on your behalf. That makes it powerful, but it also means your security scope has to expand beyond data protection to agent permissions.
However, when the agent can act, not just respond, then every permission, integration, and connection becomes a potential risk vector. Understanding this shift—from passive responses to real execution—is key.
The main OpenClaw security risks
With that in mind, the real OpenClaw security risks come down to how these capabilities are used in real environments. OpenClaw amplifies existing risks and makes them easier to trigger at scale.
Prompt injection attacks. Malicious inputs can manipulate the AI into executing unintended actions, exposing data, or bypassing safeguards.
Exposed API keys. When API keys are stored insecurely or embedded within prompts, scripts, or loosely managed environments, attackers can gain access to external services.
Over-permissioned environments. Giving the agent excessive access—across files, systems, or services—increases the risk of misuse or accidental damage. This is especially risky when operating directly on a machine, where system-level access may be within reach.
Local machine vulnerabilities. Running OpenClaw directly on your host system without proper isolation can expose your system to compromise.
Data leakage. Sensitive data processed within the execution environment may be unintentionally shared, logged, or reused across tasks, creating long-term risks that are hard to trace.
Expanded attack surface. Every integration, plugin, or API connection increases risk. OpenClaw environments can quickly become complex, and without discipline, that complexity turns into a vulnerability.
If you recognize these risks early, it becomes much easier to design controls that prevent them from turning into real incidents.
Detect issues, prevent breaches
Continuously monitor threats with NordLayer
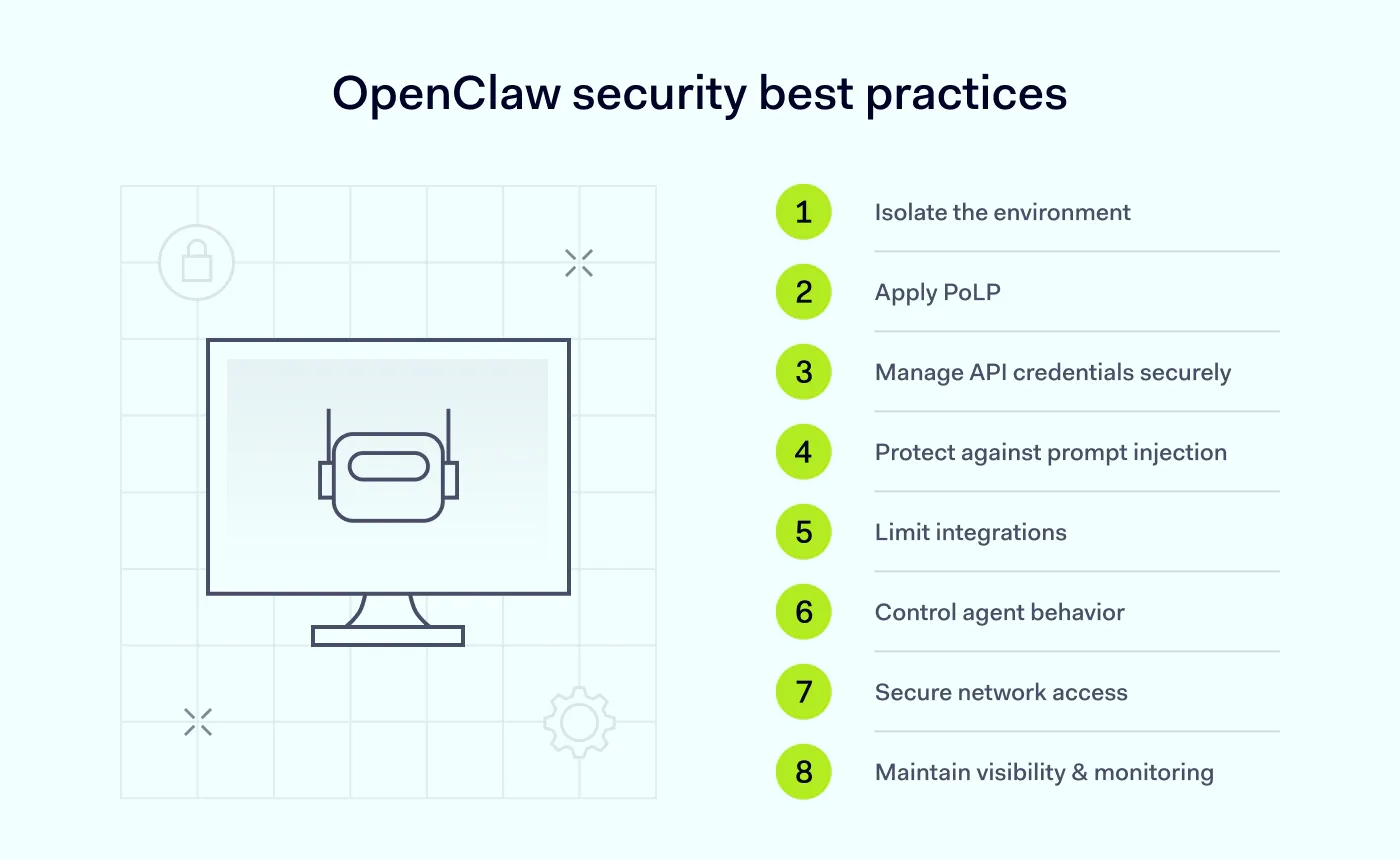
OpenClaw security best practices
Securing OpenClaw is about building layers of protection that work together across your entire environment. The best security practices for OpenClaw combine isolation, control, and visibility.
