Summary: DNS traffic connects domain names to IP addresses, enabling browsing but also introducing security risks that require monitoring, filtering, and proper management.
The internet feels instant: type a website name, hit Enter, and the page loads. But behind the scenes, several processes make that possible. One of the most important is DNS traffic.
DNS traffic refers to the exchange of DNS queries and DNS responses between your device and DNS servers, allowing users to access websites without needing to know their underlying IP addresses. Without DNS traffic, the internet would not be user-friendly—you’d have to remember strings of numbers instead of domain names.
So, in the background, DNS traffic ensures every request reaches its intended destination quickly and reliably.
In this guide, we’ll explain what DNS traffic is, how it works, why it matters for security, and how businesses can manage and monitor it effectively.
How DNS traffic works
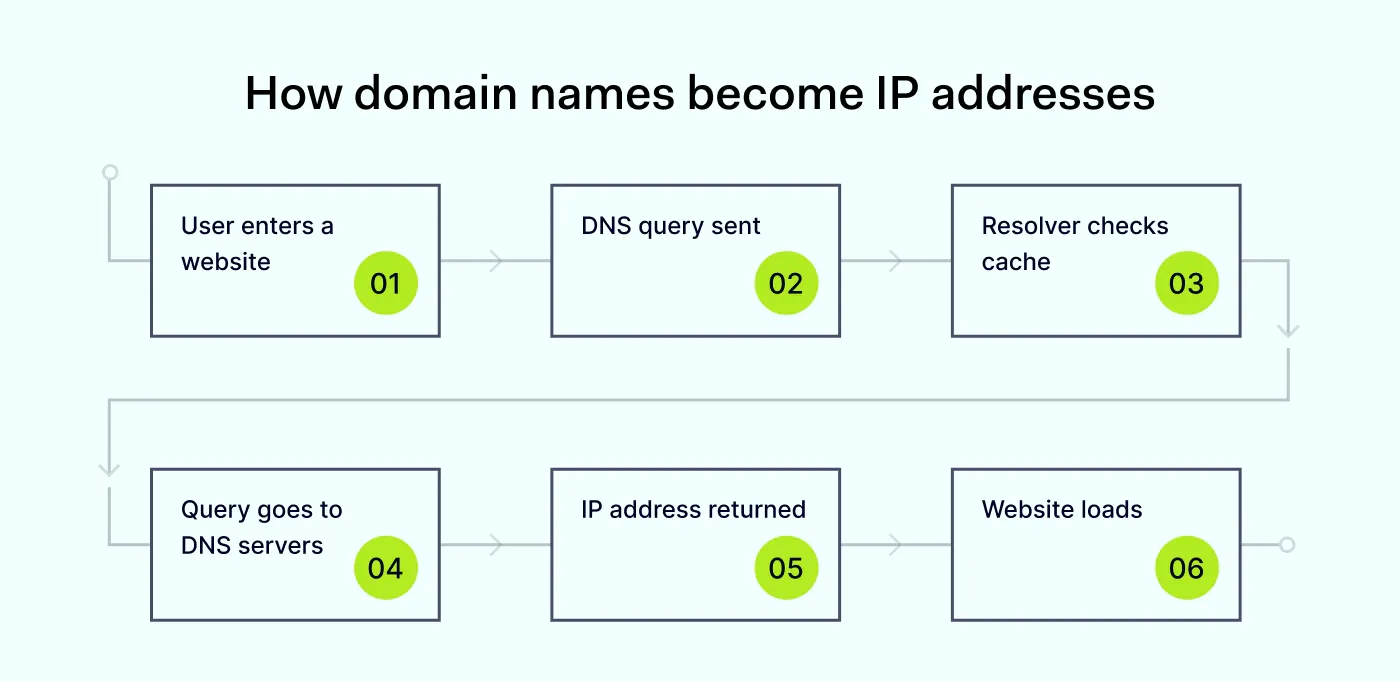
To understand what is DNS traffic, start by looking at how the Domain Name System (DNS) operates step by step. Every time you visit a website, your device sends a lookup request to find the correct destination.
