Summary: Healthcare teams must balance remote access with strict HIPAA compliance. Our guide explains how to secure ePHI while empowering your healthcare teams.
Healthcare providers must balance granting their teams and third-party vendors remote access with complying with the Health Insurance Portability and Accountability Act (HIPAA). This can be a challenge, as attackers usually target Protected Health Information (PHI) for identity theft, insurance fraud, and other financial crimes.
Standard telemedicine remote software often lacks robust security, which makes data more vulnerable to exploitation. In this guide, we’ll discuss how secure remote access solutions protect patient privacy, support clinical workflows, and help comply with the HIPAA Security Rule.
Why healthcare needs HIPAA-compliant remote access
As healthcare professionals work either from home or off-site locations, the traditional security perimeter has dissolved. This change has caused risks, such as data breaches, phishing attacks, and HIPAA violations, to skyrocket. And while the healthcare industry has always been a target for hackers, it is now the primary one. For 14 consecutive years, the industry has suffered the highest average breach costs, reaching $7.42 million per incident in 2025.
To mitigate these risks, the HIPAA Security Rule mandates the confidentiality, integrity, and availability of electronic Protected Health Information (ePHI). This applies to all healthcare organizations and their associates. However, achieving HIPAA compliance is often tricky when a healthcare organization lacks adequate remote access solutions.
The problem with legacy remote access solutions
Many healthcare providers still rely on outdated remote access methods like Windows Remote Desktop Protocol (RDP) and traditional VPNs. However, these tools lack the granular access controls, robust encryption, and detailed logging necessary to meet HIPAA regulatory standards.
What’s more, managing remote access for a network of third-party vendors and contractors adds an extra layer of complexity. Fragmented, manual access methods are not only time-consuming but also prone to human error and cyber risks. To remain HIPAA-compliant and maintain efficiency, healthcare organizations now turn to zero-trust solutions that help streamline access management and provide the visibility needed to keep PHI safe without stalling critical healthcare workflows.
The core requirements for HIPAA-compliant remote access
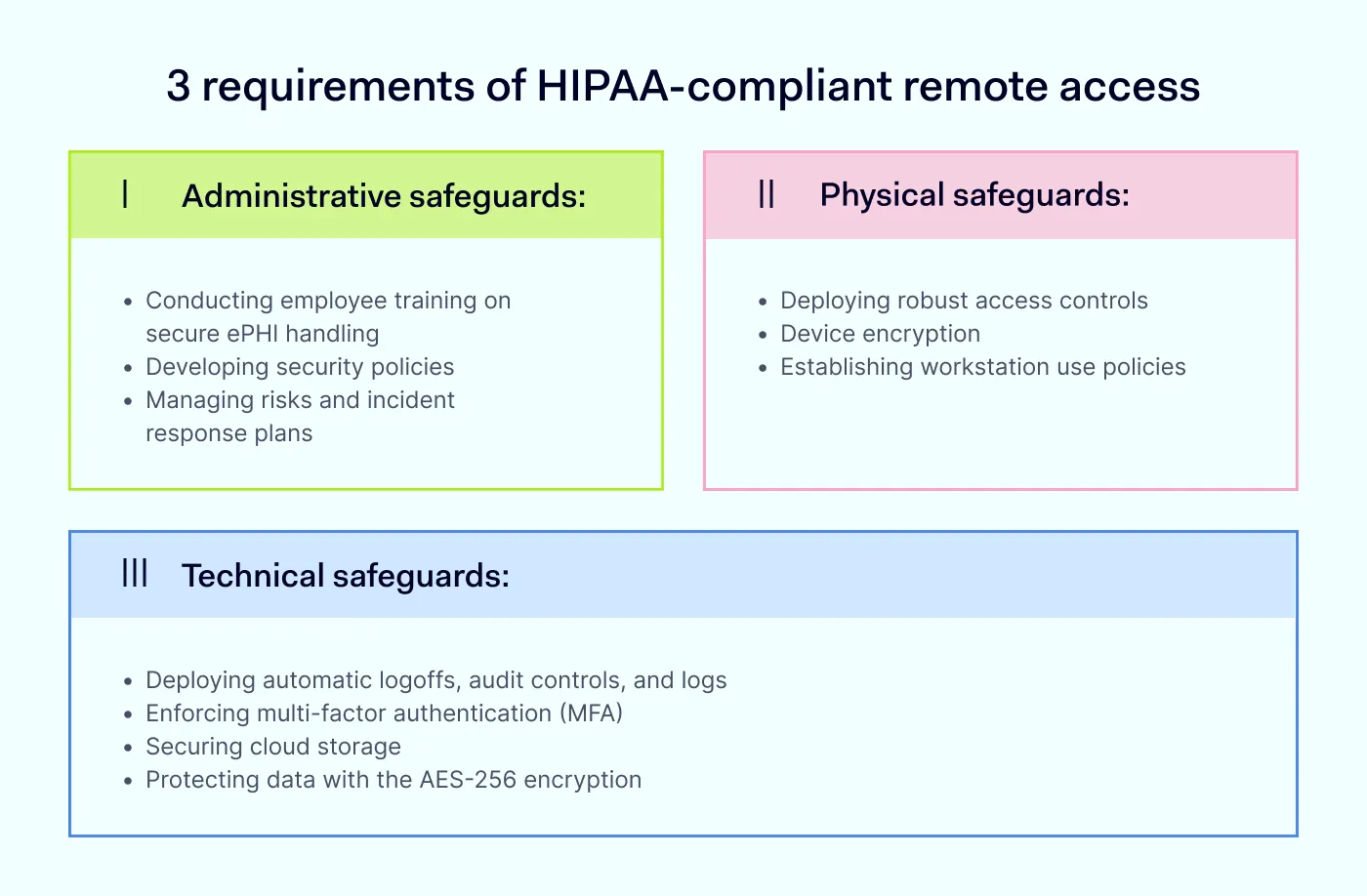
The HIPAA Security Rule states that all healthcare organizations must protect PHI. To be HIPAA-compliant, each healthcare provider must implement 3 categories of safeguards to prevent unauthorized access to ePHI and protect it from threats.
Administrative safeguards address the human aspect of security. Organizations must:
Conduct regular employee training on secure ePHI handling
Create security policies
Manage risks and incident response plans
Physical safeguards focus on the physical environment and hardware. Requirements include:
Deploying robust access controls
Device encryption
Establishing workstation use policies
Technical safeguards are technology-driven:
Deploying automatic logoffs, audit controls, and logs
Enforcing multi-factor authentication (MFA)
Securing cloud storage
Failure to comply with the HIPAA Security Rule can lead to devastating data breaches and substantial regulatory fines. Depending on the level of culpability, penalties range from $145 to over $2,190 per violation. Aside from the financial cost, organizations also face significant reputational damage and a loss of patient trust.
Related articles

