Network Access Control (NAC) solutions
Keep unauthorized users and devices outside of your business network.
14-day money-back guarantee
15,000+
Business protected
10 min
Average time to deploy
40+
Global service locations
4.6
Customers happiness
OVERVIEW
What is Network Access Control?
NAC comprises a series of security solutions that expand network visibility and access management via device and user policies. The purpose of NAC is to protect access to corporate networks.

Core NAC capabilities:
Device discovery
Identity-based access
Device posture checks
Network Segmentation
Guest/BYOD workflows
Policy enforcement
Reporting and logs
Integrations (IdP, XDR)
Get NAC features with the Core plan
For a deeper security layer, switch to the Premium and get more advanced tools.
How does NordLayer’s NAC solution work?
Network Access Control (NAC) is a tool that enables the customization of network access according to specific needs, strategies, and infrastructure. It allows administrators to enforce access rules on devices and users, using security protocols for authenticating and authorizing requests, often with third-party tools.
With NAC, you can build a framework to establish secure connections and manage user access to resources based on their roles, ensuring users do not exceed their permissions.
Get a real-time look at how NordLayer protects businesses
Explore features like Custom DNS, a dedicated IP, VPN Split Tunneling, and more, all in real-time with our interactive Control Panel demo.
BUSINESS USE
Why is NAC important for business?
Improved security
NAC authenticates users and devices before they access the network, giving admins visibility into activity and helping stop unauthorized access fast.
Increased visibility
NAC gives you a real-time view of users and devices across your organization, so it’s easier to track access, spot risks, and manage endpoints.
Regulatory compliance
NAC helps support compliance by enforcing access controls and strengthening security across your network under standards such as HIPAA, SOX, and PCI DSS.
USE CASES
Protect your organization with NordLayer NAC solutions
Control access for a hybrid workforce
NAC helps hybrid teams securely access the tools and information they need, whether working from the office or remotely. Administrators can control who connects to the network while keeping company data protected.
Regulate third-party access
Control access for partners, vendors, and third parties. NAC ensures external users only access approved resources, which helps your organization collaborate securely without exposing sensitive systems.
Manage access for short-term contractors and freelancers
Control access for contractors and freelancers. NAC ensures temporary team members can only access approved resources. This way, you protect your network while supporting project-based work.
Protect your network from IoT and unmanaged devices
Unmanaged and IoT devices often lack strong security controls. NordLayer NAC helps identify these devices, limit their access, and isolate them from critical systems to reduce risk across your network.
Secure BYOD access across hybrid teams
With NordLayer, personal devices connect only to approved network resources based on user identity and device security posture, which gives IT teams greater control over access.
FEATURES
NordLayer's multi-layered NAC capabilities
NordLayer provides a range of capabilities designed to work together for stronger network access control. Combine different access control methods to secure your network and manage user and device access more effectively.
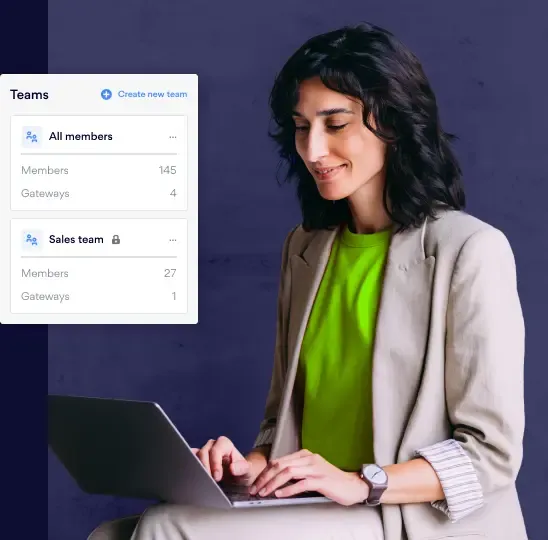
Control by user identity and connections
NordLayer enables robust control based on user identity. It integrates seamlessly with major identity management platforms, like Google Workspace, Entra ID, Okta, OneLogin, and JumpCloud, to support secure user management. It also facilitates:
- Network segmentation. Decide which members and teams can or cannot access the network.
- Authorized access. With single sign-on (SSO), biometric authentication, and multi-factor authentication (MFA) ensure that only the authorized users can access the network.

Control by IP address & gateway
A dedicated server with a fixed IP address, provided by NordLayer, enables organizations to do IP allowlisting. This helps ensure that your work tools and sensitive resources are accessed only through the organization’s Virtual Private Gateways.