This process relies on a globally distributed network of DNS servers—both public, like Cloudflare or Google, and private, used within organizations—that work together to answer queries efficiently. These servers are designed for high availability. It means that if one server fails or becomes unreachable, another can take over and continue handling traffic without disruption.
Here’s how it goes:
You enter a domain name. You type a website address (like example.com) into your browser.
Your device sends a DNS query. A DNS query is sent to a DNS server (usually provided by your ISP or a third-party service).
The resolver checks its cache. If the server has recently handled the same request, it may already have the IP address stored.
If not cached, the resolver queries other DNS servers. It may contact root servers, TLD servers, and authoritative DNS infrastructure to find the correct information.
The IP address is returned. The correct IP address is sent back as a server reply.
Your browser connects to the website. Using the IP address, your device connects to the server hosting the website.
All of this happens in milliseconds, generating continuous DNS traffic as users browse, stream, and work online. Efficient DNS routing plays a key role here. Requests are often directed to the closest or fastest server available, which reduces latency and improves load times—especially for global services with users in different regions.
Types of DNS traffic
While most users don’t notice it, there are different types of DNS traffic happening behind the scenes:
Recursive queries are requests made by your device to fully resolve a domain name.
Iterative queries are requests in which DNS servers provide partial answers and referrals.
Forward DNS lookups convert domain names into IP addresses.
Reverse DNS lookups map an IP address back to a domain name.
Each type contributes to how efficiently DNS traffic flows across networks.
Secure your network against cyber risks with our DNS filtering
Block malware, phishing & botnet attacks while optimizing connection performance.
What is encrypted DNS traffic, and why it matters
As privacy concerns grow, traditional DNS traffic is being replaced by encrypted traffic.
Normally, DNS queries and responses are sent in plain text. This means they can potentially be intercepted, monitored, or even modified by third parties. Encrypted traffic solves this problem by securing DNS communication between your device and DNS servers, ensuring it remains private and protected.
In simple terms, the Domain Name System still performs the same function of translating a domain into an IP address, but the way that data is transmitted is significantly more secure.
How it works
Encrypted DNS traffic relies on modern protocols that wrap DNS requests in encryption before they leave your device. The most common ones include:
DNS over HTTPS (DoH) sends DNS queries over HTTPS and blends them with regular web traffic, making them harder to distinguish and intercept.
DNS over TLS (DoT) uses an encrypted TLS connection dedicated specifically for DNS traffic to ensure secure communication between your device and DNS servers.
Here’s what changes in practice:
A DNS query is generated as usual when you try to access a website.
Instead of being sent in plain text, the request is encrypted.
The encrypted request is transmitted securely to a DNS resolver.
The DNS server decrypts the request, processes it, and sends back a secure reply.
Your device decrypts the response and connects to the correct IP address.
In many cases, users rely on trusted public resolvers that not only support encrypted DNS but also add additional security layers like threat intelligence and malicious domain blocking. Thanks to encryption, organizations can reduce one of the most overlooked visibility gaps in network security.