Joanna KrysińskaAug 30, 20247 min read

Joanna KrysińskaOct 10, 20249 min read
Shared responsibility: why business associate agreements (BAAs) matter
HIPAA compliance is a shared responsibility between healthcare organizations and their third-party vendors (business associates). Before handling any patient data, a business associate must sign a mandatory business associate agreement (BAA). A BAA is a contract that requires vendors to protect PHI, report any data breaches, and comply with HIPAA security standards. This ensures full accountability for data security.
A standard BAA outlines 5 key requirements for a third party:
Defines how the vendor can use and disclose ePHI, limiting it only to the specific services provided to the covered entity.
Requires vendors to implement the same administrative, physical, and technical safeguards used by the provider.
Mandates the immediate reporting of any security incident or unauthorized access to ePHI back to the healthcare provider.
Ensures that any agents or subcontractors hired by the vendor also agree to the same strict HIPAA compliance protections.
Requires that, at the end of the contract, all PHI be returned or securely destroyed.
Because BAA agreements are key to securing healthcare operations, many organizations look for vendors that are prepared to enter into these legal commitments. For example, NordLayer offers a HIPAA BAA to customers with annual or longer-term subscription plans. With this agreement in place, an organization can secure its network and maintain HIPAA standards.
How to implement HIPAA-compliant remote access
To successfully roll out a secure remote access strategy, organizations should follow these best practices:
Identity and access management
Centralize identities with single sign-on (SSO) and enforce MFA for every user.
Perform quarterly access reviews to revoke permissions for former employees or inactive contractors.
Device posture and endpoint security
Grant access only to managed, compliant devices that have been verified by endpoint security (EDR/MDM).
Require device encryption and automatic session timeouts on all remote workstations.
Session and network security
Secure or restrict Remote Desktop Protocol (RDP) configurations and avoid direct internet exposure.
Enable remote session auditing specifically for high-risk vendor and administrative access.
Operational rigor
Regularly monitor logs for anomalous activity, such as logins from unknown locations.
Run regular phishing simulations and remote work security drills.
Test your backup restores and document your recovery objectives for critical systems.
Achieve HIPAA-compliant remote access with NordLayer
NordLayer’s HIPAA compliance solutions help organizations support HIPAA compliance and protect electronic Protected Health Information (ePHI). By transitioning from legacy VPNs to secure remote access based on zero-trust principles, healthcare organizations can achieve comprehensive data security with:
Data encryption. PHI is protected with the AES 256-bit or ChaCha20 encryption during transmission.
Granular access control. Every connection is verified, which gives you total control over who accesses your network, cloud platforms, and databases.
Multi-factor authentication (MFA). NordLayer supports MFA and biometric authentication to reduce the risk of unauthorized entry with compromised credentials.
Cloud and SaaS security. Our solutions secure SaaS apps, control access, protect data, and monitor network activity.
Activity monitoring and visibility. Gain vital insights into network access, connection patterns, and device posture.
Ready to simplify your HIPAA journey? Book your demo today to see how you can build a secure, compliant environment for your remote healthcare team.

Joanna Krysińska
Senior Copywriter
Joanna's family has a history in math and engineering, and she has dedicated her life to simplifying complicated technical ideas. She helps people understand how hackers think and how to stay ahead of them by concentrating on the human side of cybersecurity.