Start with strict isolation
OpenClaw should never operate in an unrestricted environment. Running it directly on your primary host system without boundaries is one of the fastest ways to introduce risk. Instead, isolate the environment:
Use containers or virtual machines
Separate the agent workspace from critical systems
Avoid giving agents access to your full file system
Additionally, configure OpenClaw to listen only on localhost (127.0.0.1). This ensures that it isn’t exposed to external networks by default and will significantly reduce the risk of unauthorized access.
Apply the principle of least privilege (PoLP) everywhere
The agent should only have access to what it absolutely needs—nothing more. This applies to file access, API scopes, and system permissions.
Over-permissioning is one of the most common mistakes. It may feel convenient in the short term, but it increases potential entry points and weakens your company’s security.
Rethink how you manage API credentials
Credentials should never be treated casually in an OpenClaw setup. Avoid embedding API keys in prompts or scripts and reusing personal or primary accounts.
Instead, use dedicated “burner” accounts for integrations. These are isolated accounts created specifically for OpenClaw use, with limited permissions and no connection to critical systems. As a rule:
Never connect your banking, primary email, or personal GitHub accounts
Store credentials securely (e.g., in vaults or as environment variables)
Rotate keys regularly
This approach limits the damage if something goes wrong.
Build defenses against prompt injection
Because prompt injection is one of the most direct ways to manipulate an agent, it needs special attention. Treat all inputs as untrusted:
Validate external data before passing it to the agent
Avoid executing instructions blindly
Introduce approval steps for sensitive actions
The most important change in thinking is this: just because the AI suggests an action doesn’t mean it should be executed.
Limit integrations to what you actually need
One of the fastest ways to lose control of an OpenClaw setup is to connect too many services too quickly. Every new integration introduces another dependency and another potential point of failure.
Instead of aiming for maximum functionality, focus on an intentional setup. Only connect services that are essential to the agent’s tasks, and regularly review which integrations are still in use. Removing unused or redundant connections simplifies your environment and reduces unnecessary exposure.
In practice, a smaller, well-defined system is much easier to secure than a highly connected one that grows without clear boundaries.
Control how and where the agent operates
Think of OpenClaw as operating within controlled boundaries, not as a free-moving system. Define what the agent can access, where it can connect, and which actions require human approval.
This approach reinforces the idea of OpenClaw as a personal assistant model, where the human operator remains the final authority.
Secure network access
Network-level protection is often overlooked, yet essential. To strengthen your setup:
Keep OpenClaw within an internal network
Apply strict firewall rules to limit traffic
Avoid exposing ports unnecessarily
If remote access is required, using a VPN can help establish encrypted connectivity without exposing the environment to the public internet.
Maintain visibility and accountability
Secure what you can’t see, too. Monitor agent activity and commands, API usage, and access to sensitive data. Logging and auditing serve as your early warning system, not just for compliance.
Together, these practices create a controlled environment where agents can operate effectively without introducing unnecessary risk.
Related articles

Agnė SrėbaliūtėMar 25, 20268 min read

Agnė SrėbaliūtėMar 31, 20268 min read
How to implement OpenClaw security in practice
Understanding best practices is one thing, while putting them into action is where most setups start to break down. In real-world environments, the biggest challenges usually fall into 3 categories: how OpenClaw is exposed to the network, how credentials are handled, and the level of control you have over agent activity.