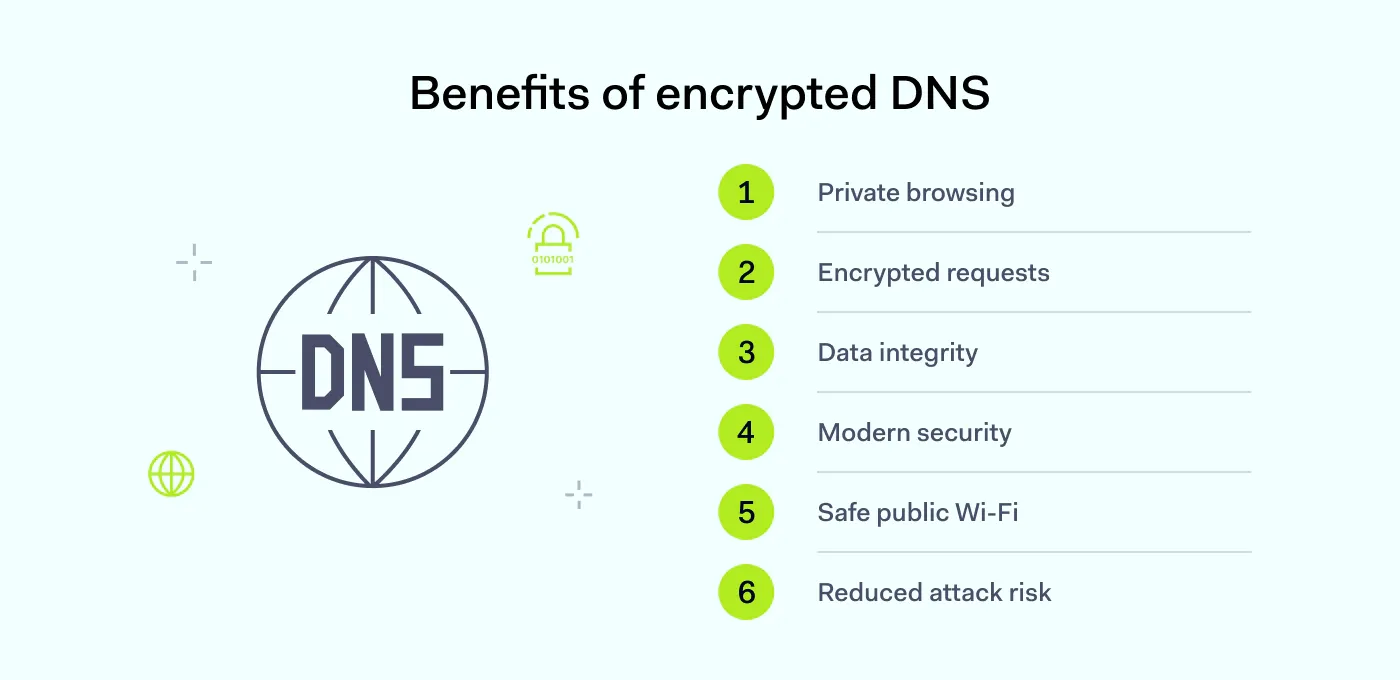
Key advantages of encrypted DNS traffic
Encrypted DNS traffic improves how domain requests are protected in transit, strengthening both privacy and security without changing how users browse. The main advantages of encrypted DNS traffic are as follows:
Improved privacy. Hides domain requests from ISPs, network admins, and attackers, which reduces visibility into user activity.
Protection against interception. Keeps data unreadable if intercepted, lowering the risk of manipulation or redirection to malicious sites.
Data integrity. Ensures DNS responses aren’t altered in transit and that users reach the intended destination.
Alignment with modern security standards. Aligns with current best practices for
secure browsing, similar to how HTTPS secures web traffic.
Safer use of public networks. Adds protection to unsecured Wi-Fi networks, making monitoring and tampering more difficult.
Reduced risk of DNS-based attacks. Limits exposure to threats like
DNS spoofing, hijacking, and DNS tunneling.
However, balancing privacy with control is key in business environments, and sometimes it needs specific measures—even blocking encrypted DNS.