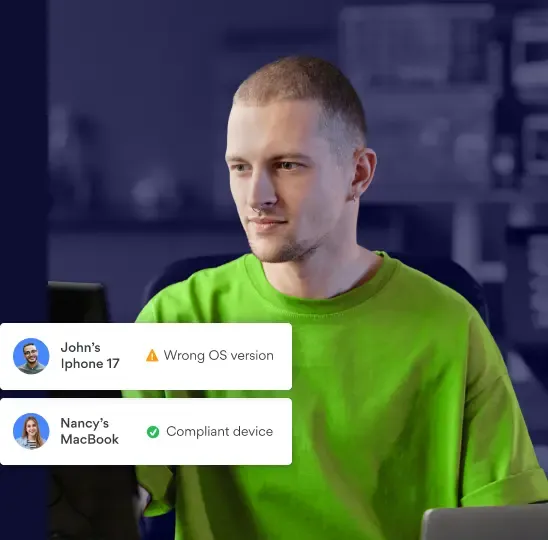
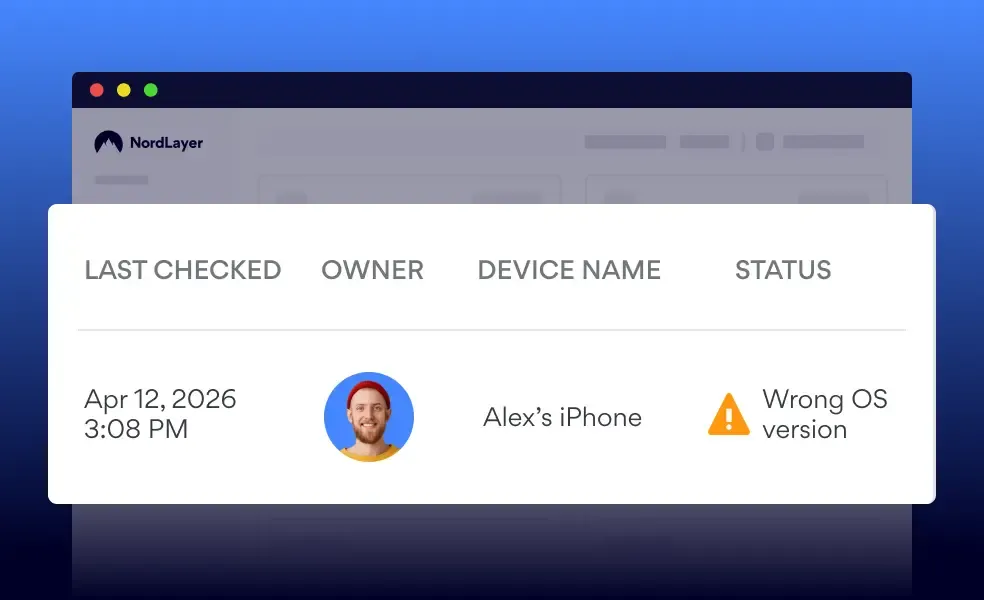
Control by Device Posture Security parameters
Device Posture Security assesses devices based on OS type, version, and even the presence of specific files. Device accounts that are jailbroken (or rooted) or don't align with security requirements are denied access to the network.
Control by the NordLayer app version
NordLayer can also restrict access based on the app version. This ensures that only devices with the latest NordLayer app – equipped with the newest features and in line with all enforced security policies – can access the network.
Control by specific location
Location-based access control is on the horizon. This feature assesses a user’s IP address location before granting network access. If a device’s location isn't on the approved list, its access will be restricted.
INTEGRATIONS
Build your own NAC solutions with NordLayer integrations
NordLayer integrates with tools and platforms you rely on daily, so setup is fast, secure, and frictionless.
Learn more about access control
Access control is a core component of network security. It is the first line of defense against unauthorized access and potential threats. It ensures that only authenticated and authorized users and devices can access network resources, which helps protect sensitive information.
Access Control basics
Learn the fundamentals of access control, why it matters, and how it functions to protect network environments.
Types of Access Control models
Discover access control models such as discretionary, mandatory, and role-based access control.
Access Control best practices
Explore best practices for deploying access control to improve security and manage user permissions.
Protect your business with NordLayer
Let zero trust handle security when it comes to verifying user credentials.
14-day money-back guarantee
Our reputation
Why teams around the world choose NordLayer
In Security Service Edge category
ADDITIONAL INFORMATION
Frequently asked questions
Businesses should adopt Network Access Control solutions to strengthen access control and protect their network infrastructure against cyberattacks, unauthorized access, and malware. NAC also helps flag suspicious activity and unauthorized access attempts so admins can respond quickly.
Implementing NAC starts with defining who and what should be allowed to access your network. In environments with BYOD (Bring Your Own Device) policies, adopting NAC effectively involves using a comprehensive network security solution.. This solution should encompass features that directly contribute to access control and enhanced oversight over the devices accessing the network.
Network Access Control helps mitigate the risk of unauthorized access to the network, which could lead to data theft or leaks, and provides greater visibility for admins to monitor activity, especially in a BYOD setup. Understanding who is accessing the corporate network is key to protecting vital assets, data, and resources from falling into the wrong hands.
There are generally two main strands of NAC, which are both key to fundamental network security::
Pre-admission. Upon receiving a request from a user or device to access the network, pre-admission NAC assesses the attempt and grants entry based on proof of compliance with the network’s security policies – usually through authentication methods like 2FA or biometrics.
Post-admission. If the user or device attempts to access another network area from within, post-admission NAC can restrict movement before further authentication to limit damage from a cyberattack.
NordLayer is an adaptive network security solution that supports both pre-admission and post-admission access controls, designed to ensure only authorized users and endpoints can access specific areas of the business network.
Network Access Control focuses on controlling which users and devices can connect to a network, typically within an internal environment. Zero Trust Network Access (ZTNA) is built on zero-trust security, verifying identity and context every time a user tries to access specific applications or resources, regardless of location. While NAC helps secure network entry points, ZTNA provides more granular, application-level access control for modern distributed environments.