Network isolation
The first step is reducing unnecessary exposure. OpenClaw should run in a controlled environment that is not directly accessible from the public internet. Instead of allowing open connectivity, it should rely on internal routing within a private network, where communication is limited to only the services it actually needs.
A simple but critical measure is binding OpenClaw to 127.0.0.1. This ensures that the service only accepts local connections by default and prevents unintended external access unless explicitly configured. From there, access can be carefully extended in a controlled and secure way, rather than being left open by design.
Credential management
Credentials should be treated as tightly controlled and short-lived assets, not as static pieces of configuration. Each integration should use separate accounts with clearly defined scopes instead of reusing personal or primary credentials across systems.
API keys should never live inside application logic or prompts. Instead, store them securely, such as in environment variables or dedicated vaults, and rotate them regularly. Keeping credentials isolated across environments also limits the risk of lateral movement, which ensures that if one component is compromised, the impact won’t spread across your entire setup.
Session and execution control
Sessions define how much freedom your AI agent has to operate, and for how long. Without proper boundaries, agents can act for longer periods of time and in broader ways than intended, which increases the risk of misuse.
To maintain control, session duration should be limited, especially for tasks involving sensitive data or system access. Re-authentication may be required for high-impact actions to ensure that a human remains part of critical decision-making processes. At the same time, logging and reviewing session activity provides visibility into an agent’s actual actions, not just their configured ones.
Together, these measures introduce a layer of human oversight without slowing down workflows, helping you maintain a strong security posture while still benefiting from automation.
Why human oversight matters
Even with strong technical safeguards, most security incidents still come down to people. According to a 2025 World Economic Forum report, human error is involved in 95% of breaches, often due to misconfigurations, over-permissioned access, or overlooked warnings.
In an OpenClaw setup, that risk shifts. The agent executes tasks exactly as instructed, but it doesn’t understand intent. In cases like prompt injection or complex workflows, this can lead to actions that are technically correct, but contextually wrong.
That’s why, instead of relying on full autonomy, define clear checkpoints for sensitive actions, such as accessing critical data or executing system-level commands.
OpenClaw works best not as a fully independent system, but as a controlled extension of human decision-making. Keeping a person in the loop helps catch what automation alone might miss.
How to monitor OpenClaw for security threats
Even a well-configured system needs continuous monitoring. Threats don’t always come from obvious failures—they often emerge from subtle, unexpected behavior.
Start by tracking activity within the agent environment. Every command, API call, and interaction should be logged and reviewable. Set up alerts for unusual patterns, such as unexpected API usage, access to restricted files, and repeated or abnormal command execution.
Network monitoring is equally important. Observing how the agent communicates within your internal network can reveal early signs of misuse or compromise.
Finally, make monitoring a routine, not a reaction. Regular reviews help you detect issues before they escalate and keep your security posture aligned with how your system actually operates. Over time, this visibility becomes one of your strongest defenses, helping you catch issues before they escalate.
OpenClaw security checklist
To keep things practical, here’s a quick checklist you can use to evaluate your setup:
Run OpenClaw in an isolated environment
Bind it to localhost (127.0.0.1) by default
Use dedicated accounts instead of personal ones
Secure and rotate API keys regularly
Protect against prompt injection
Apply strict firewall rules and network controls
Monitor agent activity and logs
Reduce unnecessary integrations to decrease risk
OpenClaw tends to break down through small, overlooked gaps, so tightening each layer is what keeps your environment predictable and secure.
Strengthen AI security with NordLayer
As tools like OpenClaw become part of everyday workflows, securing the environment around them becomes just as important as configuring the tool itself.
NordLayer helps organizations secure environments where OpenClaw is used with network-level controls. Through integrations with identity providers, teams can manage access to sensitive resources with Single Sign-On (SSO), multi-factor authentication (MFA), automated user provisioning, and Device Posture Security, which ensures that only compliant devices can connect.
With the Cloud Firewall feature, organizations can apply granular access controls and support network segmentation to reduce exposure and keep critical systems isolated. NordLayer also gives IT teams better visibility into connected users, devices, and access activity across the environment.
As AI agents take on more responsibility, security needs to be built into the way systems connect, communicate, and operate.

Agnė Srėbaliūtė
Senior Creative Copywriter
Agne is a writer with over 15 years of experience in PR, SEO, and creative writing. With a love for playing with words and meanings, she crafts content that’s clear and distinctive. Agne balances her passion for language and tech with hiking adventures in nature—a space that recharges her.