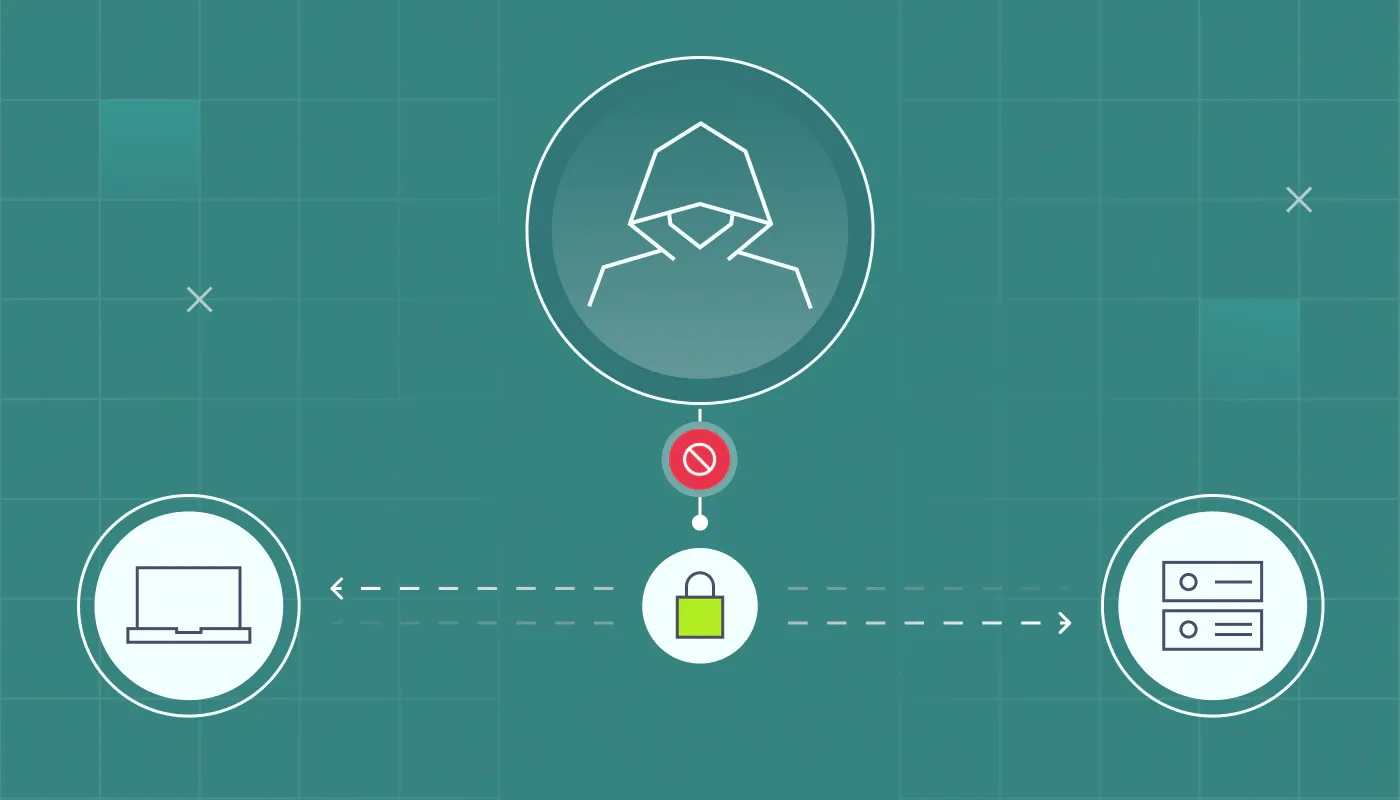
What is DNS traffic blocking?
DNS traffic blocking is a security technique used to prevent access to specific domains by stopping domain lookups before a connection is established.
Instead of allowing a DNS request to resolve a domain, the system blocks it, effectively stopping the user from reaching the destination. This makes DNS traffic blocking one of the earliest and most efficient ways to stop threats, since it acts before any data exchange with a potentially harmful server takes place.
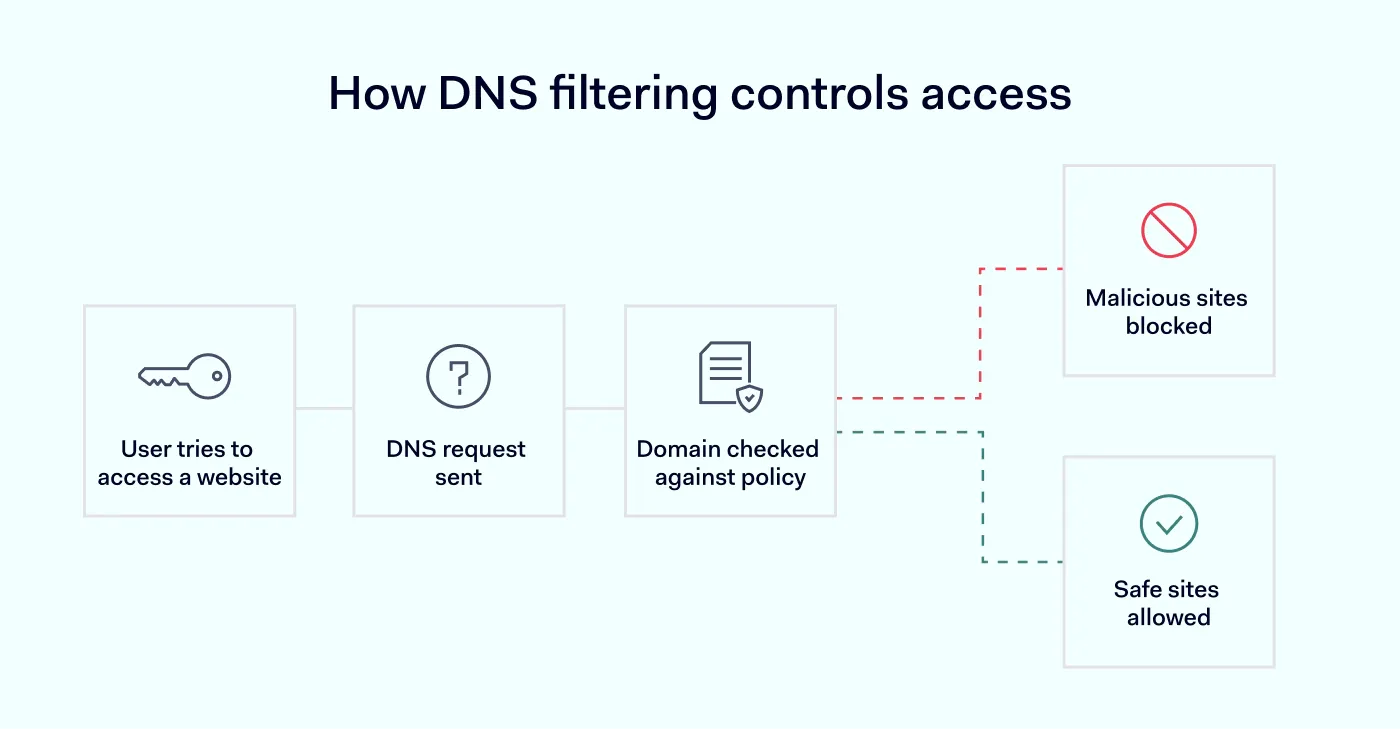
How DNS filtering blocks traffic
DNS traffic blocking typically relies on DNS filtering, which inspects and controls DNS queries in real time. Here’s how the process works step by step:
A user attempts to access a website. The process begins when the user enters a domain name into their browser or clicks on a link.
A DNS query is generated. The device sends a DNS query to resolve the domain name into an IP address via configured DNS resolvers.
The query is intercepted by a DNS filtering system. Instead of going directly to a public resolver, the request is routed through a DNS filtering service that is part of the organization’s DNS traffic management strategy.
The domain is checked against filtering policies. The system compares the requested domain against predefined rules, which may include blacklists (malicious sites), category-based restrictions (e.g., gambling, social media), or custom company policies.
A decision is made (allow or block):
If the domain is safe and allowed, the DNS request proceeds normally, and the correct IP address is returned.
If the domain is flagged, the request is blocked before resolution.
A modified DNS response is returned. Rather than receiving the real IP address, the user receives an altered reply—often leading to a warning page or an error message.
The connection is prevented. Since the domain never resolves to a valid IP address, the device cannot establish a connection, effectively stopping access at the DNS level.
This approach stops threats before a connection is ever established, reducing exposure from the start.
Benefits of DNS traffic blocking
DNS traffic blocking helps organizations control access to online resources, improving security, compliance, and day-to-day operations. It acts as an early control point, stopping unwanted connections before they reach the network. Key benefits include:
Prevents access to malicious domains. Stops users from connecting to known malicious domains by blocking harmful DNS requests early. This helps prevent malware, ransomware, and command-and-control activity before they start.
Reduces phishing risks. Blocks access to known
phishing domains that rely on deceptive URLs. Even if a user clicks on a malicious link, the connection is prevented, adding protection beyond that of email security tools.
Improves productivity. Limits access to non-work-related websites like streaming or gaming platforms. This reduces distractions and helps optimize bandwidth usage across the organization.
Supports compliance. Enforces access controls and restricts non-compliant or risky content. DNS activity logs also provide an audit trail for regulatory reporting and internal policies.
DNS traffic blocking is often a core part of DNS traffic management. It helps organizations control how users interact with the internet while strengthening security at a foundational level.
Why organizations sometimes restrict encrypted DNS
While encryption improves privacy, organizations sometimes need to control or limit it, especially when it bypasses security tools. This is often referred to as blocking encrypted DNS. Here’s why:
Loss of visibility. Encrypted DNS traffic can hide DNS activity, making it harder to detect threats or suspicious behavior.
Bypassing security controls. Users may use external DNS services that bypass internal filtering policies and DNS traffic blocking.
Increased risk of data exfiltration. Techniques like DNS tunneling can use encrypted channels to transfer sensitive data unnoticed.
Compliance requirements. Some industries require monitoring of network activity, including DNS traffic, for regulatory reasons.
Centralized control challenges. Organizations rely on managed DNS servers to enforce policies. However, encrypted DNS can bypass these controls.
Because of these risks, companies often implement strategies to manage or selectively restrict encrypted DNS traffic while still protecting user privacy.
Related articles

Agnė SrėbaliūtėMay 3, 202410 min read

Agnė SrėbaliūtėApr 12, 202418 min read
How to monitor DNS traffic
Monitoring DNS traffic helps teams detect suspicious activity early and keep control over how users access the internet. Because DNS-based activity is often one of the first indicators of suspicious behavior, monitoring it can help organizations detect threats earlier than traditional security tools alone.
Key steps to monitor DNS traffic
Use centralized DNS servers. Route all DNS requests through managed DNS servers to maintain visibility and enforce policies.
Enable logging and analytics. Track DNS activity to identify unusual patterns or suspicious domains.
Apply DNS traffic management policies. Define rules for allowed and blocked domains to reduce risk.
Detect anomalies and threats. Look for signs of malware communication, unusual traffic spikes, or DNS tunneling attempts.
Integrate with security tools. Combine DNS monitoring with
SIEM or
threat detection systems for better insights.
Monitor DNS queries and responses
Analyzing DNS requests and DNS responses helps identify:
Suspicious domains
Repeated failed lookups
Unexpected traffic destinations
Identify risky behavior
Patterns such as frequent lookup attempts to unknown domains or unusual traffic timing may indicate compromised devices or insider threats. Spikes in traffic to rarely used domains, for example, can often signal the early stages of an attack, making DNS monitoring a valuable detection mechanism.
Strengthen DNS security with NordLayer
Understanding what DNS traffic is is key to understanding how the internet works—and how to secure it. DNS traffic determines how users reach online services, from resolving domain names to enabling secure browsing. Yet, it also introduces risks that need to be managed carefully.
Managing DNS traffic doesn’t have to be complex. With the right tools, organizations can gain visibility, enforce policies, and improve security without disrupting users. NordLayer enables organizations to:
Control and filter DNS traffic in real time with
DNS Filtering by category that blocks harmful and unwanted domains.
Block malicious domains before connections are established by preventing access to known harmful websites at the DNS level.
Improve visibility into DNS activity, connections, devices, and user behavior with
Network Visibility.
Strengthen overall DNS traffic management with additional features like
Cloud Firewall for traffic control.
Reduce risks like phishing and DNS tunneling by limiting access to suspicious or high-risk domains and enforcing security policies.
By combining performance, security, and visibility, organizations can turn DNS traffic from a background process into a powerful layer of proactive defense within their broader internet access security strategy.

Agnė Srėbaliūtė
Senior Creative Copywriter
Agne is a writer with over 15 years of experience in PR, SEO, and creative writing. With a love for playing with words and meanings, she crafts content that’s clear and distinctive. Agne balances her passion for language and tech with hiking adventures in nature—a space that recharges her.